Example 1. Network Security Devices
The drawing tools of Network Security Diagrams Solution are very useful for network security design. This solution offers large collection of predesigned vector security clipart, icons, connectors and vector objects of network security devices developed by professional designers specially for ConceptDraw DIAGRAM users. All these 460 vector objects are grouped in 4 libraries:
- Cybersecurity Clipart
- Cybersecurity Round Icons
- Cybersecurity Shapes
- Cybersecurity Connectors

Example 2. Cybersecurity Clipart Library Design Elements
Each of these objects is ready-to-use. All that you need is simply double-click the icon at the library to add the chosen object in a moment to the middle of your document. Another way is to drag desired object from the library to the document page. Then you can arrange the objects, connect the objects in a desired way, add the text and make formatting changes.

Example 3. Network Security Diagram - Government Cloud Diagram
The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software and demonstrate network security schemes with using the network security devices. An experienced user spent 10 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Diagrams quick, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.
TEN RELATED HOW TO's:
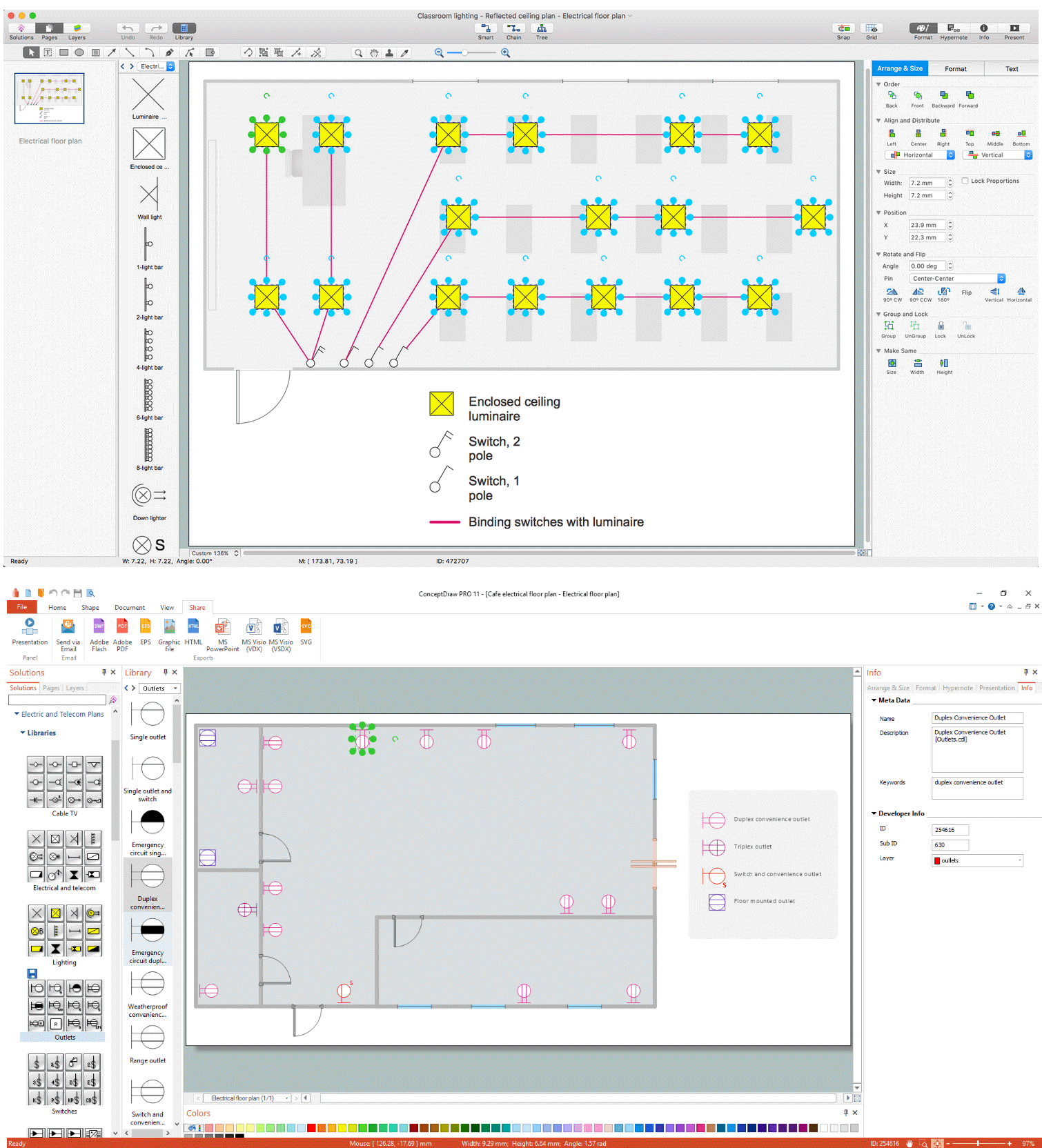
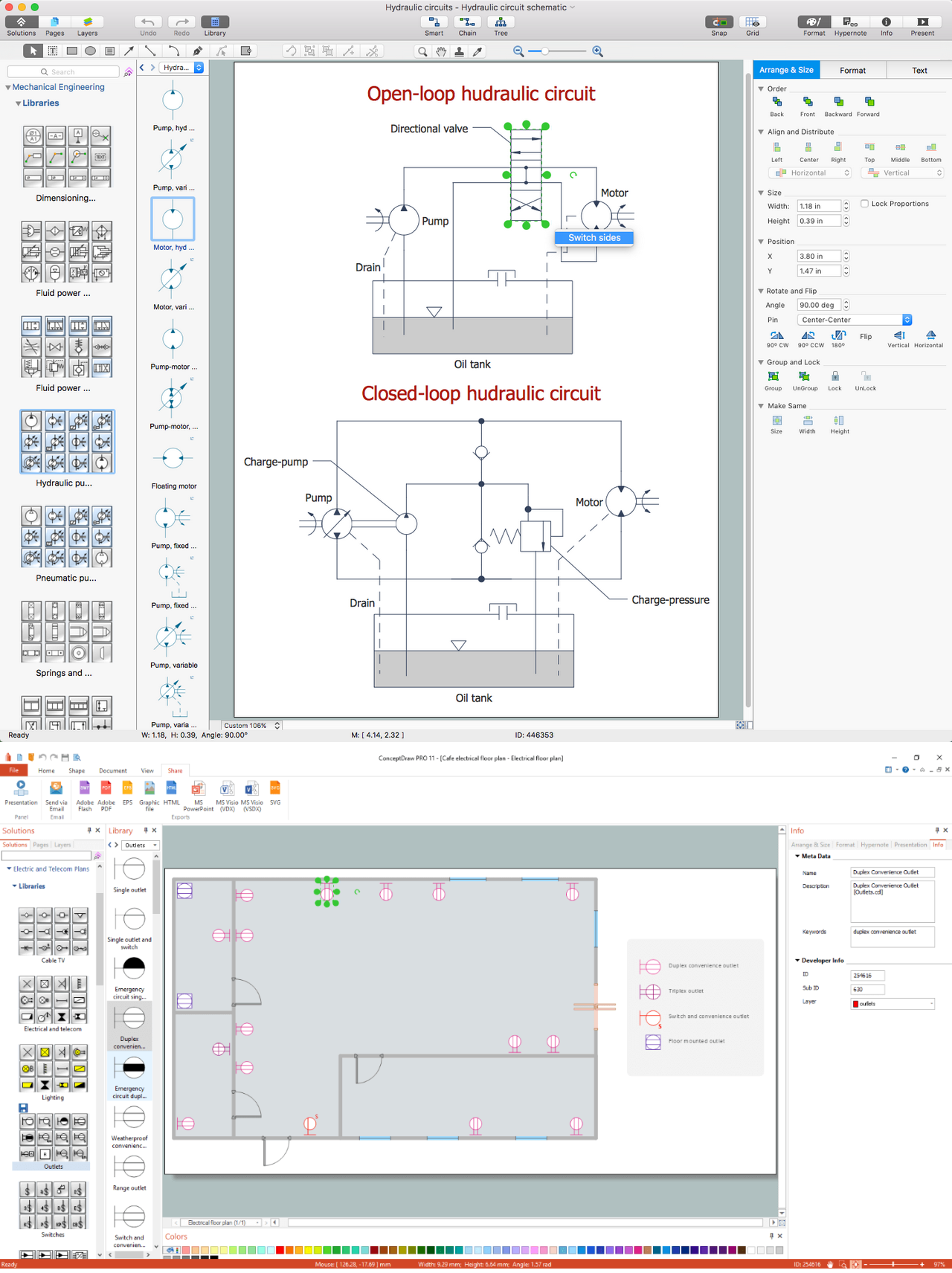
While studying, many of the students encounter the necessity of remaking class projects, over and over. To facilitate this process you can use special electrical and telecom plan software, which helps altering projects in several clicks. Using templates will fasten your work, and you will have more free time.
