Network Security Devices
Assurance of network security is one of the most important moments for safe and correct working of the computer systems and networks. The network security includes assurance of the limited access to sensitive information, the protection from unauthorized access, risks and potential security threats, and enhancement of network performance. It is necessary to protect the network at all of its entry points, the most important factors in network security are encryption, reliable passwords, the use of antivirus software and modern advanced network security devices.
There are few types of network security devices:
- active devices - firewalls, antivirus scanning devices, content filtering devices, which block the surplus traffic;
- passive devices, such as intrusion detection appliances, which identify and report on unwanted traffic;
- preventative devices - penetration testing devices and vulnerability assessment appliances, which scan the networks and identify potential security problems;
- Unified Threat Management (UTM) devices, such as firewalls, content filtering, web caching, which serve as all-in-one security devices.
The most popular network security devices are firewalls - network security systems which establish a barrier between an internal network and the Internet, effectively manage and regulate the network traffic based on some protocols. Firewall can be software or hardware appliance, or include together hardware and software devices, most computers use software-based firewalls to secure their data from Internet threats, many routers also contain the firewall components.
Such network security devices as routers, crypto-capable routers, virtual private network gateways, secure modems and intrusion detection systems are also very popular. Intrusion detection systems are devices that monitor malicious activities in a network, log information about such activities and take active steps to stop them, and then report them.
How to describe the necessity of using network security devices and visually illustrate this information? Now, it's very easy thanks to the ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.

Example 1. Network Security Devices
The drawing tools of Network Security Diagrams Solution are very useful for network security design. This solution offers large collection of predesigned vector security clipart, icons, connectors and vector objects of network security devices developed by professional designers specially for ConceptDraw DIAGRAM users. All these 460 vector objects are grouped in 4 libraries:
- Cybersecurity Clipart
- Cybersecurity Round Icons
- Cybersecurity Shapes
- Cybersecurity Connectors

Example 2. Cybersecurity Clipart Library Design Elements
Each of these objects is ready-to-use. All that you need is simply double-click the icon at the library to add the chosen object in a moment to the middle of your document. Another way is to drag desired object from the library to the document page. Then you can arrange the objects, connect the objects in a desired way, add the text and make formatting changes.

Example 3. Network Security Diagram - Government Cloud Diagram
The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software and demonstrate network security schemes with using the network security devices. An experienced user spent 10 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Diagrams quick, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.
TEN RELATED HOW TO's:
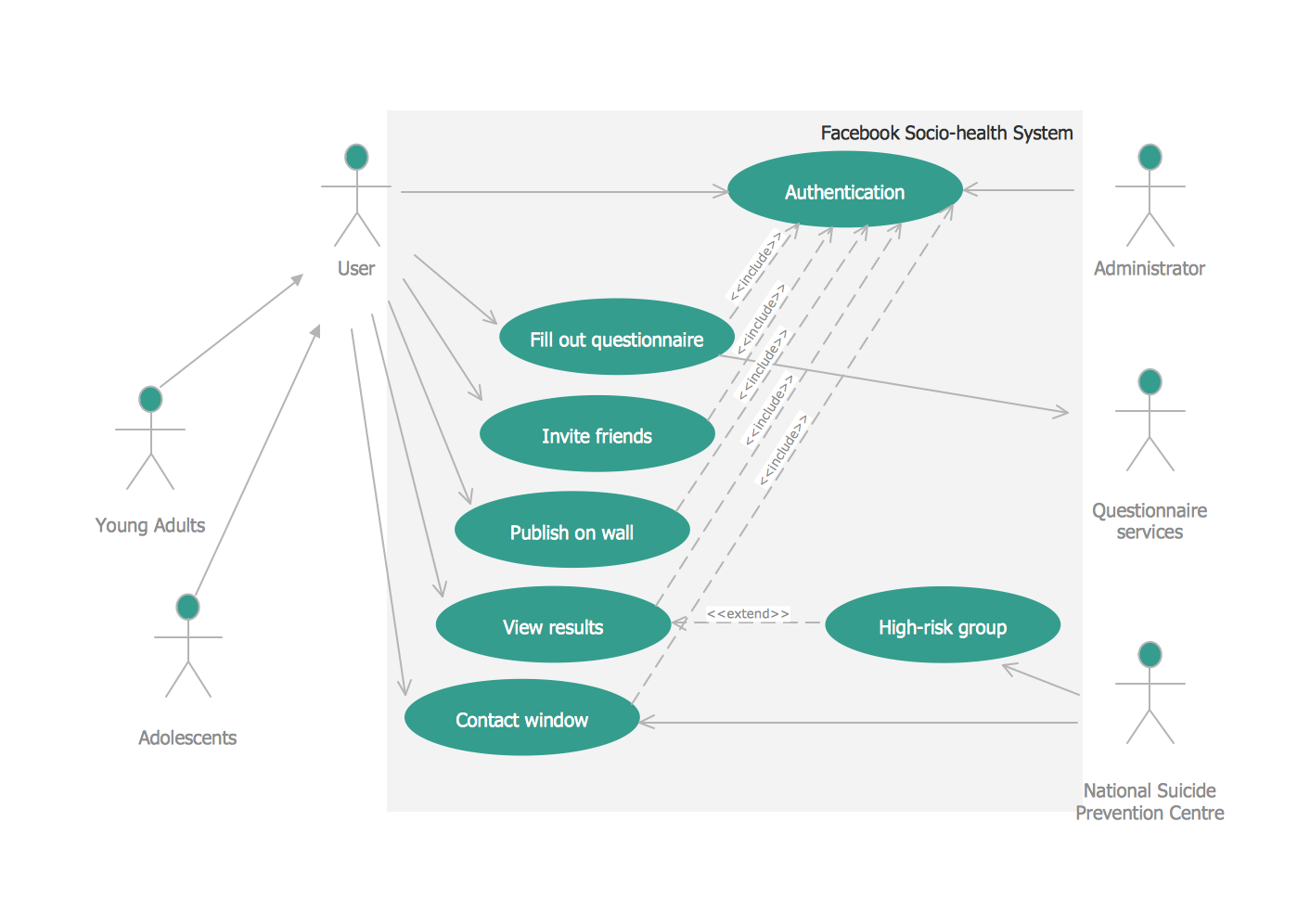
UML Diagrams Social Networking Sites Project. This sample was created in ConceptDraw DIAGRAM diagramming and vector drawing software using the UML Use Case Diagram library of the Rapid UML Solution from the Software Development area of ConceptDraw Solution Park.
This sample shows the Facebook Socio-health system and is used at the projection and creating of the social networking sites.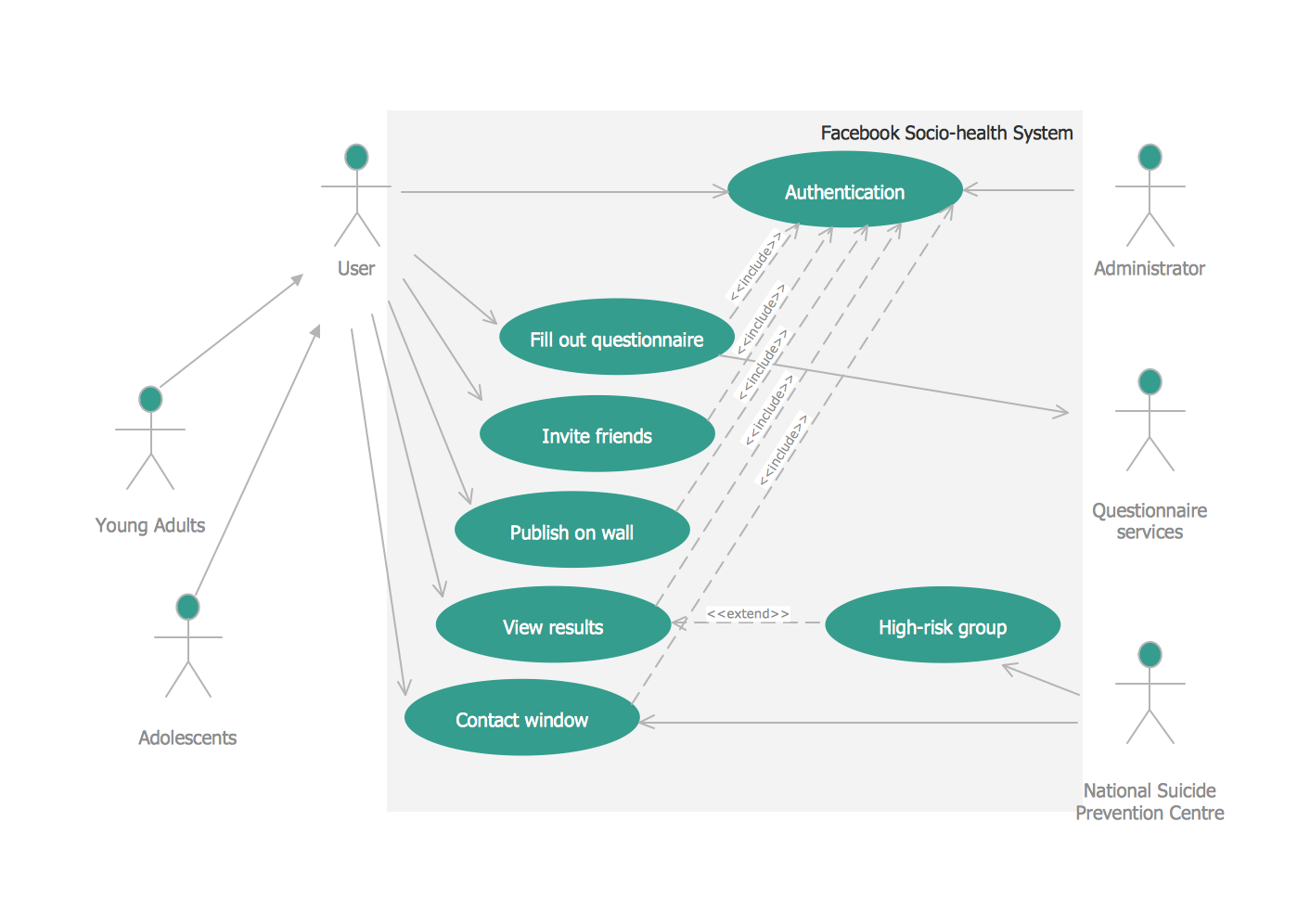
Picture: UML Use Case Diagram Example. Social Networking Sites Project
Related Solution:
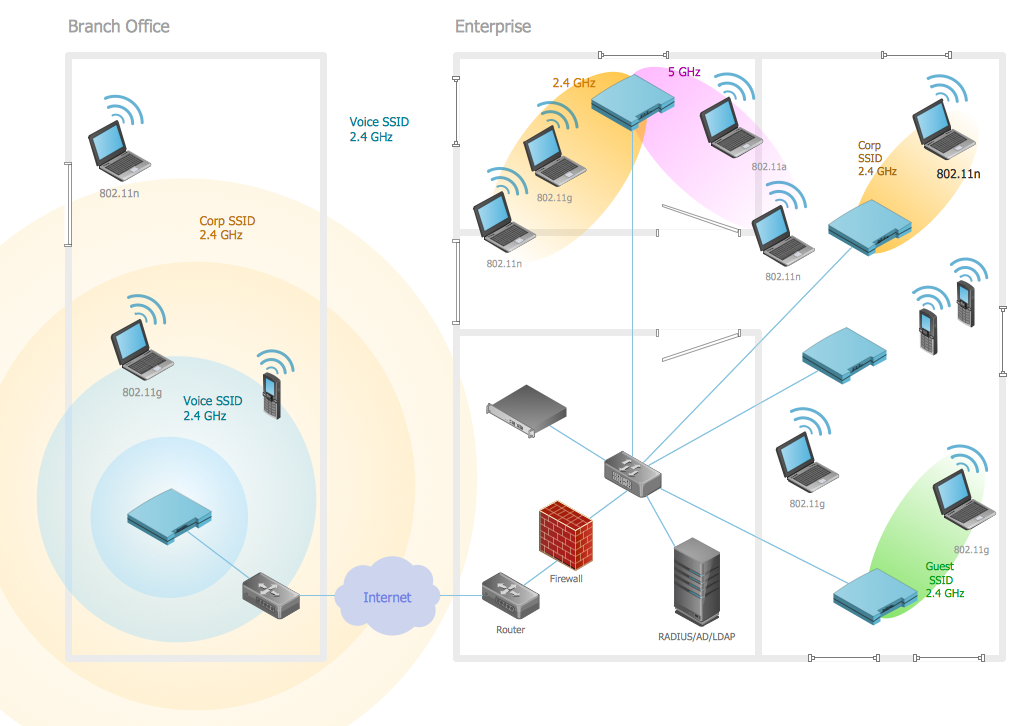
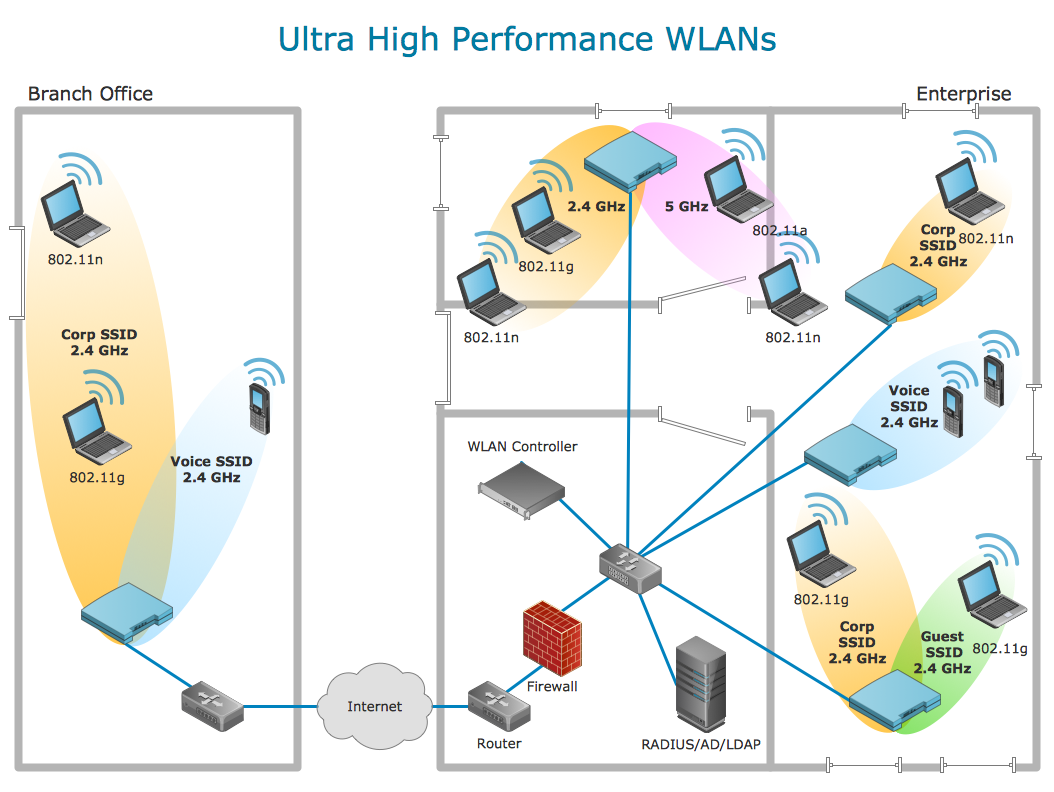
Wireless networking is useful visual tool for identification of all required equipment, and calculation the cost of creating or updating wireless computer networks. ConceptDraw DIAGRAM extended with Wireless Networks Solution from the Computer and Networks Area is the best wireless network diagramming software.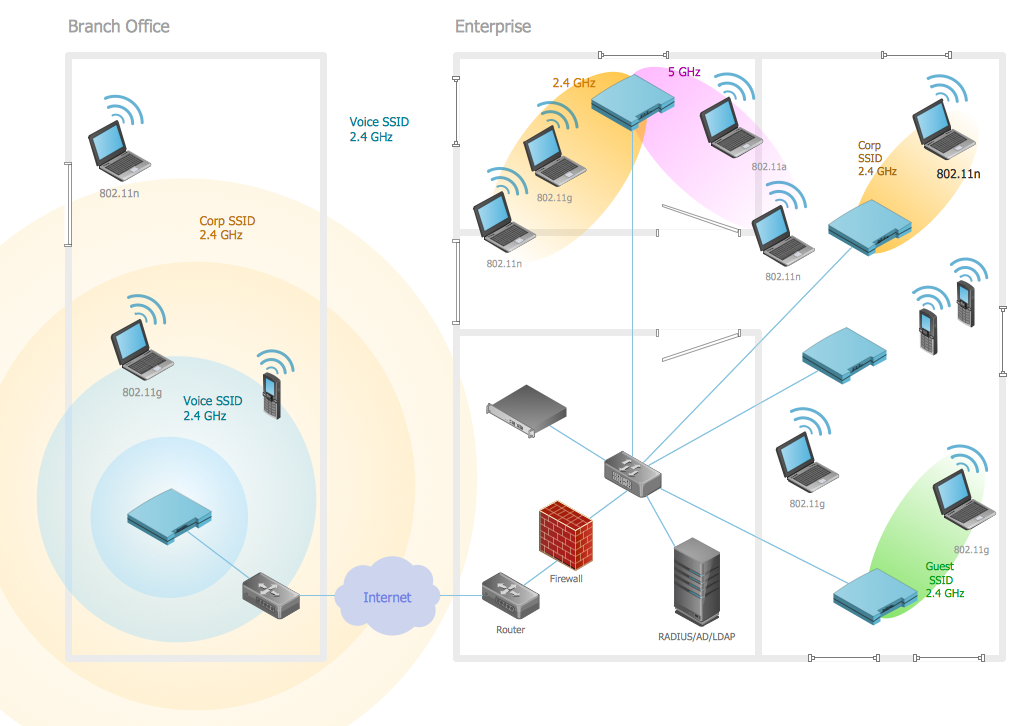
Picture: Wireless Networking
Related Solution:
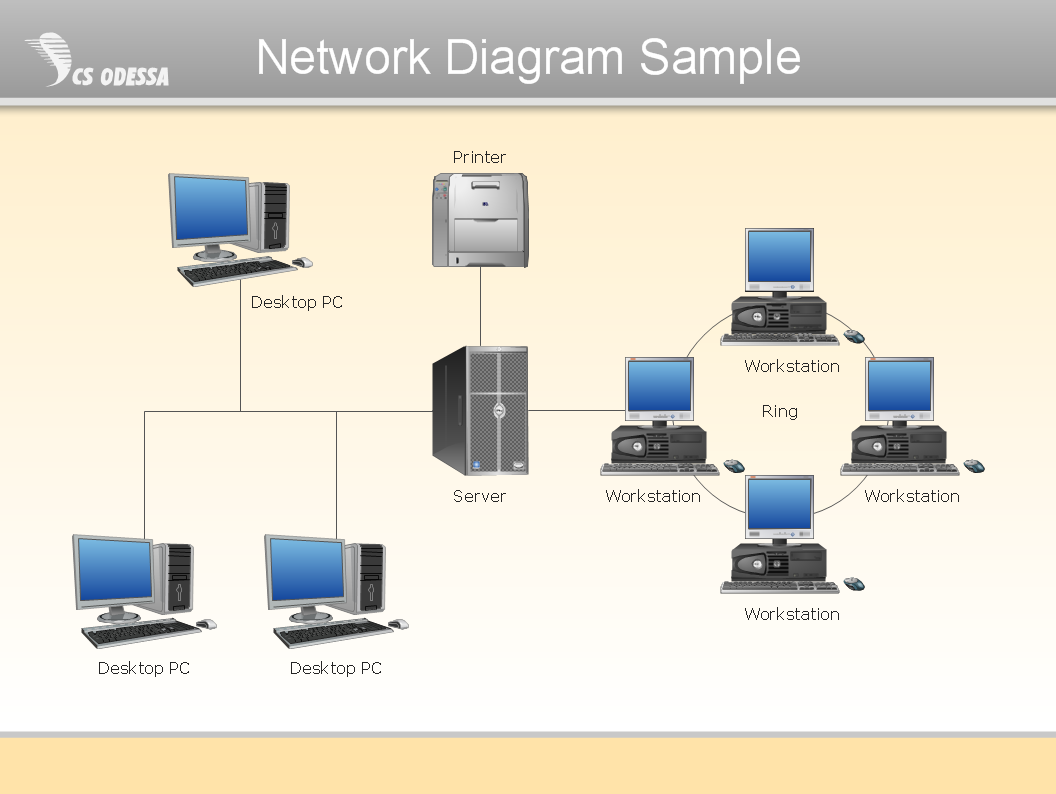
ConceptDraw Network Diagram Software is ideal for network engineers and network designers who need to draw Physical Network Diagrams.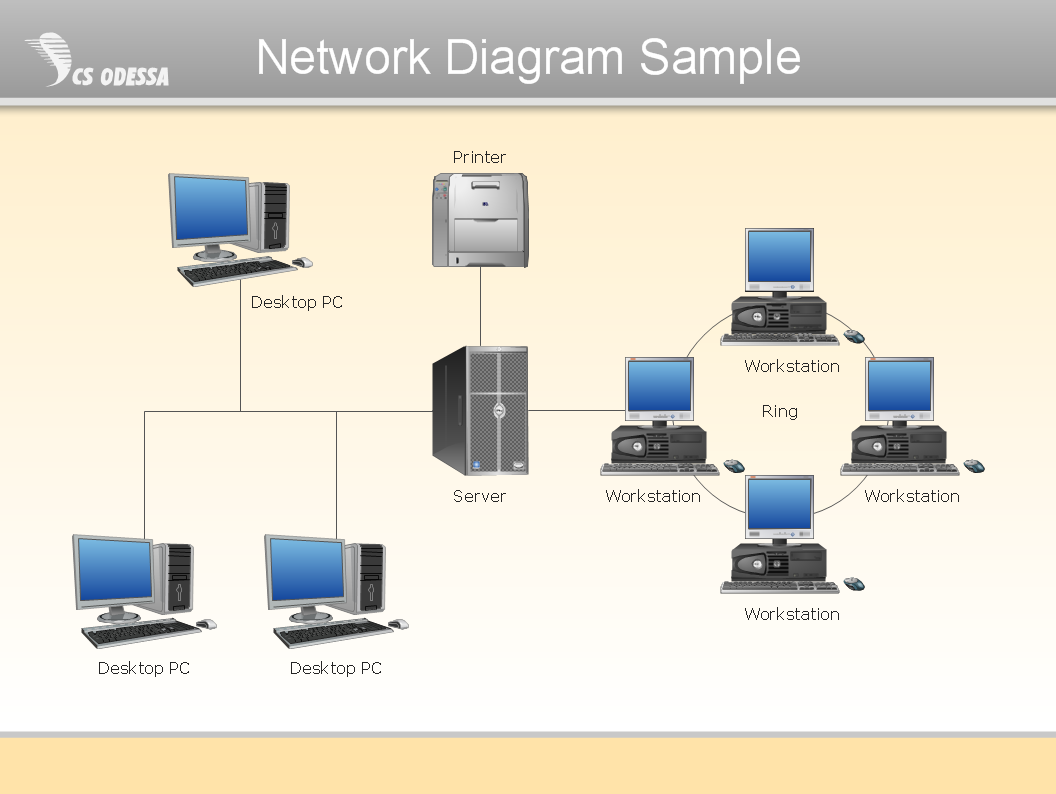
Picture: Network Diagram SoftwarePhysical Network Diagram
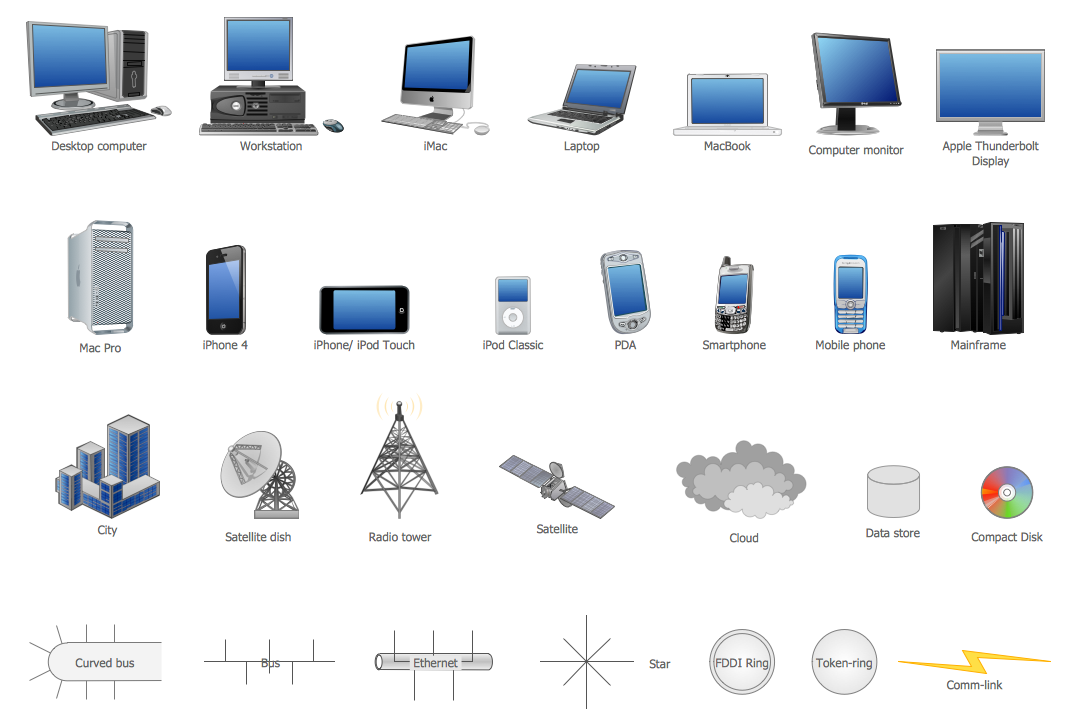
ConceptDraw DIAGRAM diagramming and vector drawing software extended with Computer Network Diagrams Solution from the Computer and Networks Area offers a set of useful tools, collection of templates, samples, and libraries of various computer symbols, computer devices icons, computer network icon for fast and easy drawing network computer diagrams and illustrations.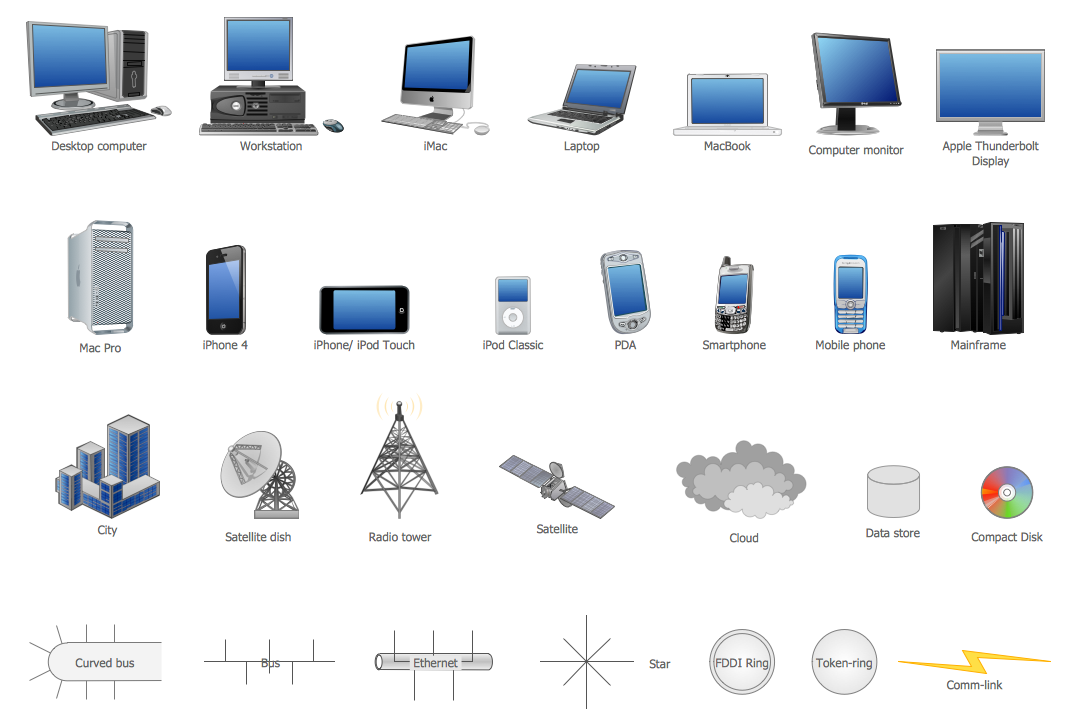
Picture: Network Icon
Related Solution:
Remote Networking - We explain the method most people use to connect to the Internet.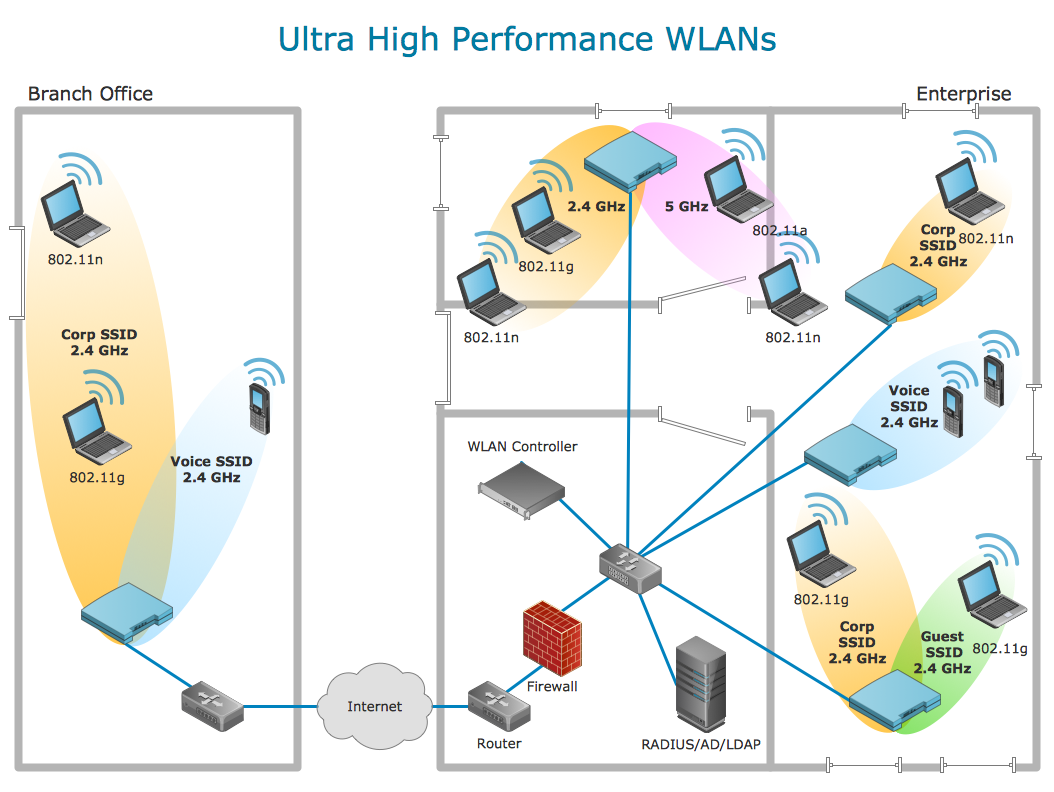
Picture: Using Remote Networking Diagrams
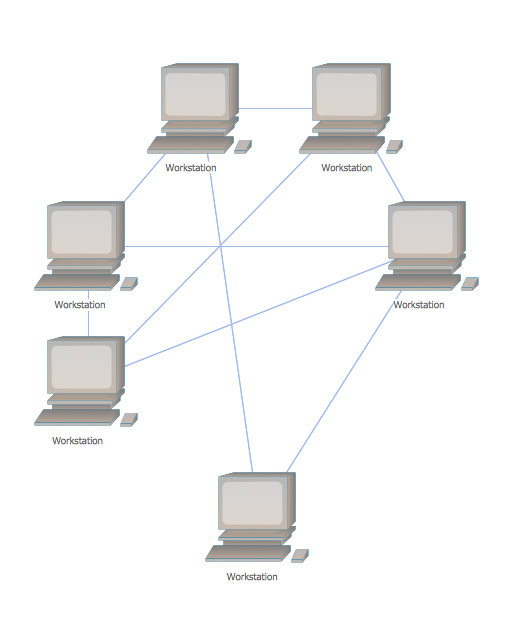
The reliability is a cornerstone for any corporate computer network. If you want to provide a high fault tolerance, a mesh network topology would be the solution. The main advantage of this network is that every node can work as a commutator, although it’s not easy to set up this kind of network.
A mesh network topology may be full, or partial. Full mesh network means that each node of the network (computer, workstation or other equipment) is connected directly to each of the other nodes. A partial mesh topology means that a part of nodes are connected with a whole network, and the other part of nodes are only connected to those equipment, they exchange the majority of data. This illustration shows schematic diagram of a partial mesh network containing six nodes. Each node is represented as a circles and connections are drawn as straight lines. The connections may be both wired and wireless. This scheme can be used to make the specific logical or physical network diagrams by means the ConceptDraw Computer and Networks solution.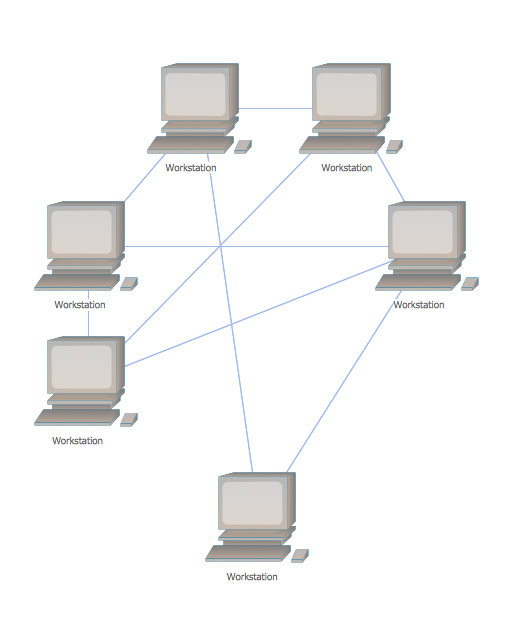
Picture: Mesh Network Topology Diagram
Related Solution:
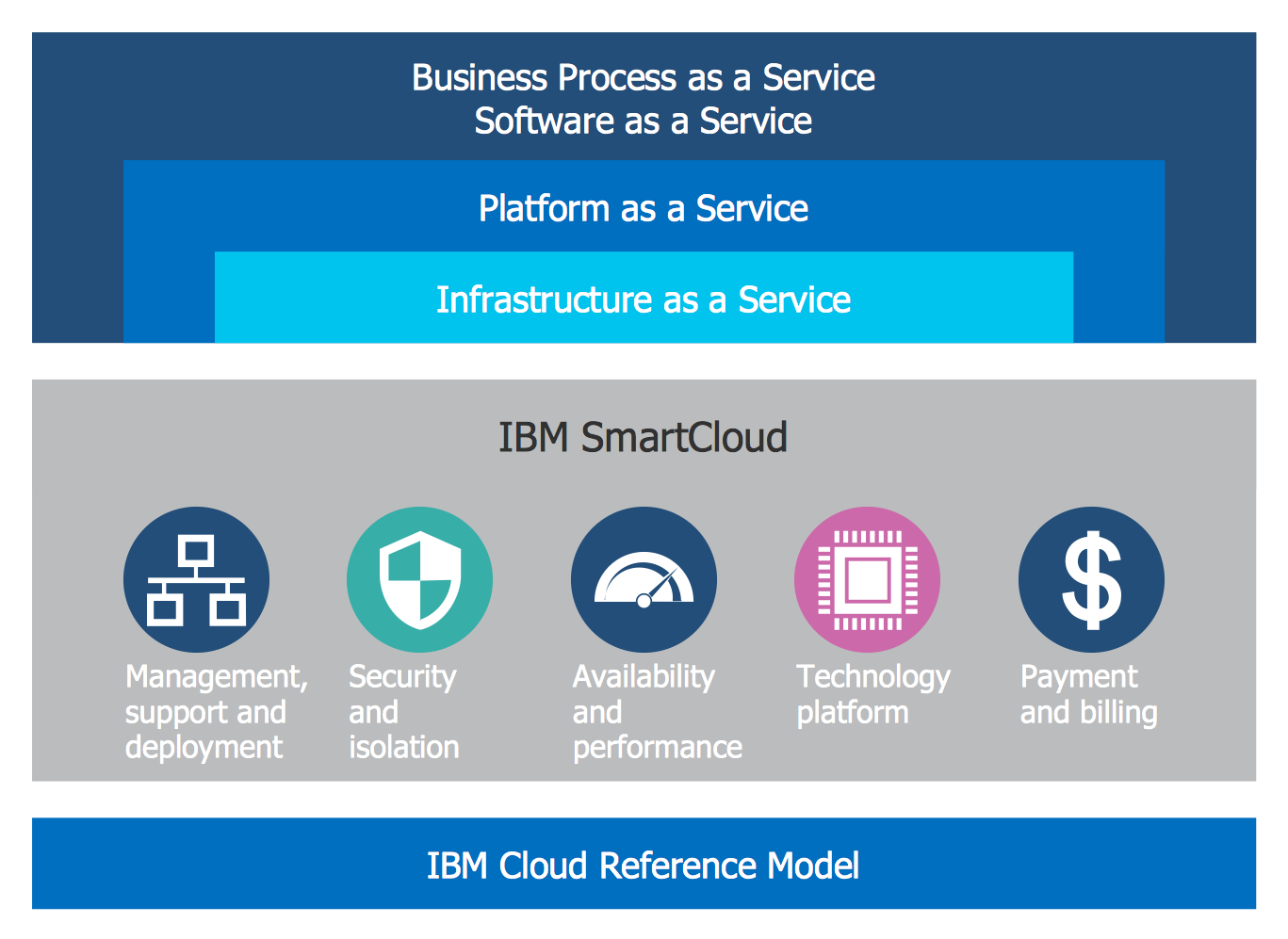
For documenting the Cloud Computing Architecture with a goal to facilitate the communication between stakeholders are successfully used the Cloud Computing Architecture diagrams. It is convenient and easy to draw various Cloud Computing Architecture diagrams in ConceptDraw DIAGRAM software with help of tools of the Cloud Computing Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.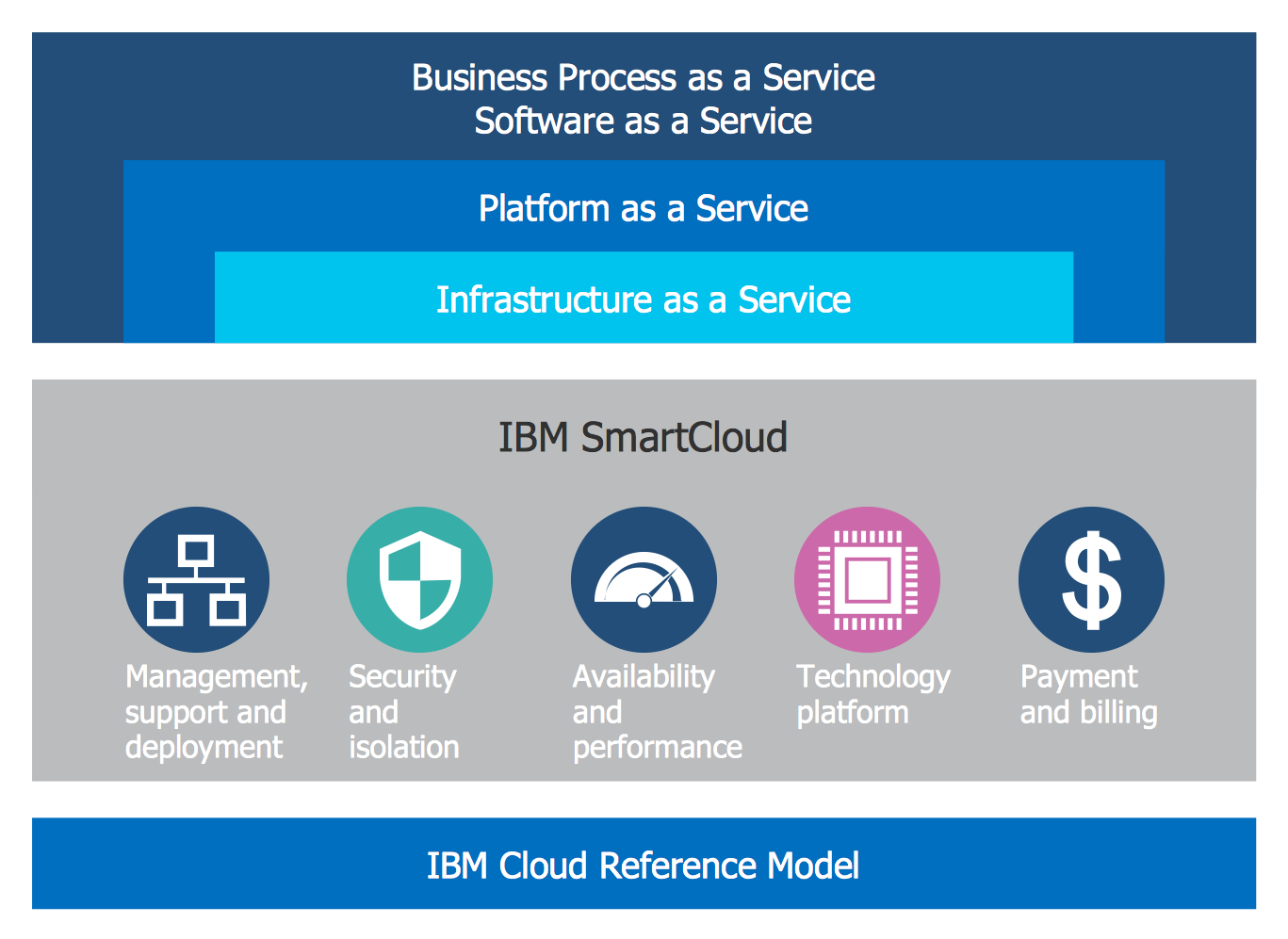
Picture: Cloud Computing Architecture Diagrams
Related Solution:
Sometimes, when it is difficult to create a functional space plan or to rearrange existing one, the art of interior design comes in. It doesn't matter, if you need a cozy bedroom or an office layout plan, you should use appropriate tools to make your design great.
While making a floor plan of a new office it could be useful to apply some design elements such as furniture and office equipment. This diagram presents an office furniture objects that can be used for office interior design planning, or making office furniture and equipment layouts. This vector stencils library is supplied with ConceptDraw Office Layout Plans solution. It contains more then 30 vector objects of office interior for making office floor plans including an office space layout plans and furniture arrangement.
Picture: Interior Design. Office Layout Plan Design Element
Related Solution:
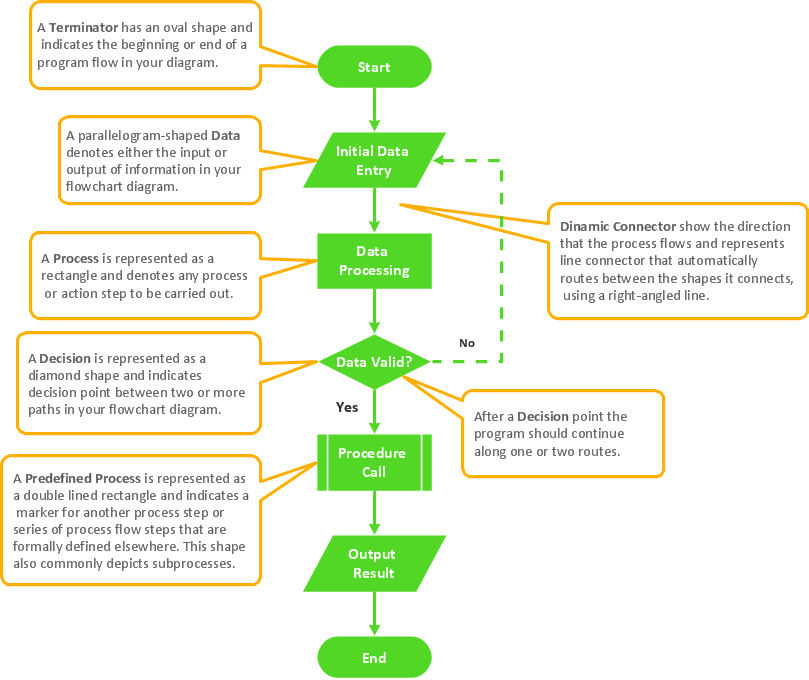
The ConceptDraw Flowchart component includes a set of samples and templates. This geathered as flowchart maker toolbox which focused on drawing flowcharts of any industry standards.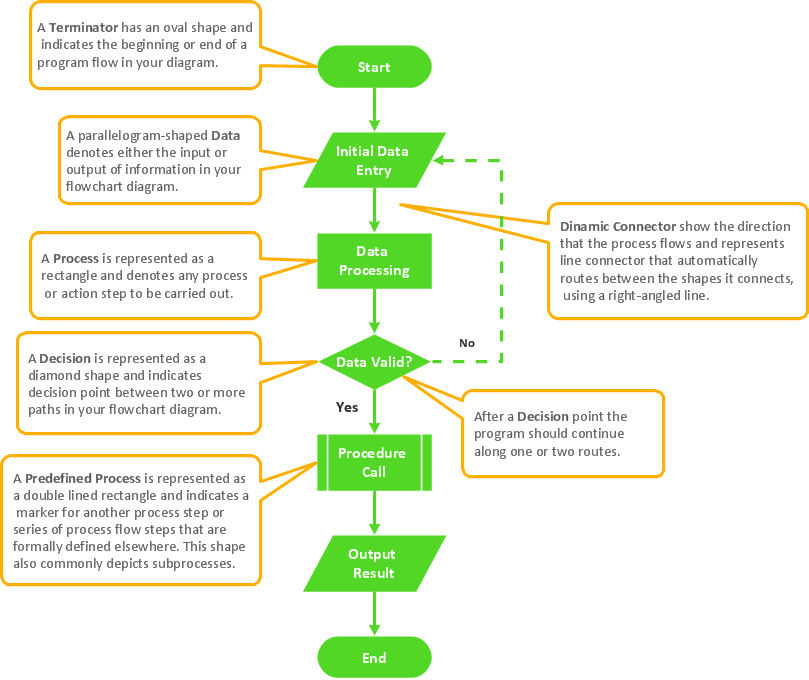
Picture: Flowchart Components
Related Solution:
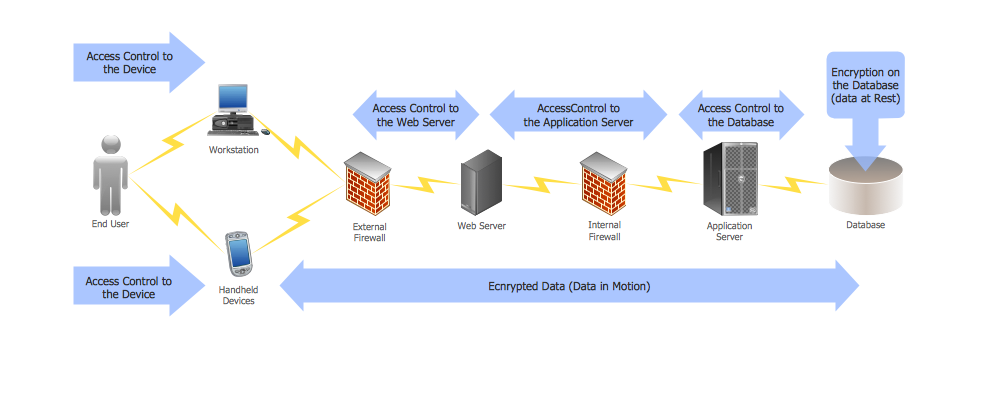
29095The Data Encryption Standard (DES) is a symmetric-key algorithm for the encryption of the electronic data.
This diagram was created in ConceptDraw DIAGRAM using the Computer and Networks Area of ConceptDraw Solution Park and shows how the encryption and access control work together to secure data.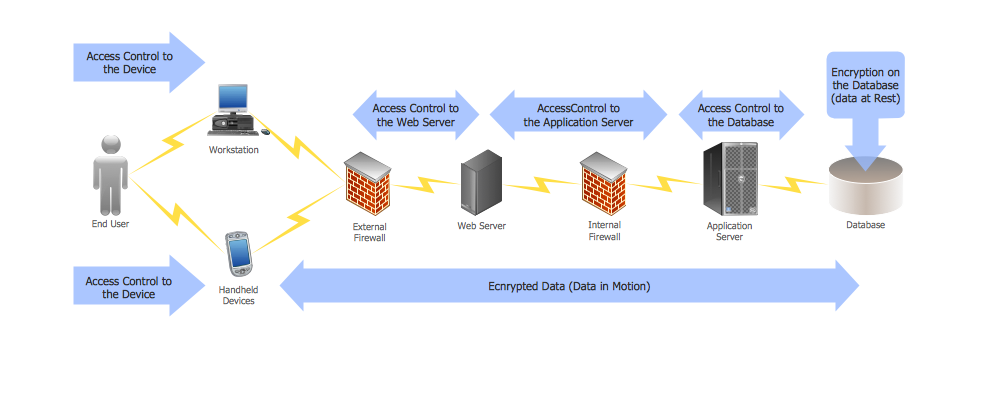
Picture: DES Network. Computer and Network Examples
Related Solution: