Ring Network Topology
Ring Network Topology Diagram
A network topology in which each of the nodes connects to two other nodes, resulting in forming a continuous pathway for the signals through each of the nodes known to be called the “rings”, is known to be called as a “ring network”. Data within such networks is known to be traveling from one node to another node, through all the nodes one by one along its way handling every single packet. The mentioned “rings” can be “unidirectional”, having all its traffic travelling clockwise or anticlockwise all the way around the ring. Also, it can be the so called “bidirectional”, providing only one single pathway between two nodes out of many other nodes. A unidirectional ring network is known to be very likely disrupted by the failure of some link appearing to be nearby.
A node failure as well as any cable break may lead to isolation of every single node, which is attached to the “ring”. Some of the ring networks are known to be adding a so called "counter-rotating ring", also known to be called a “C-Ring”. Adding the mentioned ring can be done for forming a redundant topology. Thus, once break happens, a data may get wrapped back on the ring before it reaches the end of the cable. Such data is known to be maintaining a path to every single node all the way along the resulting counter-rotating ring.
The "dual ring" networks are known to be including the so called “Spatial Reuse Protocol”, as well as the “Fiber Distributed Data Interface”, or “FDDI”, and the “Resilient Packet Ring”. The well-known “IBM token ring networks” are also sometimes called as the “802.5 networks”. They are commonly used for avoiding all the possible and existing weakness of a ring topology by using another topology — a “star” one. Such mentioned topology is usually used at the physical layer for imitating a ring at the so called “data link layer”.
Some of the previously mentioned “SONET/SDH rings” have two sets of the bidirectional links, which can be found between the nodes, allowing the failures or maintenance at the multiple points of the same ring resulting in no loss of the primary traffic on the outer ring in a way of switching the traffic on the inner ring after the so called “failure points”.
One of the advantages of using such network topology can be mentioned the convenience of using it for performing in a better way than a bus topology does, especially in the cases of the need of loading under the so called “heavy network”. The mentioned network topology is known to be used within a very orderly network having every device accessing to the “token” having the opportunity to transmit. Such ring network topologies do not require any central nodes for managing the connectivity between different computers. Because of such point to point line configuration of devices with a device on another side, it is quite simple to install as well as to re-configure whatever is needed by removing or adding any device.
Another special feature of the ring network topologies is its “point to point” line configuration, which makes it much simpler to isolate all the previously identified faults. Also, the reconfiguration for line faults of bidirectional rings in ring network topology can be very fast, having all the switching happening at the highest level, leading to the traffic not requiring any individual re-routing.
The disadvantages of the ring network topology: first of all, it is always more difficult to configure using it to compare to using a “star” one as any node adjunction equals to the ring reconfiguration and shutdown. One of the malfunctioning workstations within the ring network topology can create lots of problems for all the network. This can be solved by using a switch or a dual ring used for closing off the break. Every time there’s some moving, changing and adding the devices can affect the entire ring network and the communication delay is known to be directly proportional to the number of all the existing nodes in the ring network.
It is important to remember that any ring network may afford the so called “fault tolerance” to the telecommunication network having two paths between any two nodes on the network. Ring protection is known to be a system commonly used for assuring any needed communications, continuing in the event of failure of only one path. The most widely used protection architectures are “1+1” as well as “1:1”.
In 1+1 architecture, every single protection path is known to be used for protecting the signal having the bridge at the head of the path on a permanent basis, while the switching occurs at its tail end. There are more than two parallel routes are sent in this architecture traffic and the receiving end is known to be selecting the better of the mentioned two signals. Once some failure occurs, the destination switches into one of the alternative paths. The mentioned architecture is quite a widely used for as it is simple for implementing, resulting quite fast restoration. Although, there’s still a drawback, which is the wastage of the bandwidth, occurring for a reason of no traffic traveling through the redundant path.
Pic. 1. Ring Network Topology
Drawing the ring network topology diagrams taking into consideration any of the mentioned architectures can be always much simpler using a professional software for completing such tasks. One of the best applications nowadays is ConceptDraw DIAGRAM one, enabling all its users to create a great looking diagram, such as a ring network topology one, especially having the Computer and Networks solution downloaded from ConceptDraw STORE application.
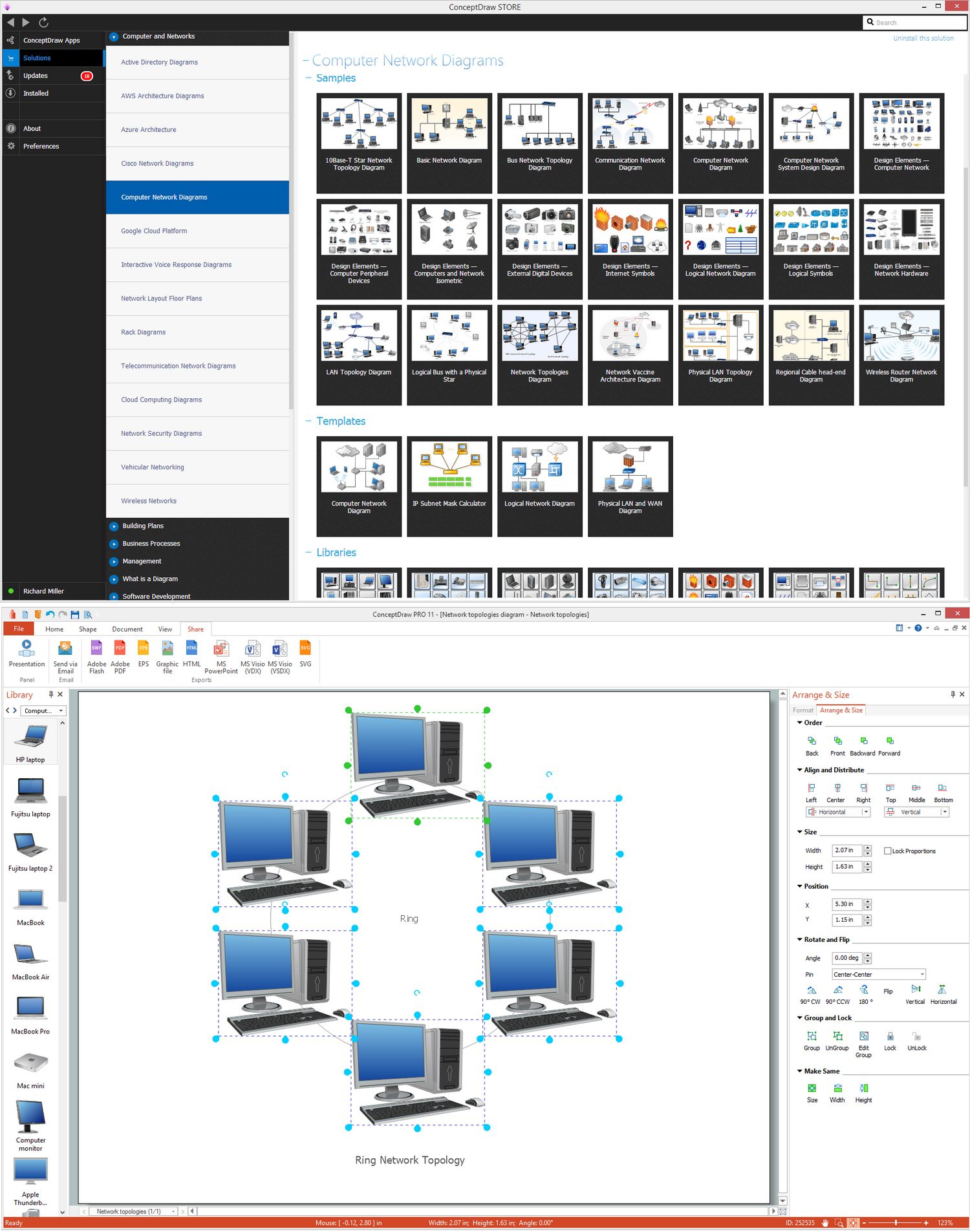
Pic. 2. Ring Network Topology Diagram
Having the ConceptDraw DIAGRAM software means having all the needed tools for making smart looking drawings, at the same time having the ConceptDraw STORE which is meant to be used while working in ConceptDraw DIAGRAM means simplifying your work with creating such diagrams by using the previously developed solutions full of the stencil libraries with the design symbols depending on the subject of your drawing.
See Also Network Topologies:
- Bus Network Topology
- Star Network Topology
- Mesh Network Topology
- Tree Network Topology
- Fully Connected Network Topology
TEN RELATED HOW TO's:Use the libraries from the Block Diagrams solution to draw block diagrams for your business documents, presentations and websites in a few minutes. Picture: Block DiagramRelated Solution:If you are an advanced diagramming software user, you might use it daily. Traversing the Internet in searching of alternative to MS Visio for MAC and PC, you can fulfill all your requirements with ConceptDraw DIAGRAM. Don’t hesitate to transfer your documents to another operating system. When looking for a smart and simple tool for business diagrams as alternative to MS Visio for Apple OS X platform, ConceptDraw DIAGRAM certainly is the best choice. Making many kinds of business charts, numerous technical drawings is what ConcepDraw DIAGRAM is the best. One can easy create any diagram and complete it perfectly and quickly. The big collection of vector object libraries, templates and samples, make it the best Microsoft Visio alternative: ConceptDraw DIAGRAM is simpler to use, less expensive, and supports project management and mind mapping methods.
Picture: Block DiagramRelated Solution:If you are an advanced diagramming software user, you might use it daily. Traversing the Internet in searching of alternative to MS Visio for MAC and PC, you can fulfill all your requirements with ConceptDraw DIAGRAM. Don’t hesitate to transfer your documents to another operating system. When looking for a smart and simple tool for business diagrams as alternative to MS Visio for Apple OS X platform, ConceptDraw DIAGRAM certainly is the best choice. Making many kinds of business charts, numerous technical drawings is what ConcepDraw DIAGRAM is the best. One can easy create any diagram and complete it perfectly and quickly. The big collection of vector object libraries, templates and samples, make it the best Microsoft Visio alternative: ConceptDraw DIAGRAM is simpler to use, less expensive, and supports project management and mind mapping methods. Picture:In Searching of Alternative to MS Visio for Mac and PCwith ConceptDraw DIAGRAMThe reliability is a cornerstone for any corporate computer network. If you want to provide a high fault tolerance, a mesh network topology would be the solution. The main advantage of this network is that every node can work as a commutator, although it’s not easy to set up this kind of network. A mesh network topology may be full, or partial. Full mesh network means that each node of the network (computer, workstation or other equipment) is connected directly to each of the other nodes. A partial mesh topology means that a part of nodes are connected with a whole network, and the other part of nodes are only connected to those equipment, they exchange the majority of data. This illustration shows schematic diagram of a partial mesh network containing six nodes. Each node is represented as a circles and connections are drawn as straight lines. The connections may be both wired and wireless. This scheme can be used to make the specific logical or physical network diagrams by means the ConceptDraw Computer and Networks solution.
Picture:In Searching of Alternative to MS Visio for Mac and PCwith ConceptDraw DIAGRAMThe reliability is a cornerstone for any corporate computer network. If you want to provide a high fault tolerance, a mesh network topology would be the solution. The main advantage of this network is that every node can work as a commutator, although it’s not easy to set up this kind of network. A mesh network topology may be full, or partial. Full mesh network means that each node of the network (computer, workstation or other equipment) is connected directly to each of the other nodes. A partial mesh topology means that a part of nodes are connected with a whole network, and the other part of nodes are only connected to those equipment, they exchange the majority of data. This illustration shows schematic diagram of a partial mesh network containing six nodes. Each node is represented as a circles and connections are drawn as straight lines. The connections may be both wired and wireless. This scheme can be used to make the specific logical or physical network diagrams by means the ConceptDraw Computer and Networks solution.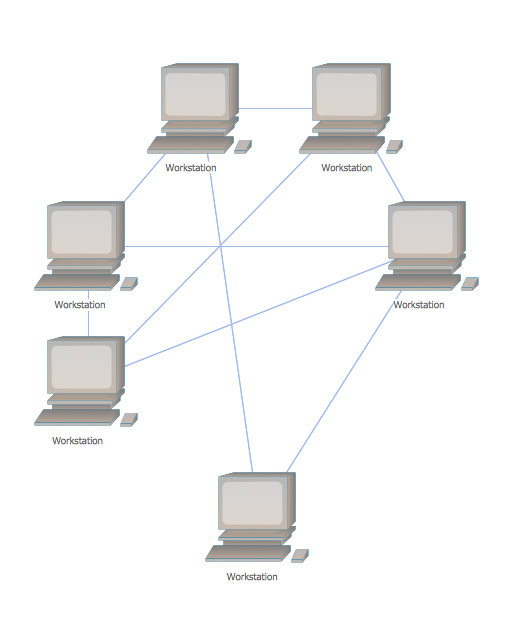 Picture: Mesh Network Topology DiagramRelated Solution:No security system cannot be constructed without detailed security plan, or even a set of plans in some cases. ConceptDraw DIAGRAM software offers the Security and Access Plans Solution from the Building Plans Area to help you design the Security Plans for any premises and of any complexity.
Picture: Mesh Network Topology DiagramRelated Solution:No security system cannot be constructed without detailed security plan, or even a set of plans in some cases. ConceptDraw DIAGRAM software offers the Security and Access Plans Solution from the Building Plans Area to help you design the Security Plans for any premises and of any complexity.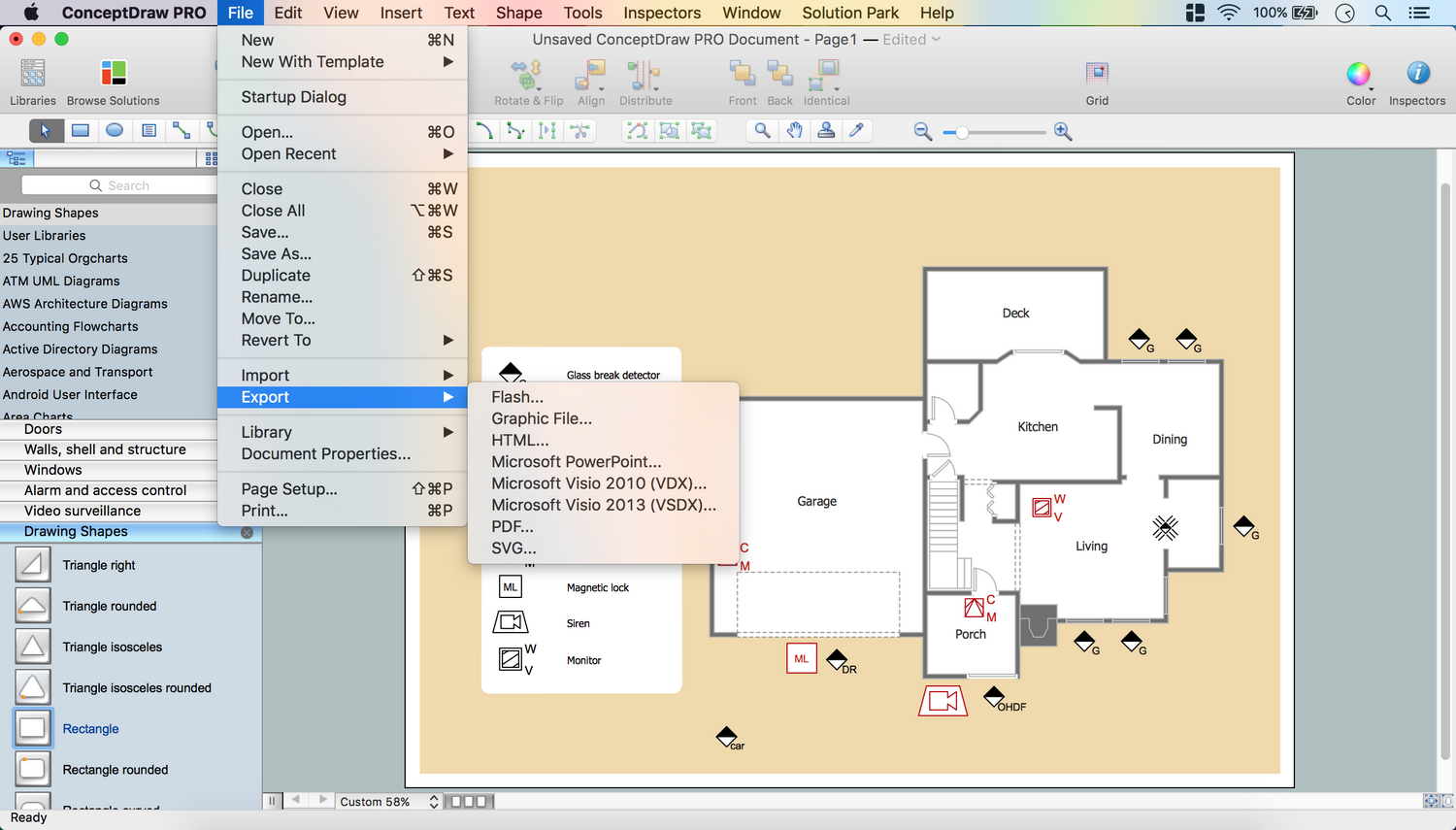 Picture: Security PlansRelated Solution:Creation of well thought-out network security model will effectively help you in realization your network's security. ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.
Picture: Security PlansRelated Solution:Creation of well thought-out network security model will effectively help you in realization your network's security. ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.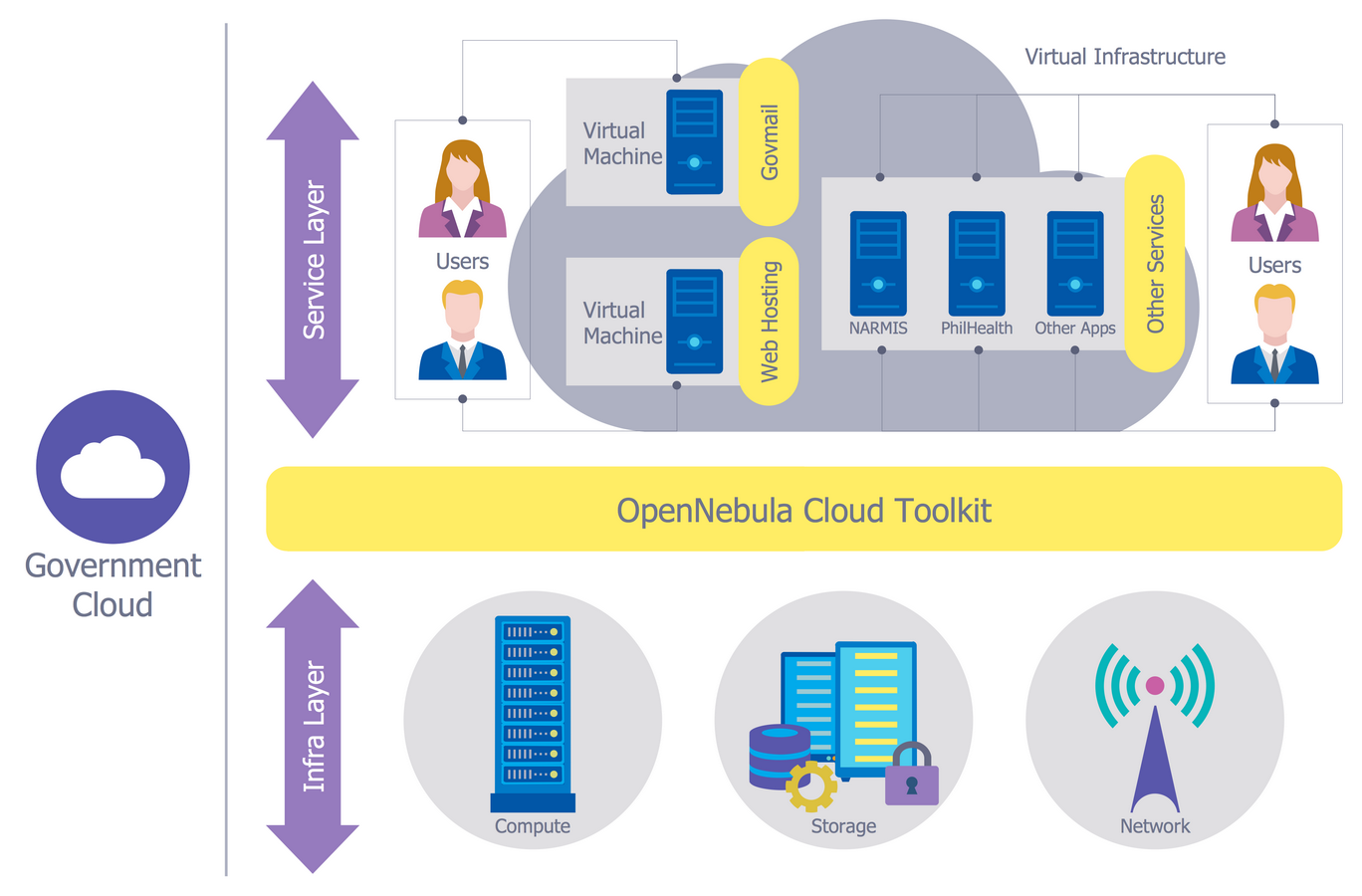 Picture: Network Security ModelRelated Solution:Nodes of any computer network are somehow organized in a hierarchy or a layout. Some of the common layouts like star network topology are more reliable and some like ring topology withstand high loads better. It is also important to distinguish logical topologies from physical. This diagram represents a typical view of the star network topology. The star network topology is one of the most frequently used network topologies in the majority of office and home networks. It is very popular because of its low cost and the easy maintenance. The plus of the star network topology is that if one computer on the local network is downed, this means that only the failed computer can not send or receive data. The other part of the network works normally. The minus of using star network topology is that all computers are connected to a single point-switch, or hub. Thus, if this equipment goes down, the whole local network comes down.
Picture: Network Security ModelRelated Solution:Nodes of any computer network are somehow organized in a hierarchy or a layout. Some of the common layouts like star network topology are more reliable and some like ring topology withstand high loads better. It is also important to distinguish logical topologies from physical. This diagram represents a typical view of the star network topology. The star network topology is one of the most frequently used network topologies in the majority of office and home networks. It is very popular because of its low cost and the easy maintenance. The plus of the star network topology is that if one computer on the local network is downed, this means that only the failed computer can not send or receive data. The other part of the network works normally. The minus of using star network topology is that all computers are connected to a single point-switch, or hub. Thus, if this equipment goes down, the whole local network comes down.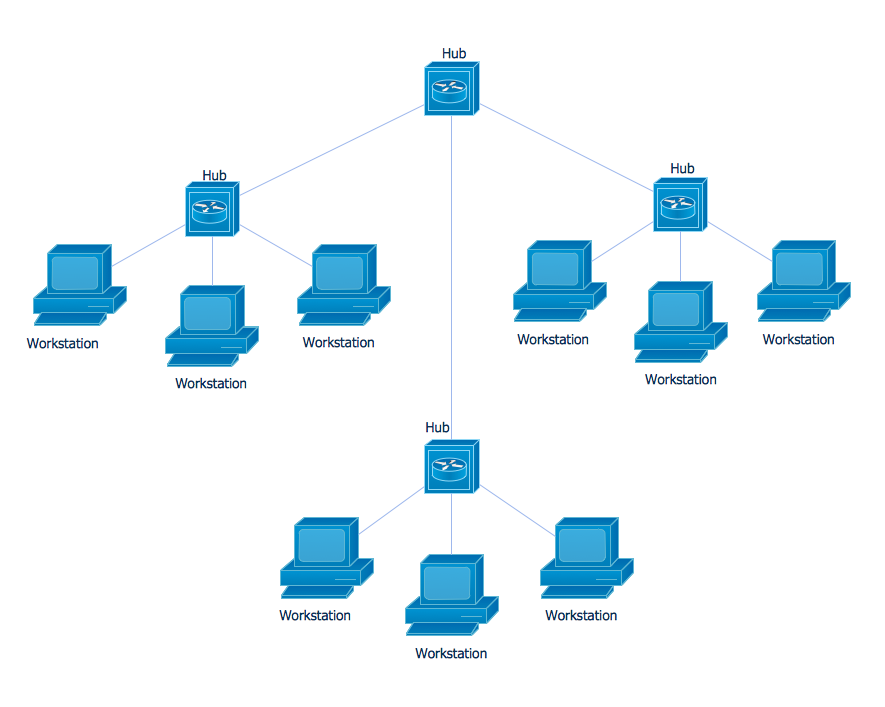 Picture: Star Network TopologyRelated Solution:All of the needed tools for that, including the field objects, were designed in accordance with the real field dimensions and they all can be found in the solution, as well as the corner view template and many other samples.
Picture: Star Network TopologyRelated Solution:All of the needed tools for that, including the field objects, were designed in accordance with the real field dimensions and they all can be found in the solution, as well as the corner view template and many other samples. Picture:Baseball DiagramBaseball Field – Corner View – TemplateRelated Solution:Computer networks nowadays are spread all across the world. The large number of parameters, such as geographic scale or communication protocols, can divide networks. One of the most common types of networks is called local area network (LAN). It convenient to represent network examples by means of diagrams. This local area network (LAN) diagram provides an easy way to see the way the devices in a local network are interacted. The diagram uses a library containing specific symbols to represent network equipment , media and the end-user devices such as computers (PC, mac, laptop) , network printer, hubs, server and finally a modem. There are two types of network topologies: physical and logical. The current diagram represents precisely a physical type of LAN topology because it refers to the physical layout of a local network equipment.
Picture:Baseball DiagramBaseball Field – Corner View – TemplateRelated Solution:Computer networks nowadays are spread all across the world. The large number of parameters, such as geographic scale or communication protocols, can divide networks. One of the most common types of networks is called local area network (LAN). It convenient to represent network examples by means of diagrams. This local area network (LAN) diagram provides an easy way to see the way the devices in a local network are interacted. The diagram uses a library containing specific symbols to represent network equipment , media and the end-user devices such as computers (PC, mac, laptop) , network printer, hubs, server and finally a modem. There are two types of network topologies: physical and logical. The current diagram represents precisely a physical type of LAN topology because it refers to the physical layout of a local network equipment.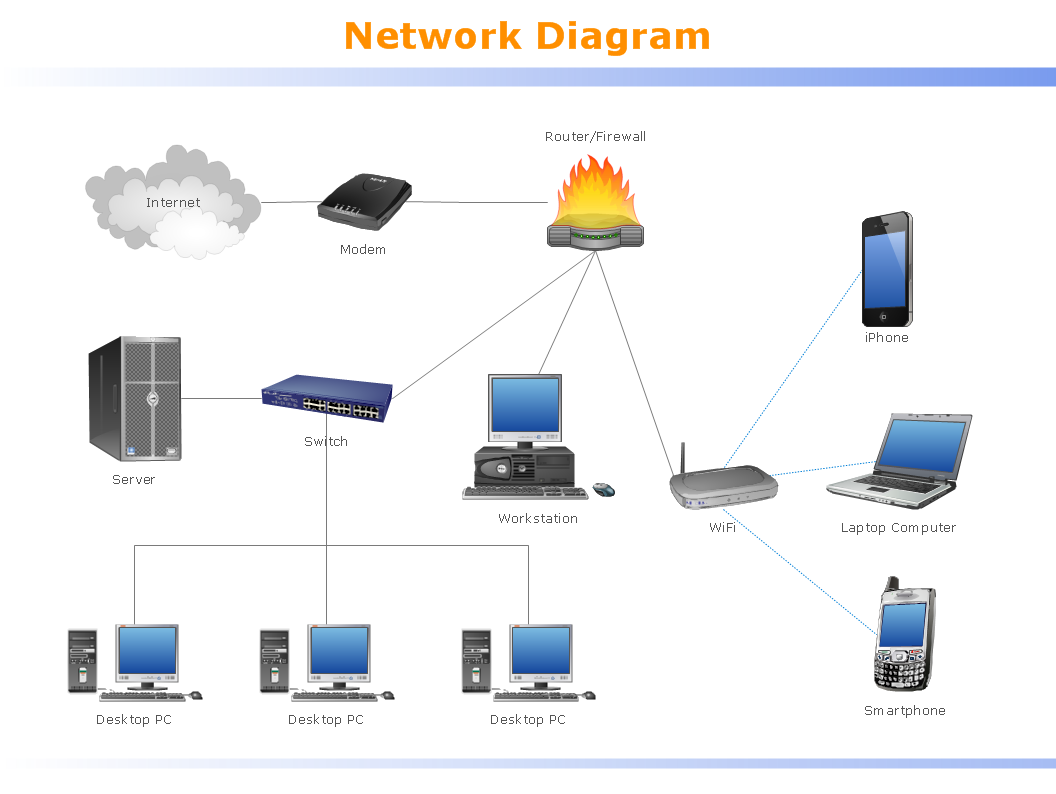 Picture:What is a Local Area Network?Examples of LAN DiagramsRelated Solution:In general, you can use any icons to represent network equipment on a diagram. However, there are some icons, for instance, Cisco icons, shapes, stencils and symbols, that are recognizable worldwide. Using those icons you can create Cisco network topology diagrams in minutes and share them anywhere. The icons depicting Cisco network equipment are recognized and generally applied as standard images for designing network diagrams. They are free to used , but can not be reworked. Cisco network diagrams are created to depict how signals processed on the network equipment and end-user computers and how data transfer through LAN or WLAN between nodes. The vector graphic library of ConceptDraw CISCO Network Diagrams solution includes about 90 icons of Cisco network equipment for designing computer network diagrams with ConceptDraw DIAGRAM.
Picture:What is a Local Area Network?Examples of LAN DiagramsRelated Solution:In general, you can use any icons to represent network equipment on a diagram. However, there are some icons, for instance, Cisco icons, shapes, stencils and symbols, that are recognizable worldwide. Using those icons you can create Cisco network topology diagrams in minutes and share them anywhere. The icons depicting Cisco network equipment are recognized and generally applied as standard images for designing network diagrams. They are free to used , but can not be reworked. Cisco network diagrams are created to depict how signals processed on the network equipment and end-user computers and how data transfer through LAN or WLAN between nodes. The vector graphic library of ConceptDraw CISCO Network Diagrams solution includes about 90 icons of Cisco network equipment for designing computer network diagrams with ConceptDraw DIAGRAM.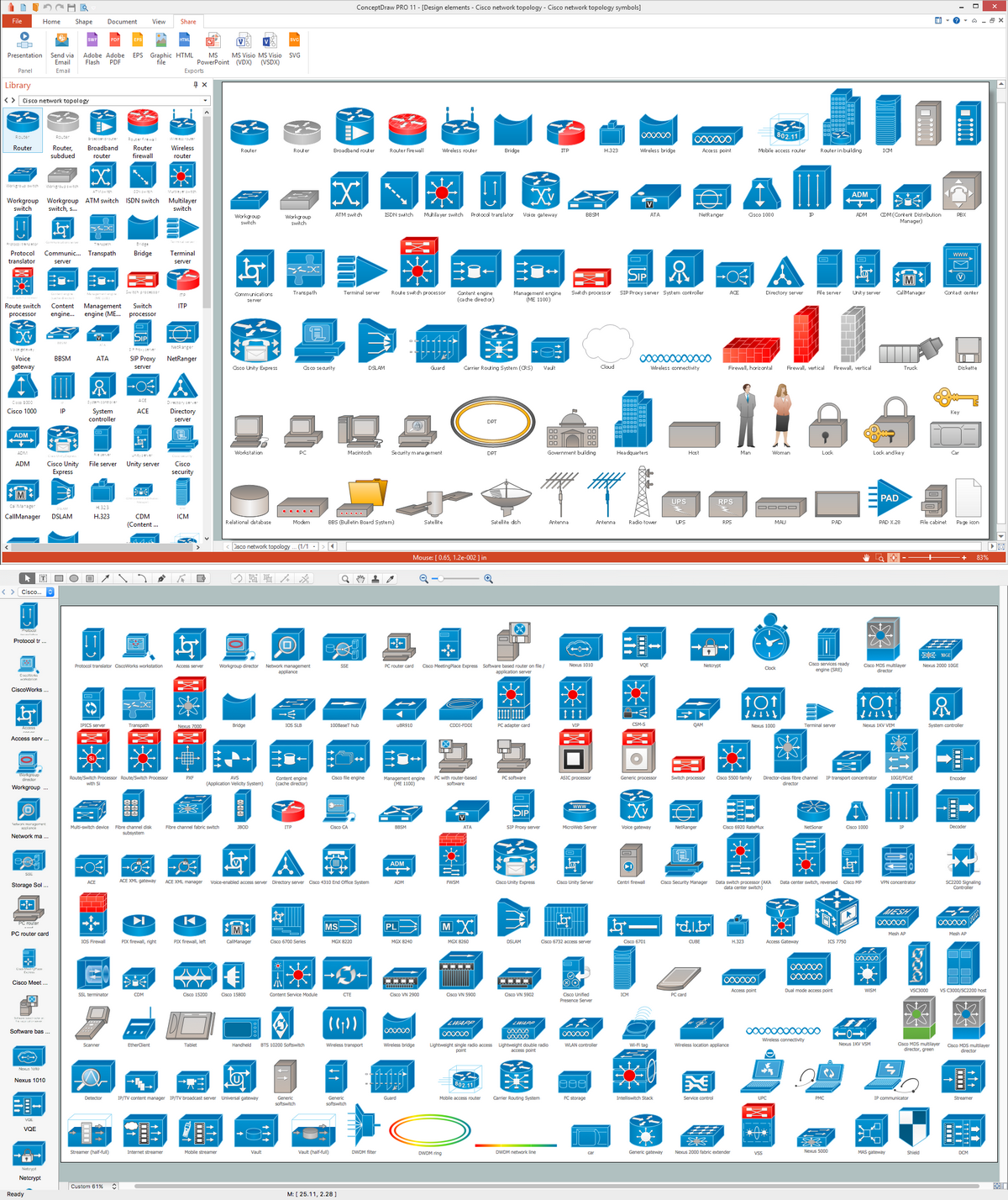 Picture: Cisco Network Topology. Cisco icons, shapes, stencils and symbolsRelated Solution:Multiprotocol Label Switching (MPLS) is a mechanism in high-performance telecommunication networks that implements the data transfer from one network node to another using the labels. ConceptDraw DIAGRAM is a powerful network diagramming and vector drawing software that provides the Computer and Networks solution with wide set of ready-to-use predesigned vector stencils and examples to help you design the MPLS Networks quick and easy.
Picture: Cisco Network Topology. Cisco icons, shapes, stencils and symbolsRelated Solution:Multiprotocol Label Switching (MPLS) is a mechanism in high-performance telecommunication networks that implements the data transfer from one network node to another using the labels. ConceptDraw DIAGRAM is a powerful network diagramming and vector drawing software that provides the Computer and Networks solution with wide set of ready-to-use predesigned vector stencils and examples to help you design the MPLS Networks quick and easy.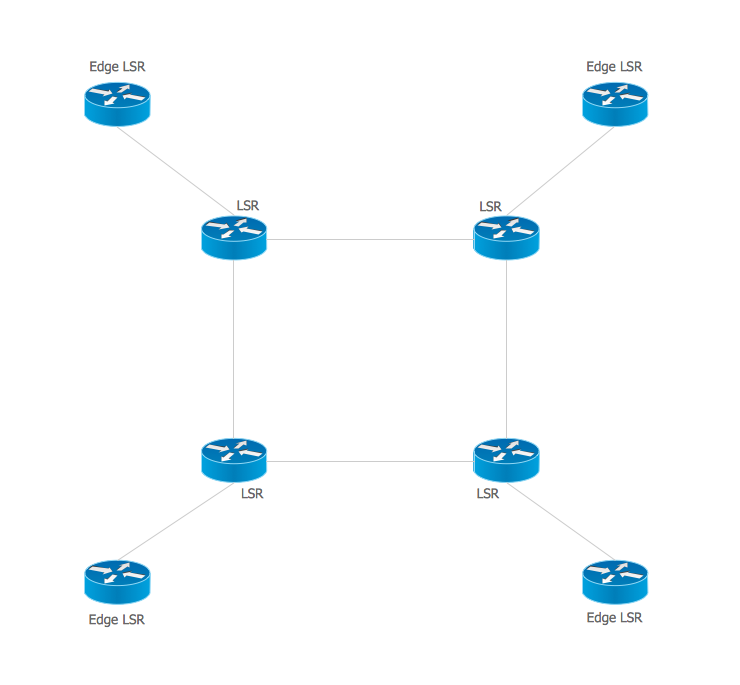 Picture: Multiprotocol Label Switching (MPLS). Computer and Network ExamplesRelated Solution:ConceptDrawDIAGRAM 18
Picture: Multiprotocol Label Switching (MPLS). Computer and Network ExamplesRelated Solution:ConceptDrawDIAGRAM 18