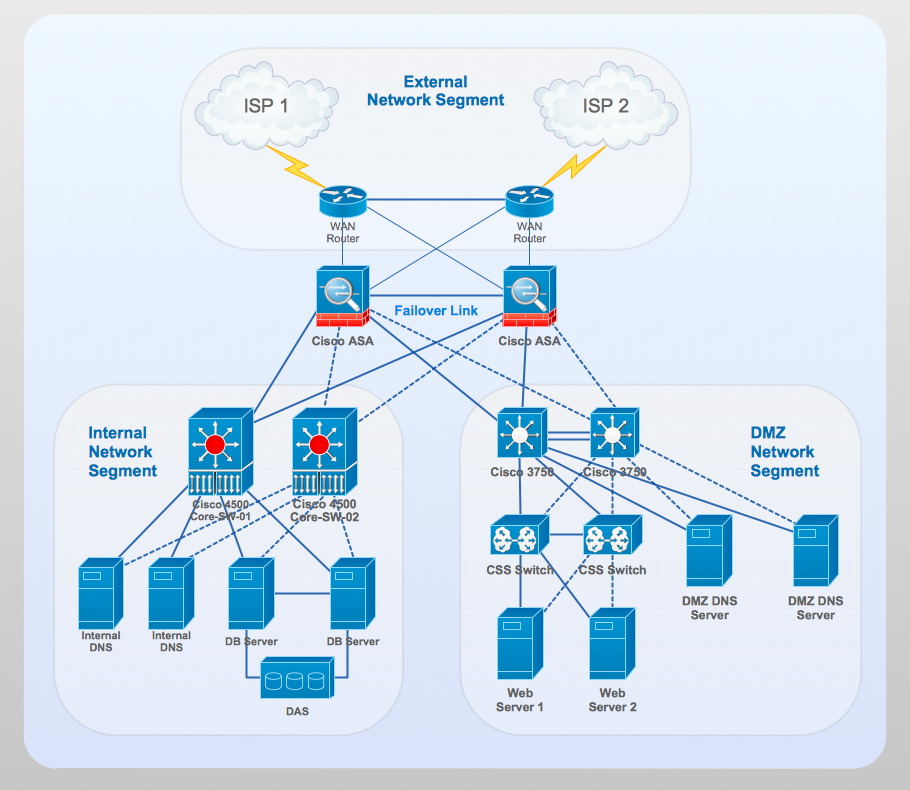
Network Security Tips
The Internet sure came into our live a few decades ago and now few people can imagine its life without him. It's a huge world with unlimited possibilities! Initially most people used the Internet only to search different information. Today it provides wide opportunities to learn, work, play, communicate with people around the world, etc. But with all its numerous advantages, the Internet also conceals many dangers and security threats, that's why we advise you to follow simple network security tips:
- Make creative usernames and don't use your real name as username.
- Create complex and strong passwords that contain letters, numbers and symbols, and keep them at the secret.
- Never disclose your personal confidential information while online, such as name, age, address, telephone number, personal ID number, bank account details, credit card numbers.
- Read attentively the terms and privacy policy for the sites and applications you use.
- Keep in mind that all information, data, files which you have posted online, are available for trillions of people. Even deleted information can be stored long at the older version of the site hosting, and so is still available at strong desire.
- Stay careful and attentive at the choice of your new virtual friends.
- Use the last versions of secure browsers with recommended default settings.
- Be extremely careful when working with email.
- And the most important use the firewalls and last versions of reliable anti-virus software, effective security applications which warn about unsafe of files you download or open.
Follow these simple, but essential network security tips to use the Internet safely and enjoyably.
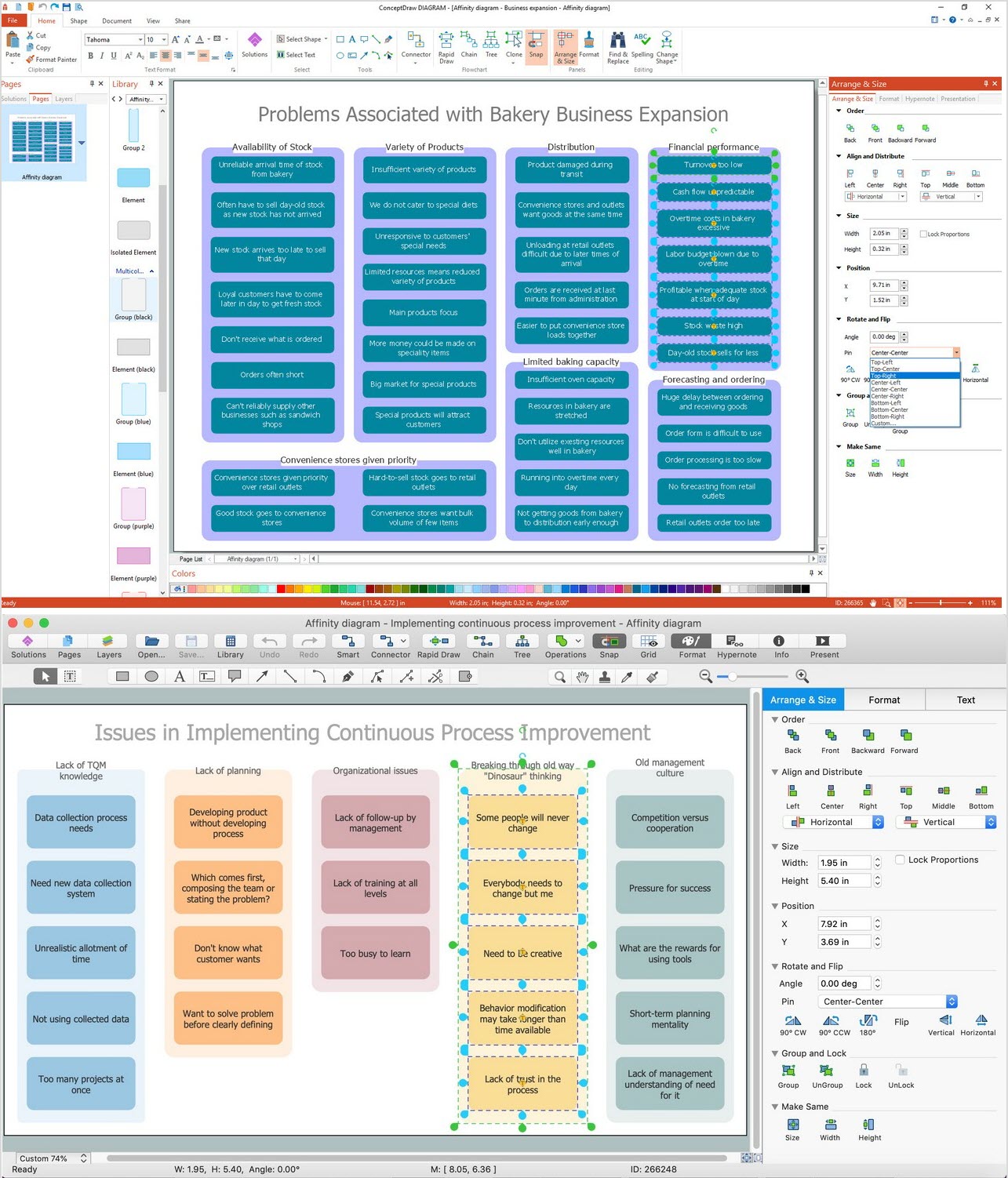
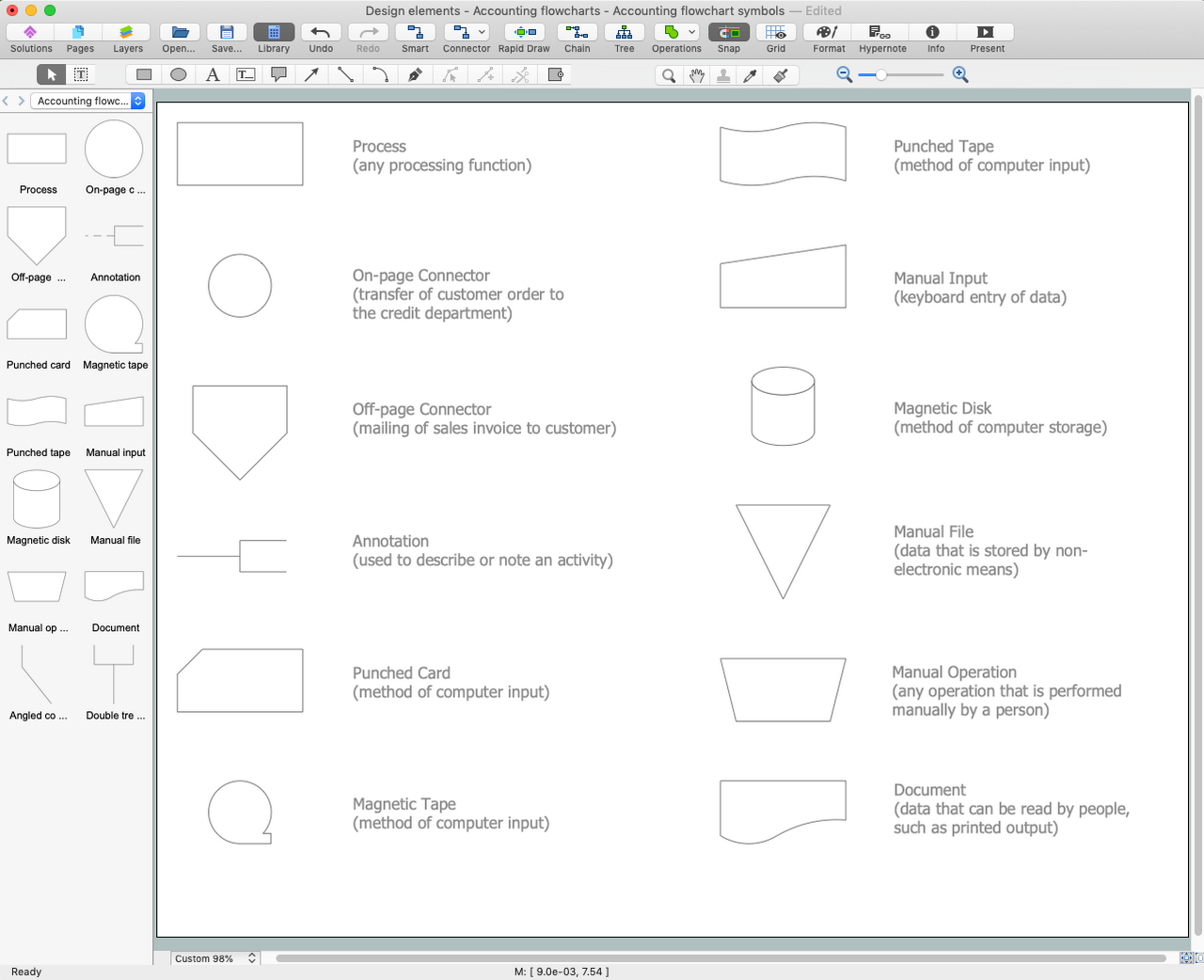
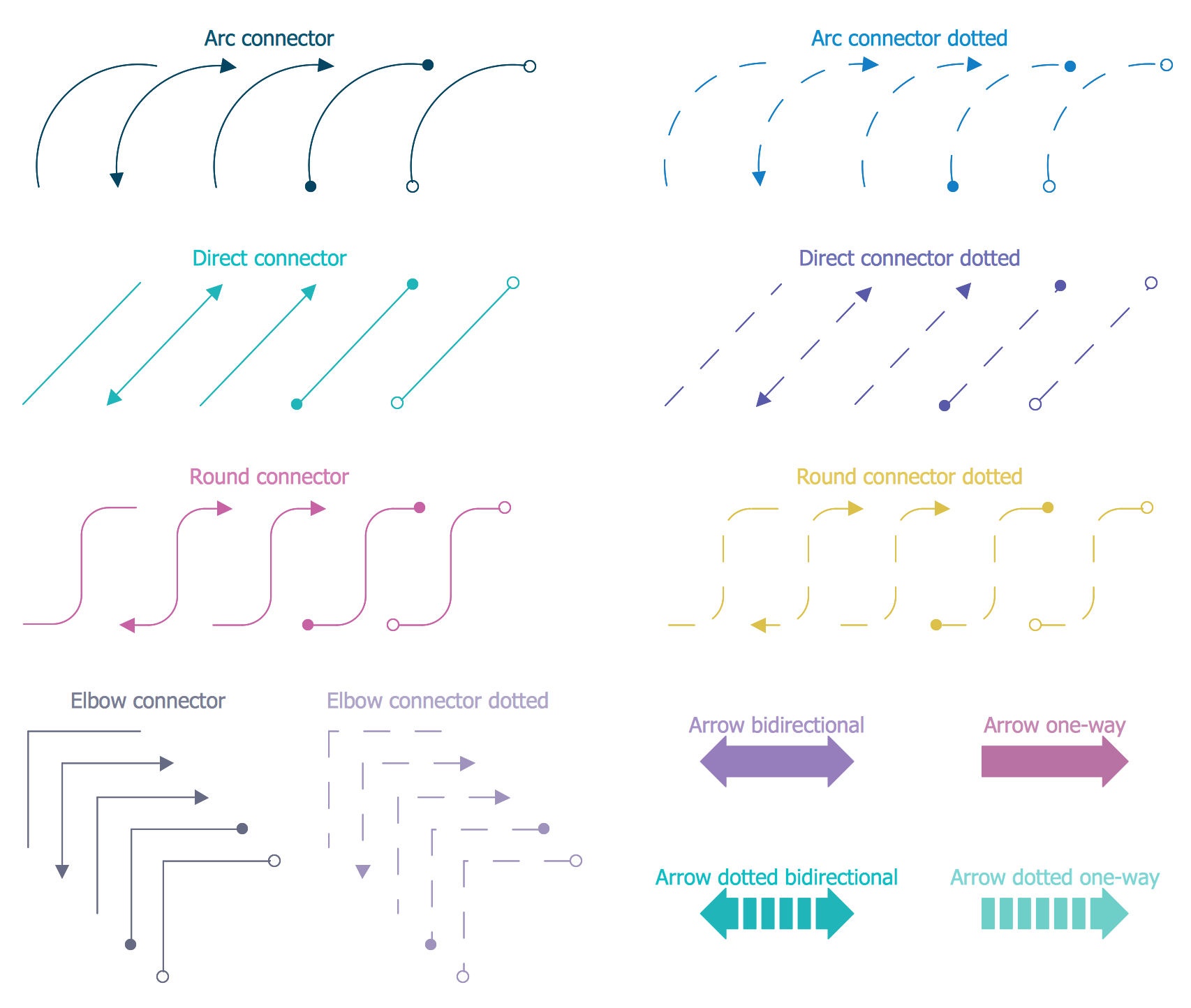
ConceptDraw DIAGRAM diagramming and vector drawing software supplied with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is an ideal software for easy designing Network Security Diagrams and attractive illustrations with effective network security tips.
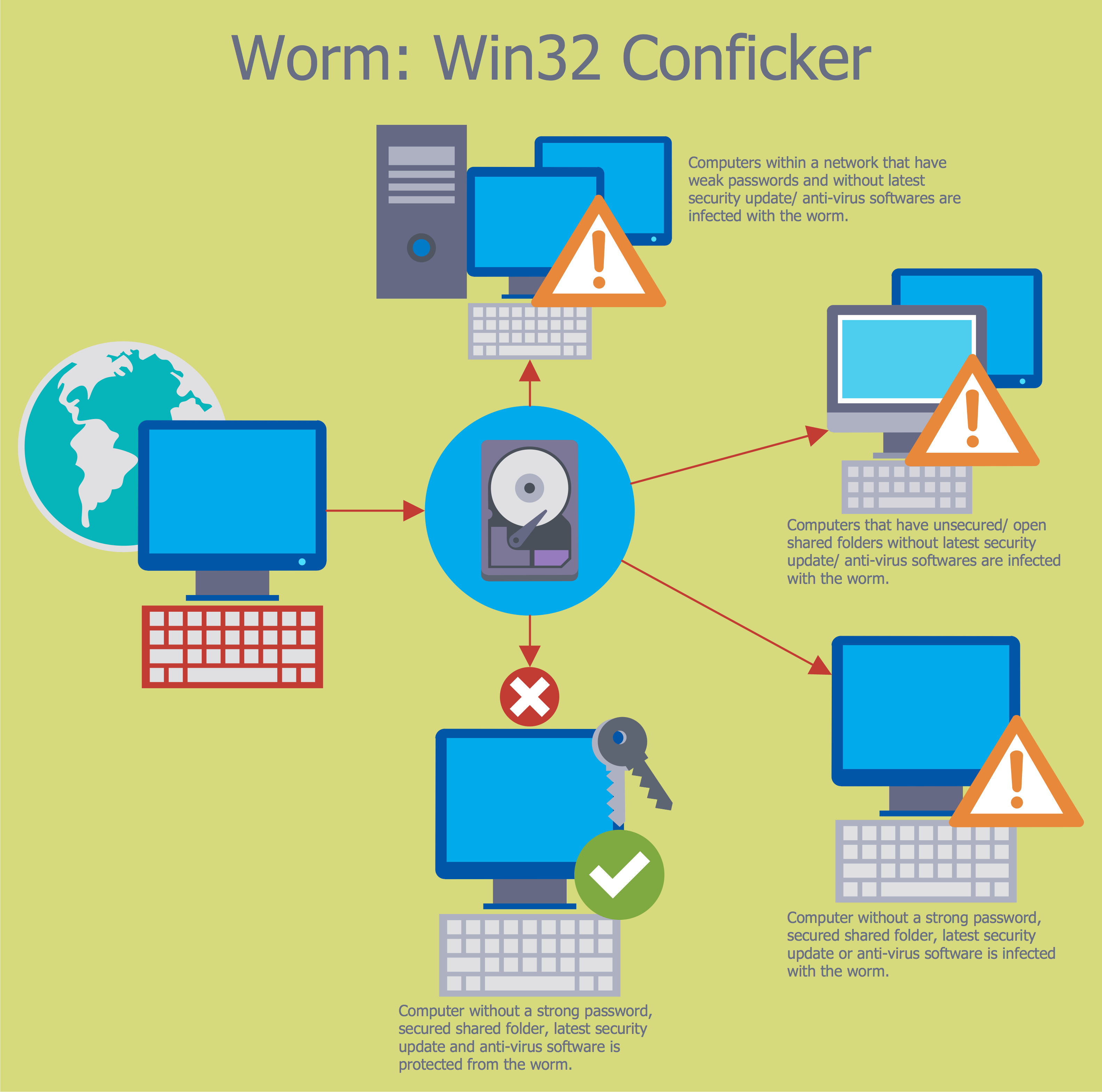
Example 1. Network Security Tips
The powerful drawing tools of ConceptDraw DIAGRAM software and Network Security Diagrams Solution are so much useful for effective Network Security Diagram design and network security tips vivid representation. First of all, it is worth to note collection of predesigned vector objects developed by professional designers specially for Network Security Diagrams Solution. These are 4 libraries with 460 vector objects.
Network Security Diagrams Solution provides also wide variety of predesigned samples and examples of Network Security Diagrams and Infographics. Each of them is carefully thought-out by experts and is available for viewing and editing from ConceptDraw STORE. You can use any desired sample from the offered to get the excellent result for the creation your own diagram in a few minutes
Example 2. Network Security Infographic - 10 Steps to Cyber Security
The samples you see on this page were created in ConceptDraw DIAGRAM using the the recommended network security tips and powerful tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software. An experienced user spent 10-15 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Diagrams quick, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.