This sample represents an electrical and telecommunication floor plan. Electrical and telecom floor plans contain a floor plan , on which imposed the layout of electrical, and telecommunications equipment. They shows electrical and telecom details regarding the current floor of a building: lightening, fixtures, wires, outlets, circuit panels, etc. Using of standart notation of electrical and telecommunication symbols makes the plan understandable for engineers, architects, constructors, specialist in electricity and telecommunications.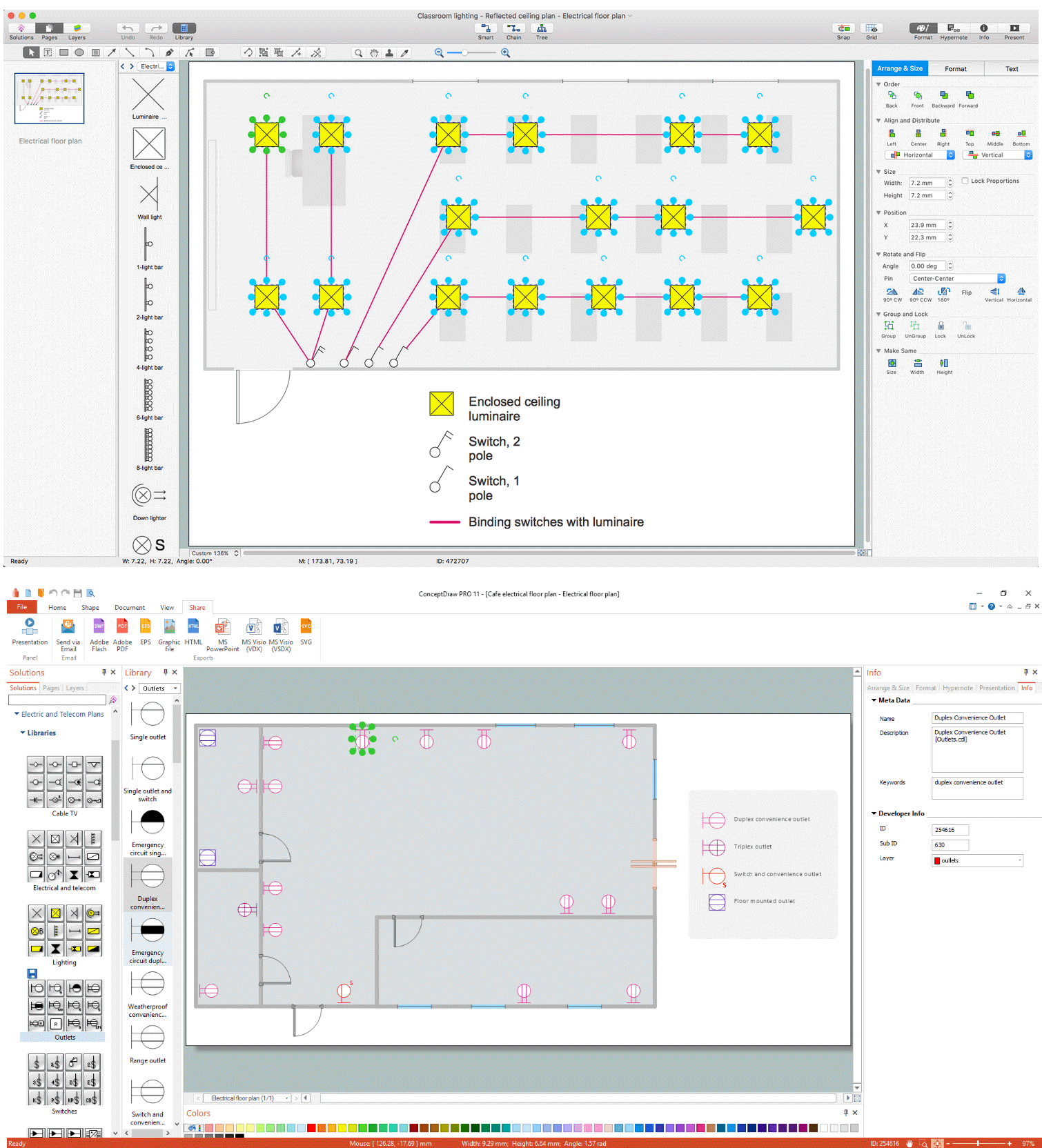
Picture: Electrical and Telecom Plan Software
Related Solution:
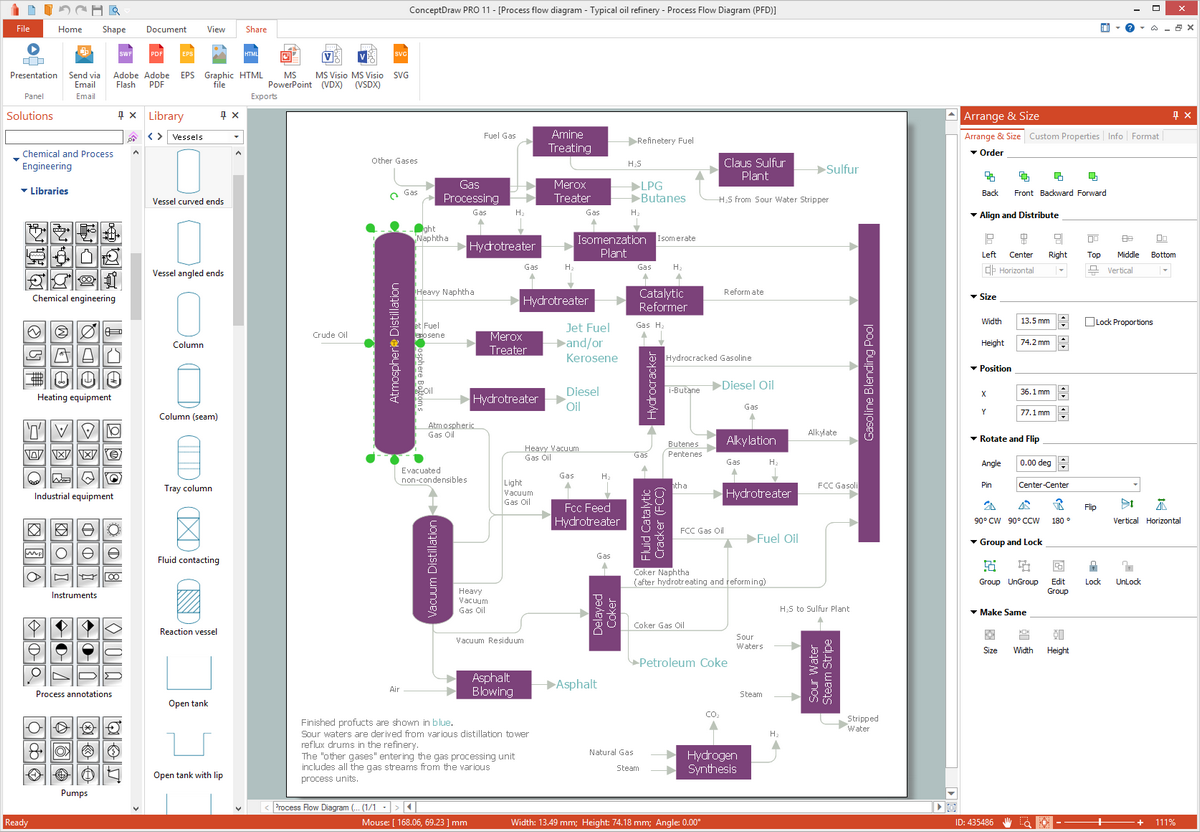
ConceptDraw DIAGRAM is a powerful diagramming and vector drawing software. Extended with Chemical and Process Engineering Solution from the Industrial Engineering Area of ConceptDraw Solution Park, it became the best Chemical Engineering software.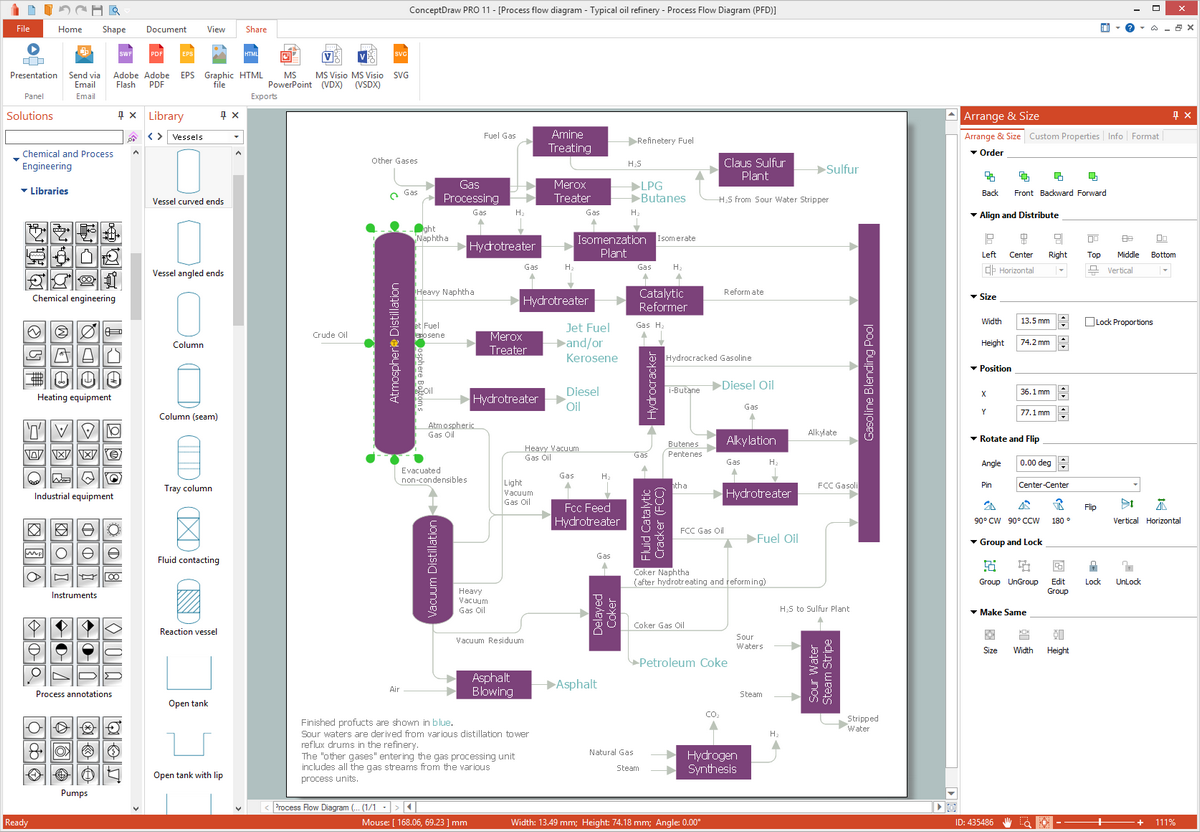
Picture: Chemical Engineering
Related Solution:
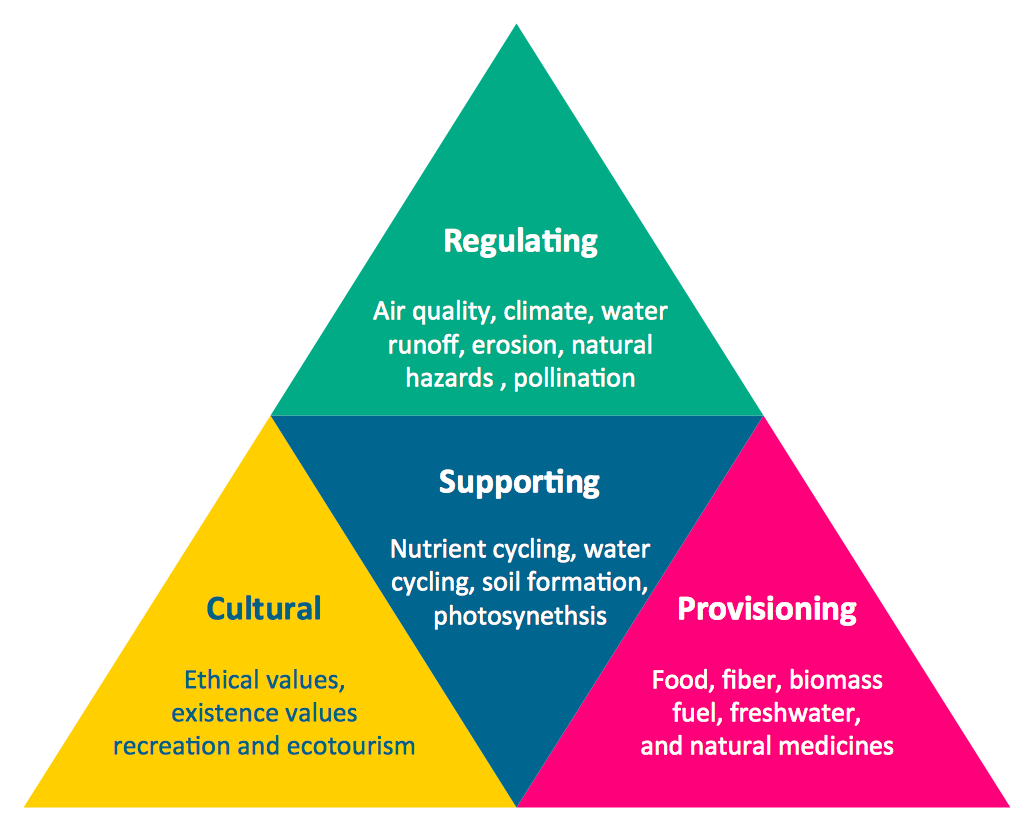
When we think of an hierarchy, we intuitively imagine a pyramid. Thus, a lot of management tools use pyramid charts as examples or illustrations of various documents or models. You can create any type of triangle diagram using ConceptDraw DIAGRAM.
A triangle (pyramid) diagram is often used in marketing to show the data hierarchy. This pyramid diagram represents the Top Brand Model. It illustrate the model of rebranding strategy. It can be used by marketing agency dealing with rebranding strategies development. It’s critical for marketing diagrams to be both clear and eye catching. ConceptDraw Pyramid diagrams solution meet all these requirements and can be successfully applied for creating and presenting various marketing pyramidal diagrams.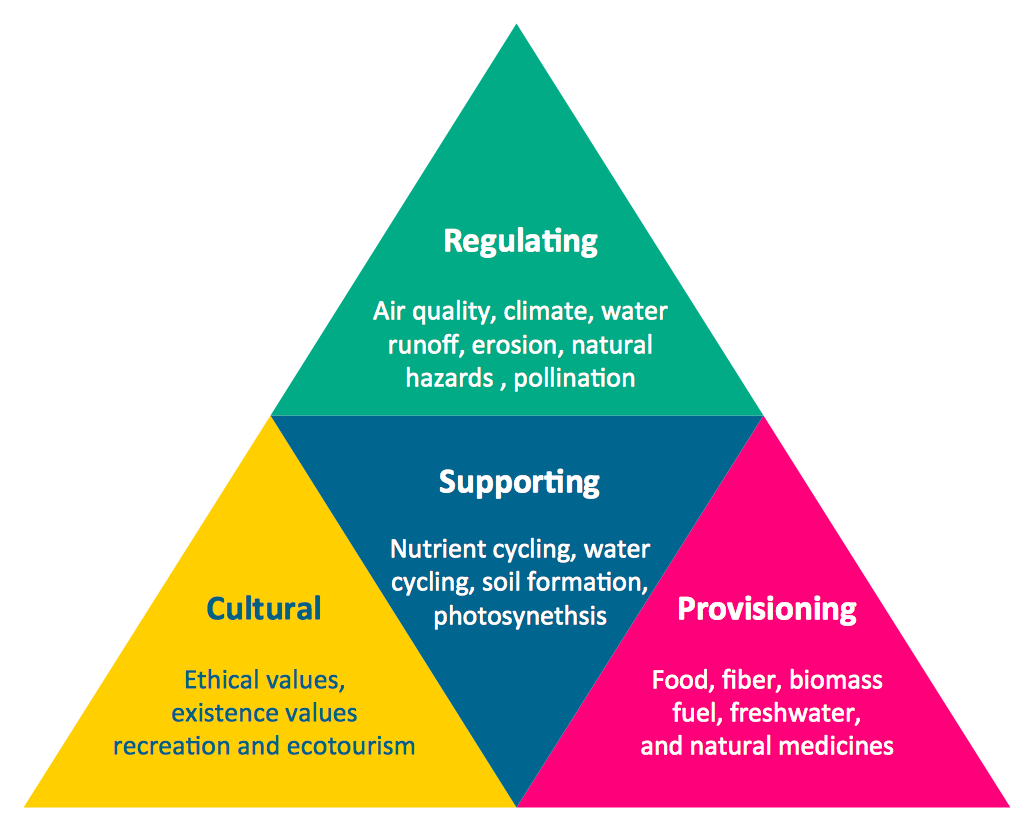
Picture: Pyramid Chart Examples
Related Solutions:
One of the three main constituents of any enterprise is the Control and Information Architecture. The rest two are Production facilities and People and Organization.
Picture: Control and Information Architecture Diagrams (CIAD) with ConceptDraw DIAGRAM
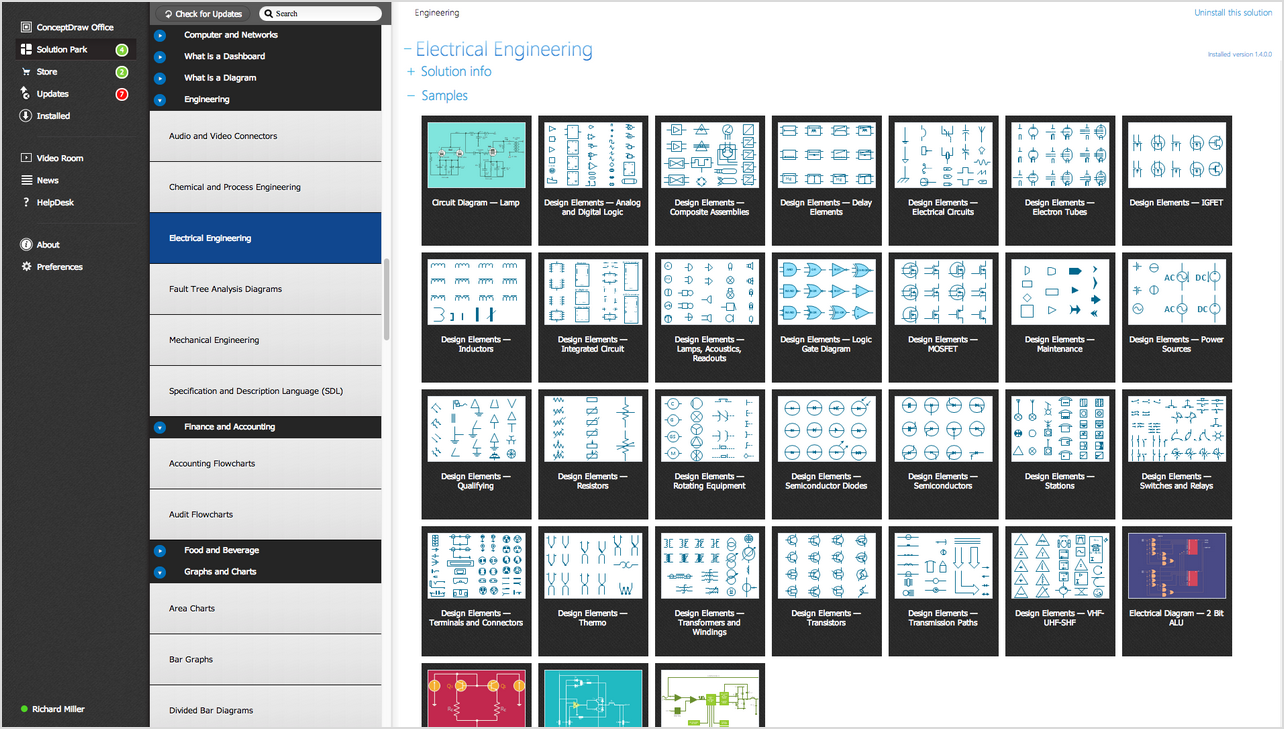
Electrical Engineering Solution used together with ConceptDraw DIAGRAM drawing facilities makes short a work of drawing various electrical and electronic circuit schemes. A library of vector objects composed from symbols of Analog and Digital Logic elements of electric circuit includes 40 symbolic images of logic gates, bistable switches of bi-stable electric current, circuit controllers, amplifiers, regulators, generators, etc. All of them can be applied in electronic circuit schemes for showing both analog and digital elements of the circuit.
Electrical Engineering Solution used together with ConceptDraw DIAGRAM drawing facilities makes short a work of drawing various electrical and electronic circuit schemes. A library of vector objects composed from symbols of Analog and Digital Logic elements of electric circuit includes 40 symbolic images of logic gates, bistable switches of bi-stable electric current, circuit controllers, amplifiers, regulators, generators, etc. All of them can be applied in electronic circuit schemes for showing both analog and digital elements of the circuit.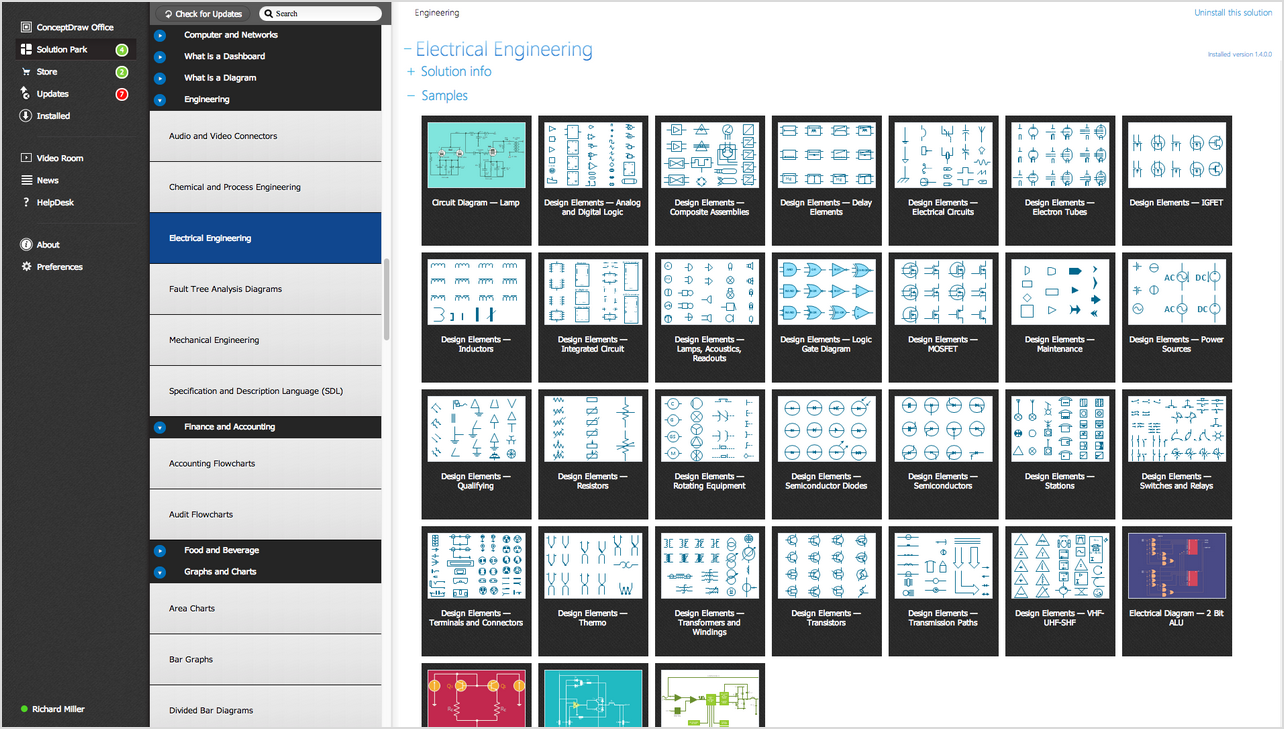
Picture:
Electrical Diagram Symbols F.A.Q.
How to Use Electrical ConceptDraw Diagram Software
Related Solution:
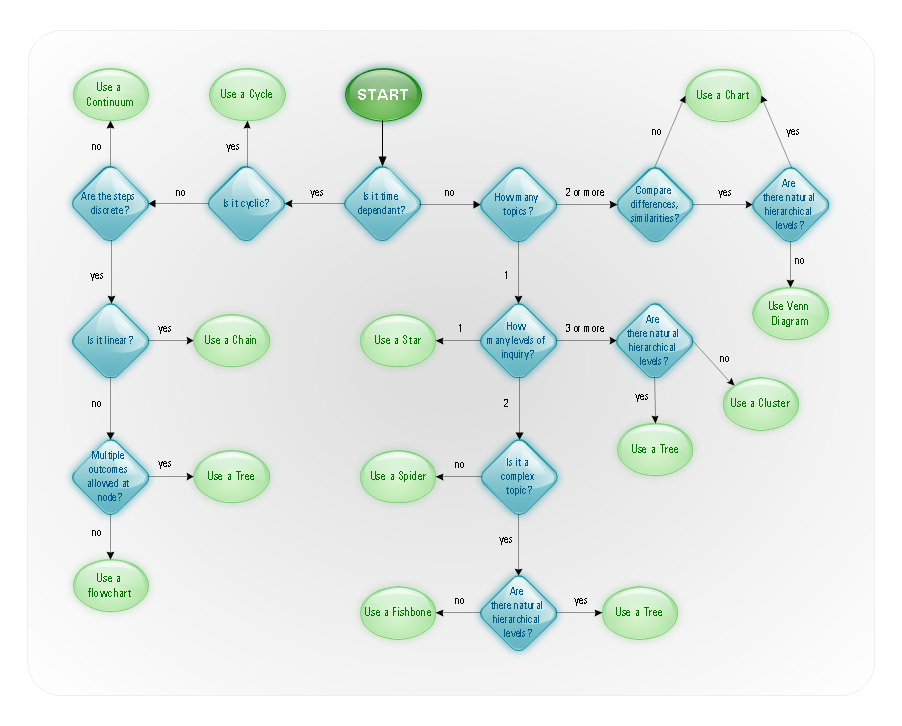
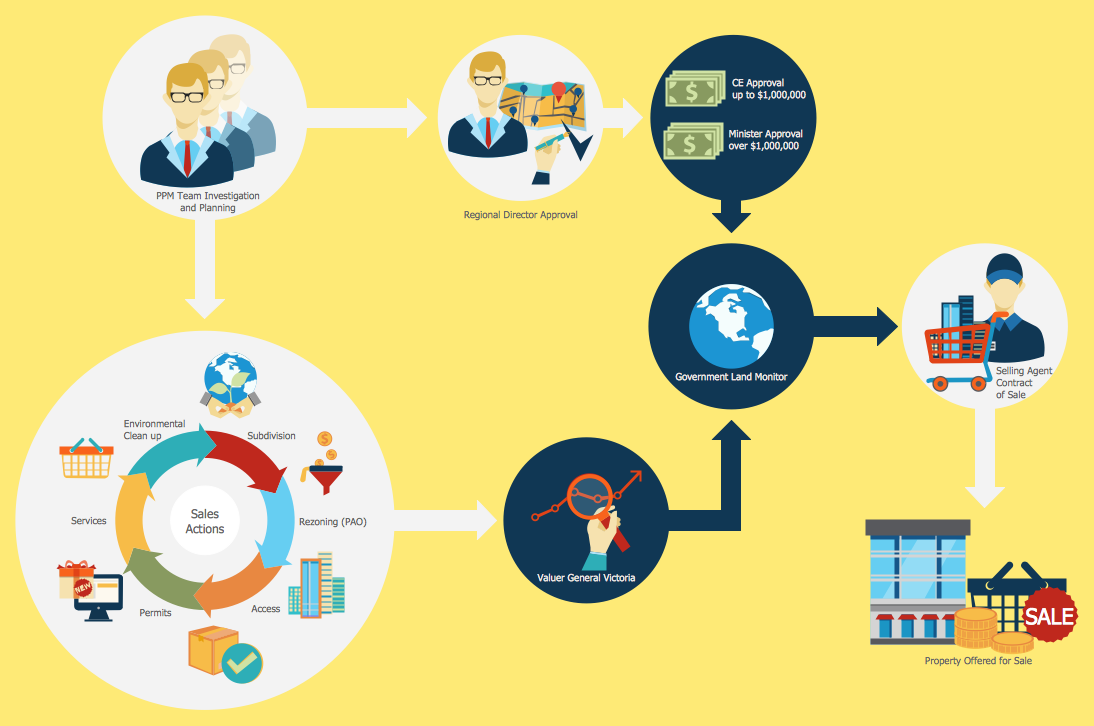
Helps to create professionally looking and detailed Sales Flowcharts with all sales steps visually represented on them.
Use the Sales Flowcharts Solution for ConceptDraw DIAGRAM software to create your own Sales Flowcharts of any complexity quickly, easily and effectively to use them successfully in your work activity.
ConceptDraw DIAGRAM diagramming and vector drawing software supplied with unique Sales Flowcharts solution from the Marketing area of ConceptDraw Solution Park allows fast and easy visualize all sales steps of the sales process on a sales process Map or sales process flowchart, and then realize them easily.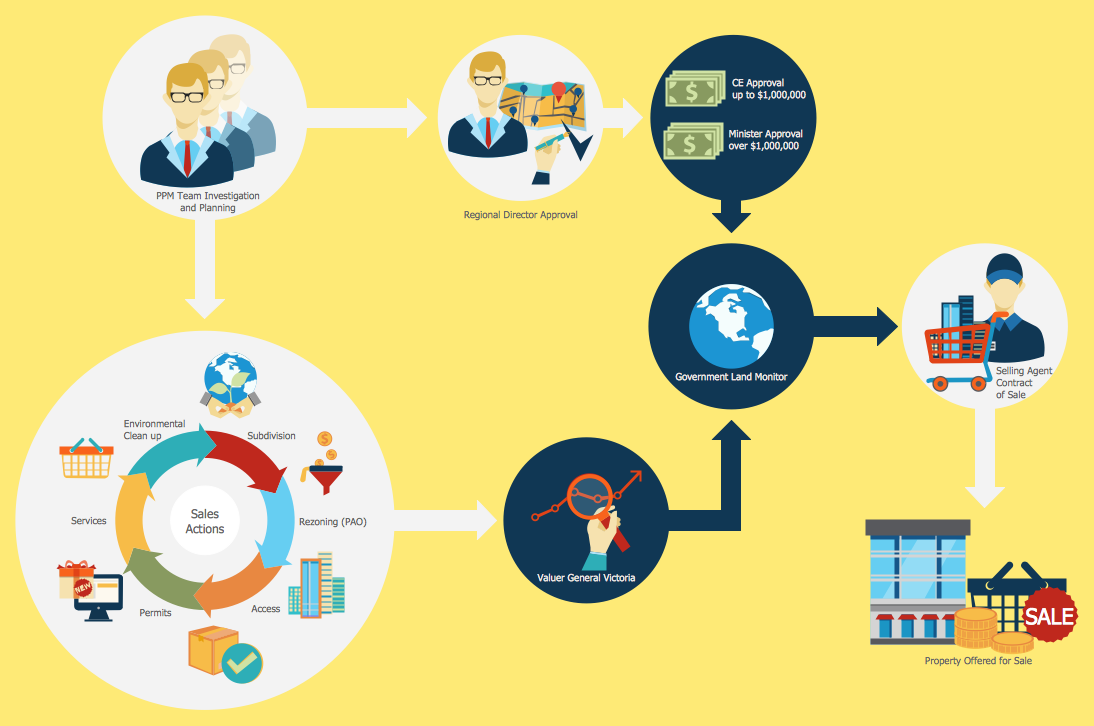
Picture: Sales Steps
Related Solution:
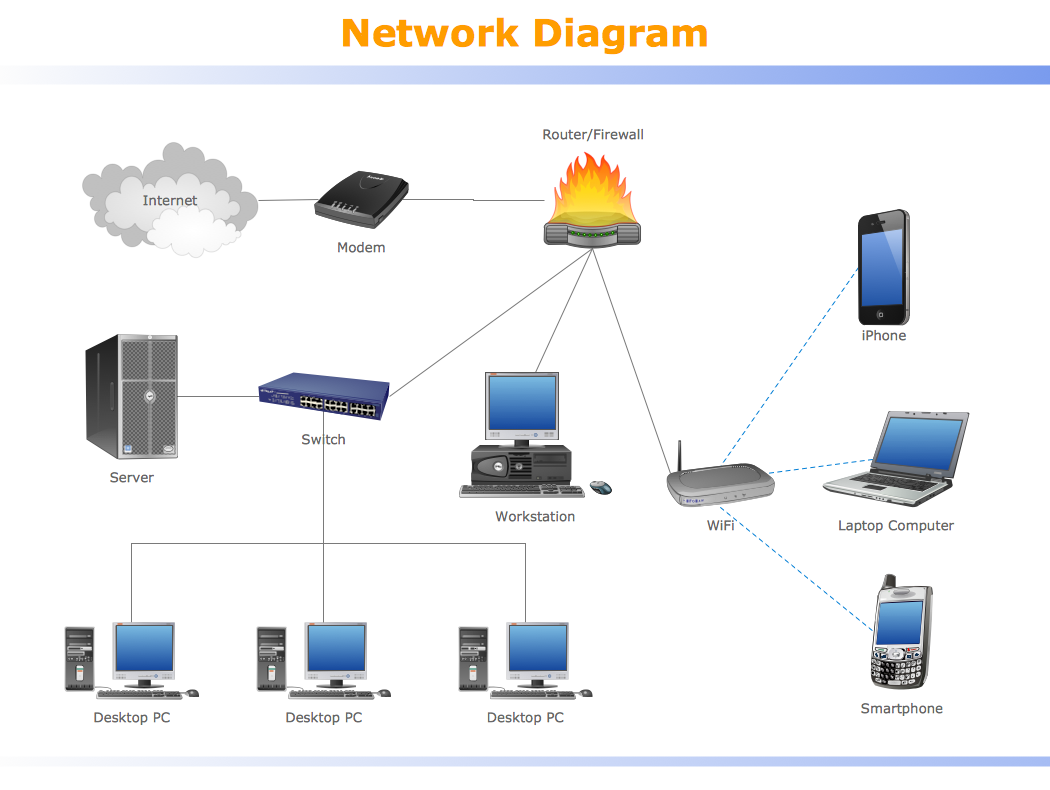
Special libraries of highly detailed, accurate shapes and computer graphics, servers, hubs, switches, printers, mainframes, face plates, routers etc.
Use ConceptDraw DIAGRAM with Computer & Networks solution for drawing LAN and WAN topology and configuration diagrams, Cisco network diagrams, network wiring schemes and floor plan layouts.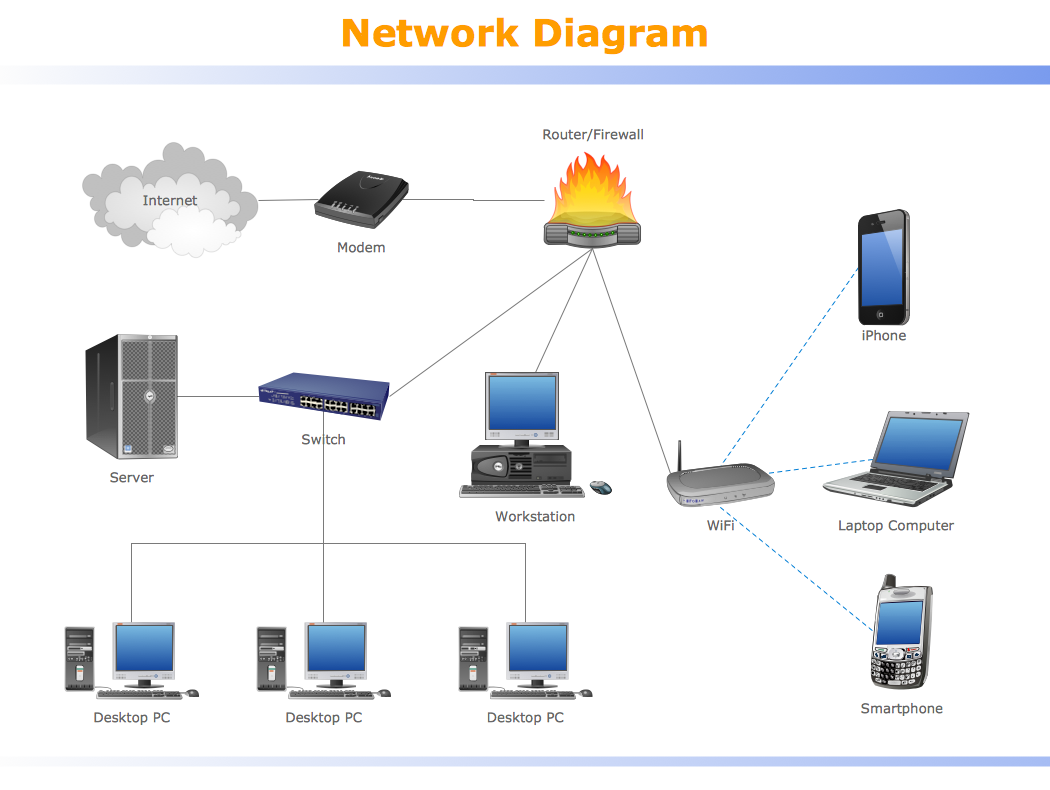
Picture: How To use Switches in Network Diagram
Related Solution:
This diagram represents the electrical floor plan. This is a common practice - to draw the electrical plan on the floor plan. The outlets, fixtures and other electrical equipment are depicted on the floor plan with special symbols. This drawing was created using the possibilities of ConceptDraw DIAGRAM as CAD software. Computer-aided design software is intended to replaces manual engineering drafting with an automated process. CAD software is used by engineers, architects, and others to make high-precision technical drawings and illustrations. CAD software allows technical specialists to develop, examine and manage various engineering projects.
It is almost impossible nowadays to imagine mechanical engineering without digital technologies. Finding a suitable CAD software for creating mechanic diagram and electrical diagram architectural designs can take a lot of time and effort. However, with ConceptDraw DIAGRAM you can create any diagram that you want and later convert it to the most popular graphic formats like.vsdx,.png,.pptx etc.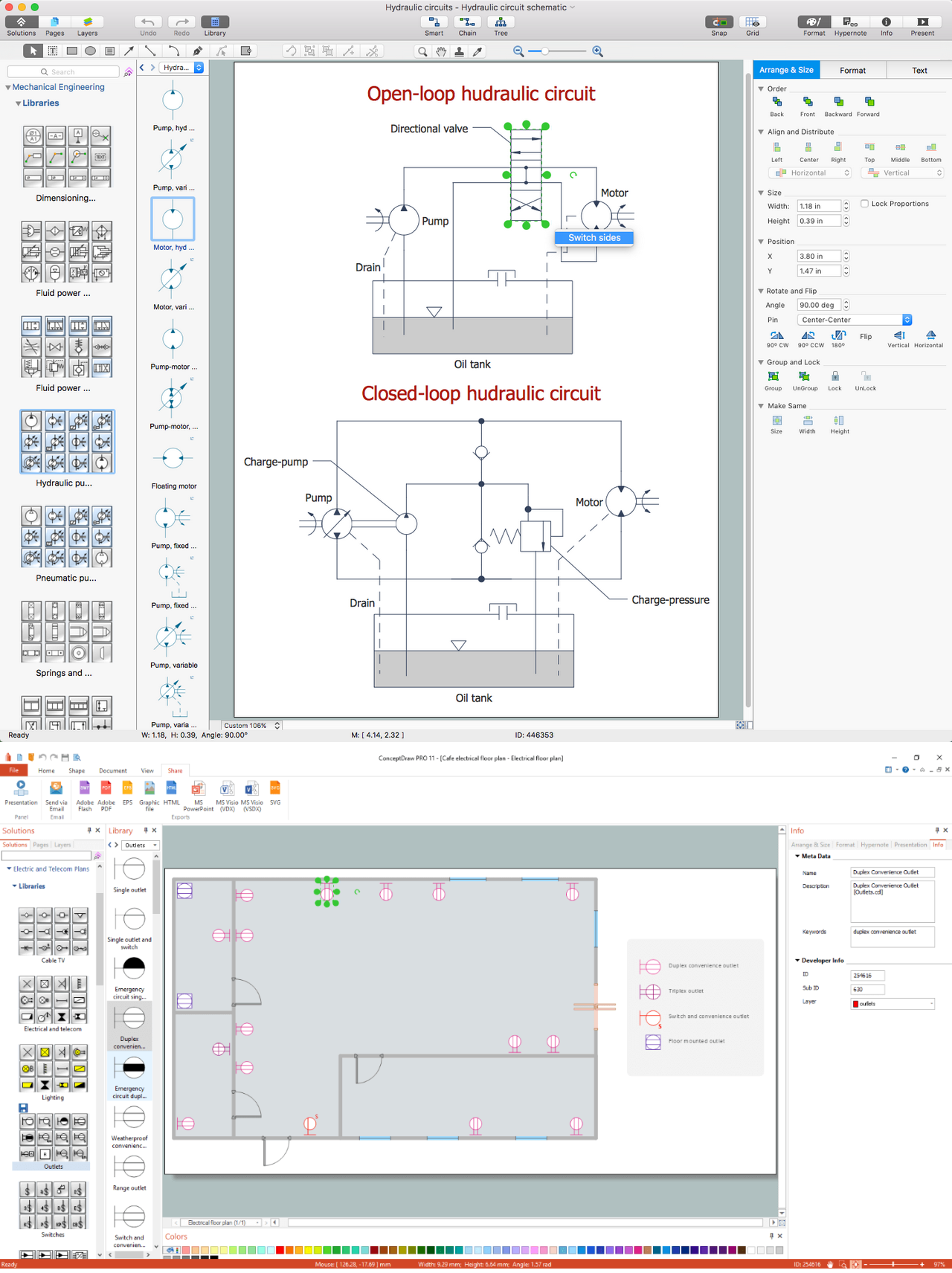
Picture: CAD Drawing Software for Making Mechanic Diagram and Electrical Diagram Architectural Designs
Related Solution:
ConceptDraw MINDMAP is the Note Exchange Solution, a feature that allows quick and easy export of MINDMAP documents through Evernote.
Picture: Evernote & Exchange Integrations
Related Solution:
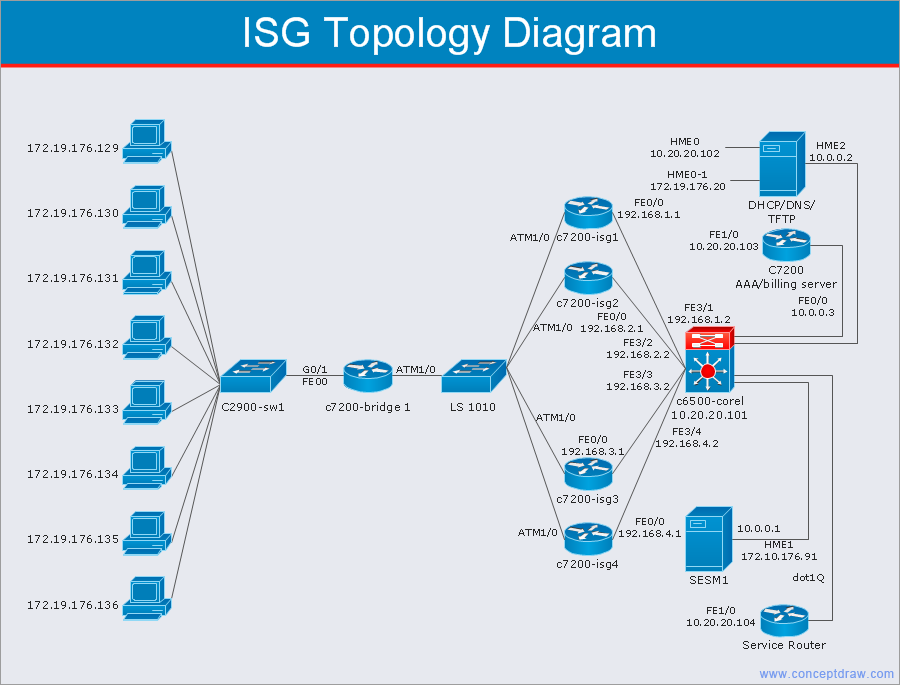
A network diagram is used to depict the topology of a computer network or, talking more broadly, any telecommunications network in general. In order for a computer network diagram to be understandable, clearly identifiable icons must be used for each network appliance. Cisco network templates, also called Network Topology Icons, is a brand of symbols developed and used by Cisco. Since Cisco Systems is the largest networking company in the world, it's list of networking symbols is widely recognized and exhaustive.
The diagram of the ISG network topology diagram illustrates the Cisco Intelligent Services Gateway. Since Cicso company offers service providers a possibility to provide control of state and resources in a broadband network, network architects and engineers need some facilities to create ISG topology diagrams.This Cisco ISG network diagram was created in ConceptDraw DIAGRAM using its solution for Cisco network diagrams. The vector library of this solution comprises over 500 icons of Cisco hardware and accessories. They can be used to design LAN, WAN, ISG and other Cisco equipped network diagrams.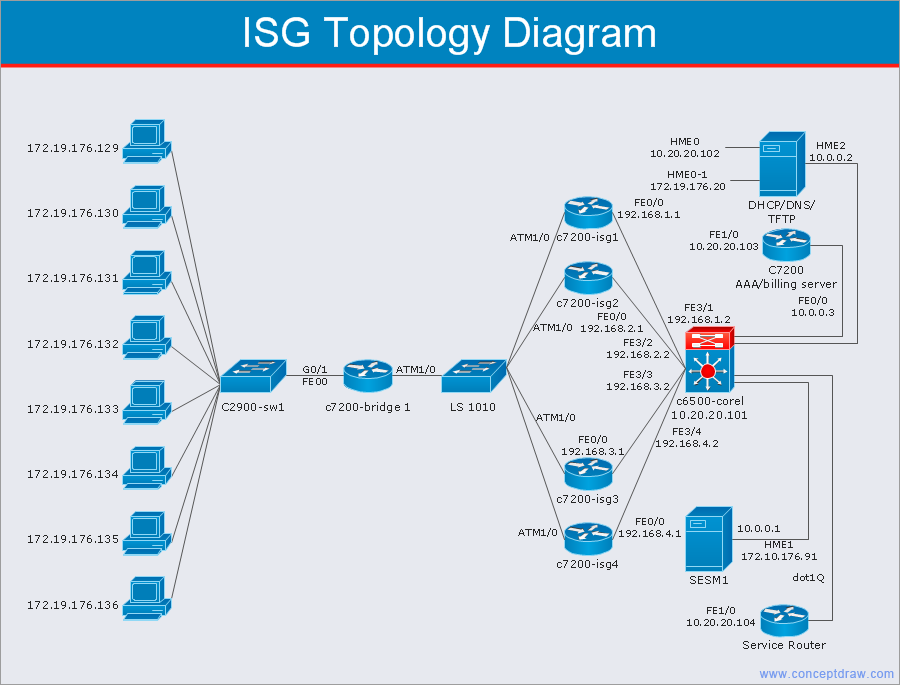
Picture: Cisco Network Templates
Related Solution: