Network Security
The Internet is a giant computer network which connects computers all over the world. Now the Internet is widely used in all spheres of the life and activity, it is first of all a way to exchange information, without which today is difficult to imagine the life. The Internet is integral part of human society and business. But the serious question for network engineers, designers, lawmakers and enforcers is the need for protect the Internet networks from the Internet crimes, hacking and attacks.
There are many kinds of dangers and ways of attacks, but there are also quite a number of hardware, software and physical methods of protection against them. Such devices as routers, IDS and Firewalls are examples of hardware devices used for network security. Anti-virus software and VPNs are some of the software network security tools.
One of the most effective and easily implemented ways to protect the networks is the use of Firewalls. The Firewall is a first line of defense against the external threats to networks, it can be either software based or hardware based. The main task of firewall is to allow the authorized access to a computer while blocking unauthorized access. The Network layer firewalls makes decisions based on the source address, destination address and ports in individual IP packets. Modern network layer firewalls maintain internal information about states of the connections passing through them.
Depending of the service kind and security you need for your network, you can choose the type of firewall. The most useful types of firewalls are: Screened host firewall, Screened subnet firewall, Packet filer firewall, Stateful inspection firewall, Hybrid firewall, Proxy server firewall, Application level (gateway) firewall.
ConceptDraw DIAGRAM is a powerful diagramming and vector drawing software that allows quick and easy draw the diagrams of your safe networks.

Example 1. Network Security
Computer and Networks Area provides the Network Security Diagrams solution that contains the libraries with a great number of predesigned vector stencils, a set of professional looking examples that you can change for your needs.
All numerous predesigned Network Security Diagram samples are available from ConceptDraw STORE. Use of ready sample is the most simply and quick way of drawing diagrams, you can start with ready sample and change it according to your taste and needs.
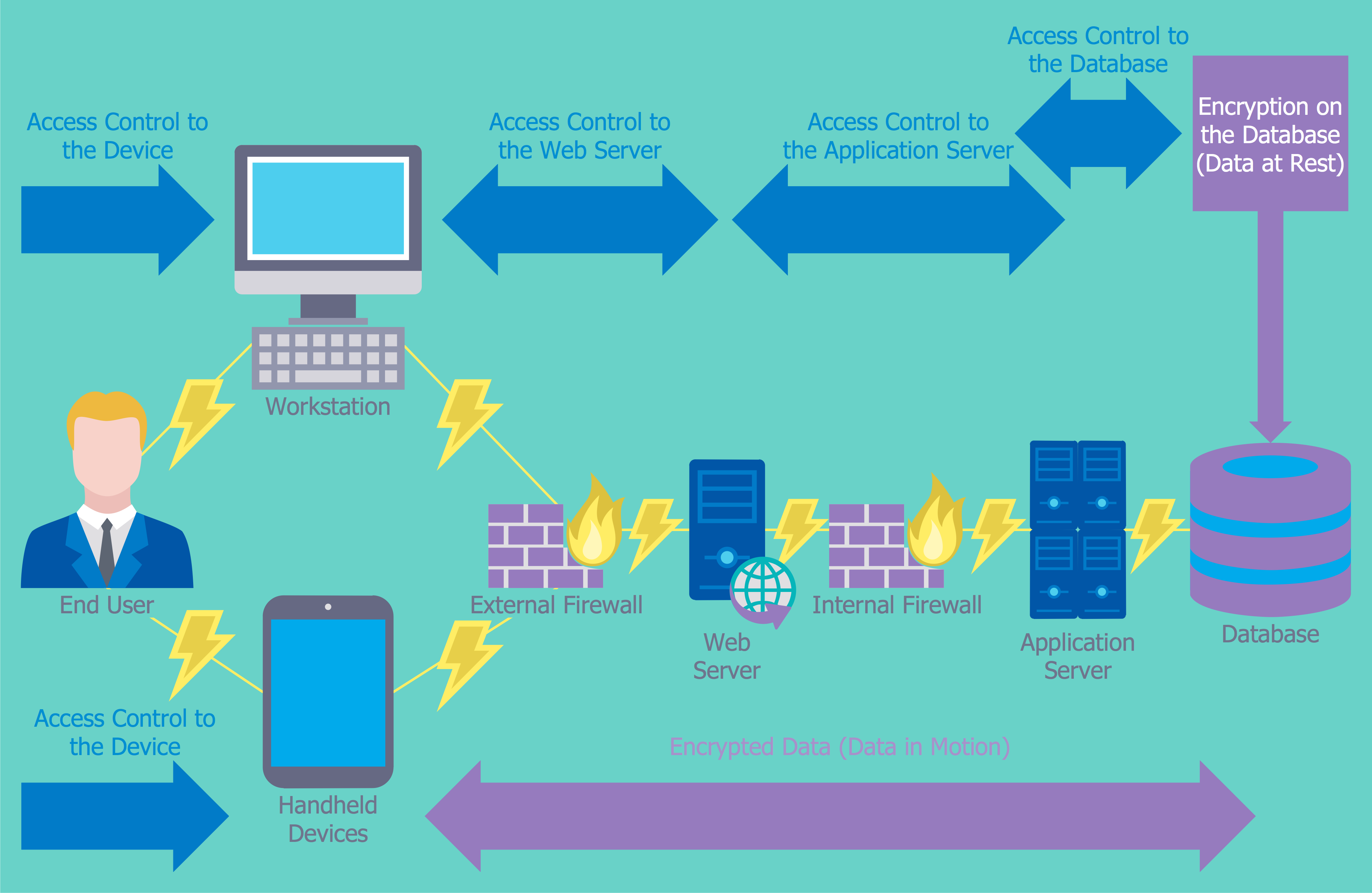
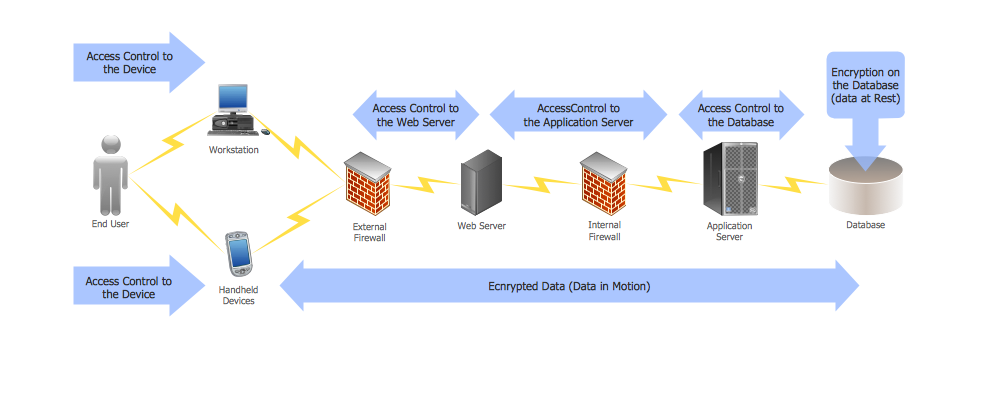
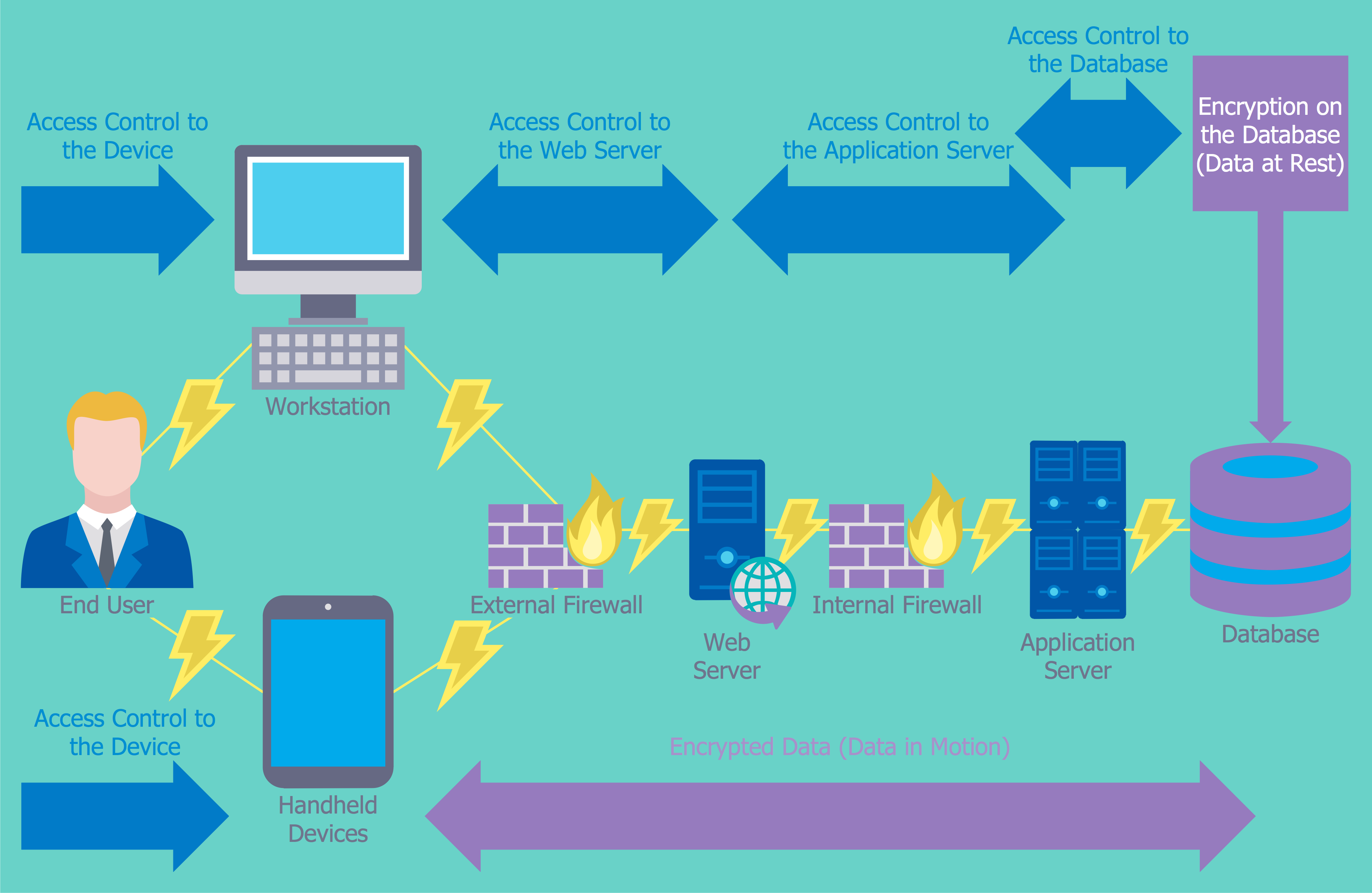
Example 2. Network Security Diagram - Access Control and Encryption
The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software. They show protection networks with Firewalls and other network security devices. An experienced user spent 5-10 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Diagrams quick, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.
TEN RELATED HOW TO's:
You need to draw a Functional Flow Block Diagram? You are an artist? Now it doesn't matter. With Block Diagrams solution from the Diagrams area for ConceptDraw Solution Park you don't need more to be an artist to design the Functional Flow Block Diagram of any complexity.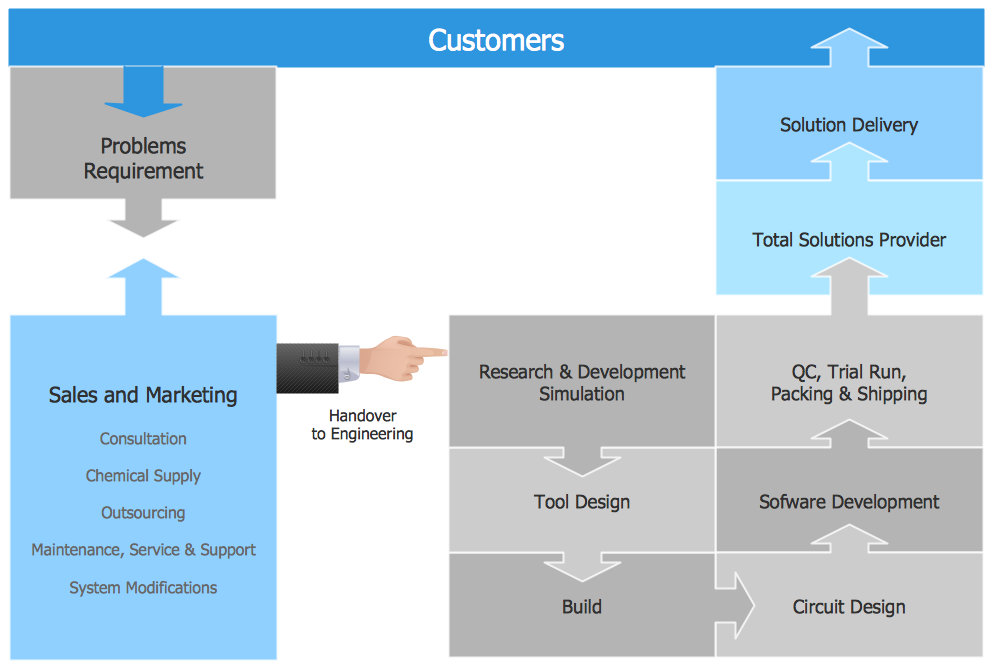
Picture: Functional Flow Block Diagram
Related Solution:
ConceptDraw provides some interactive xy chart and scatter graph symbols that offers advanced features yet is simple to use.
Picture: Scatter Graph Charting Software
Related Solution:
29095The Data Encryption Standard (DES) is a symmetric-key algorithm for the encryption of the electronic data.
This diagram was created in ConceptDraw DIAGRAM using the Computer and Networks Area of ConceptDraw Solution Park and shows how the encryption and access control work together to secure data.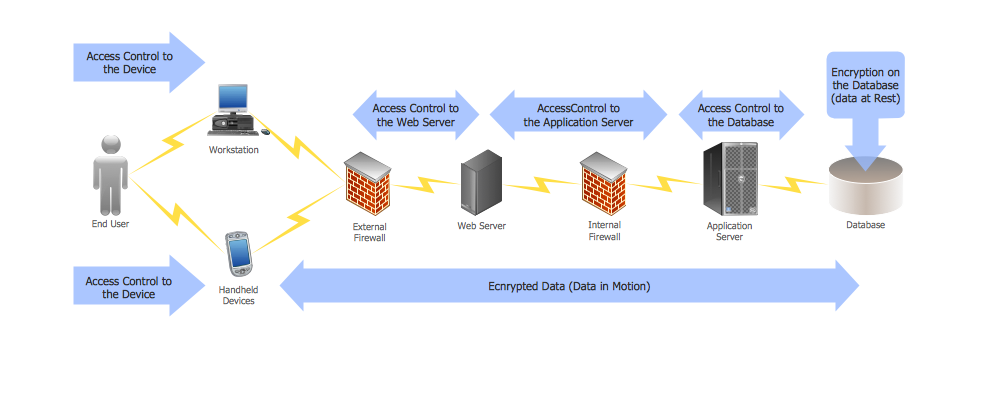
Picture: DES Network. Computer and Network Examples
Related Solution:
Fast visualization of structured data is main capability of the ConceptDraw DIAGRAM. With numerous vector stencils and standard flowchart symbols from object libraries and the RapidDraw technology this program stands as the best professional flowchart software for drawing with type of flowchart symbols. ConceptDraw DIAGRAM also known as best flowchart maker.
Picture: Easy Flowchart Program and Standard Flowchart Symbols
Related Solution:
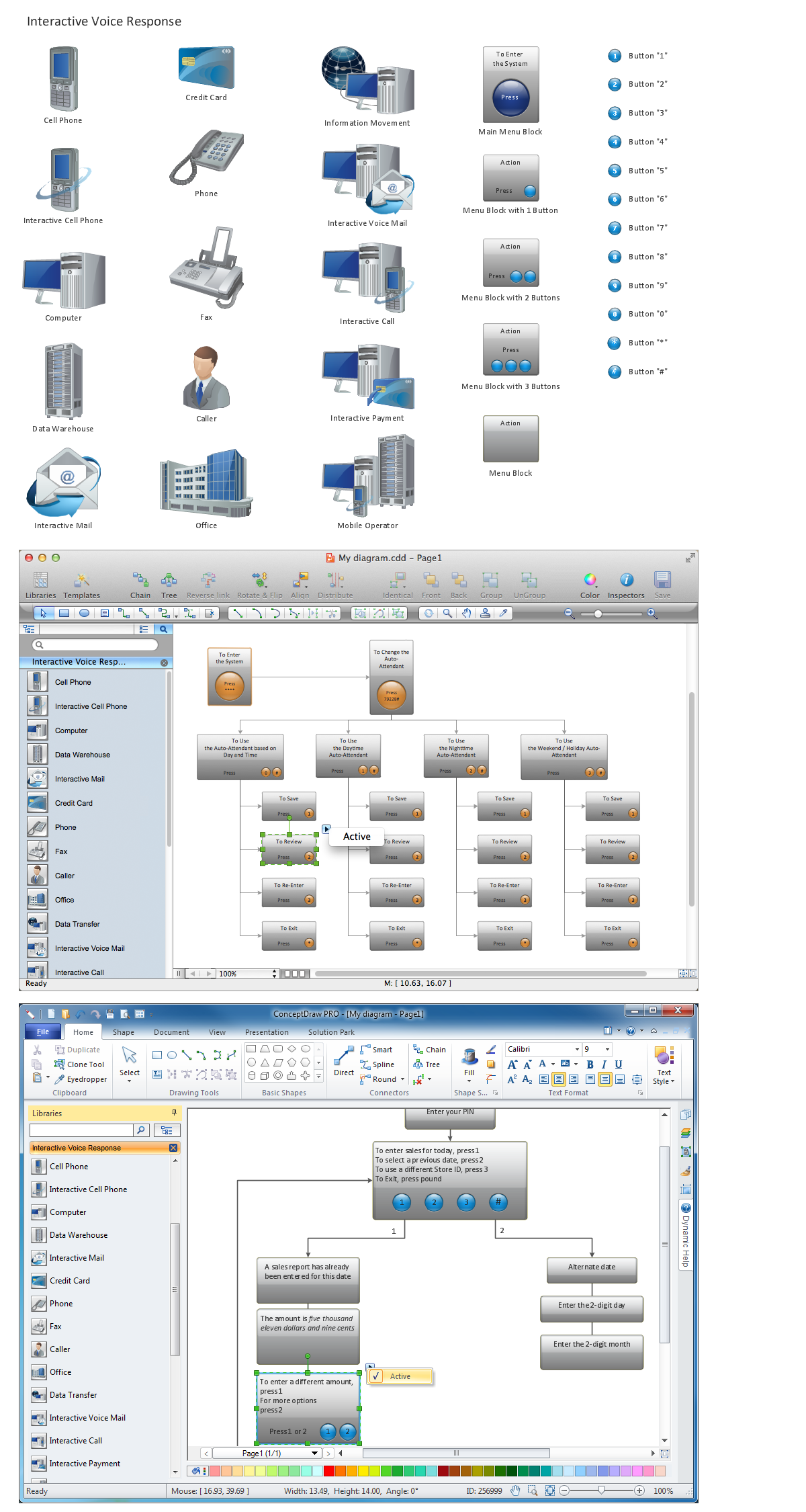
ConceptDraw DIAGRAM is perfect for software designers and software developers who need to draw IVR Network Diagrams.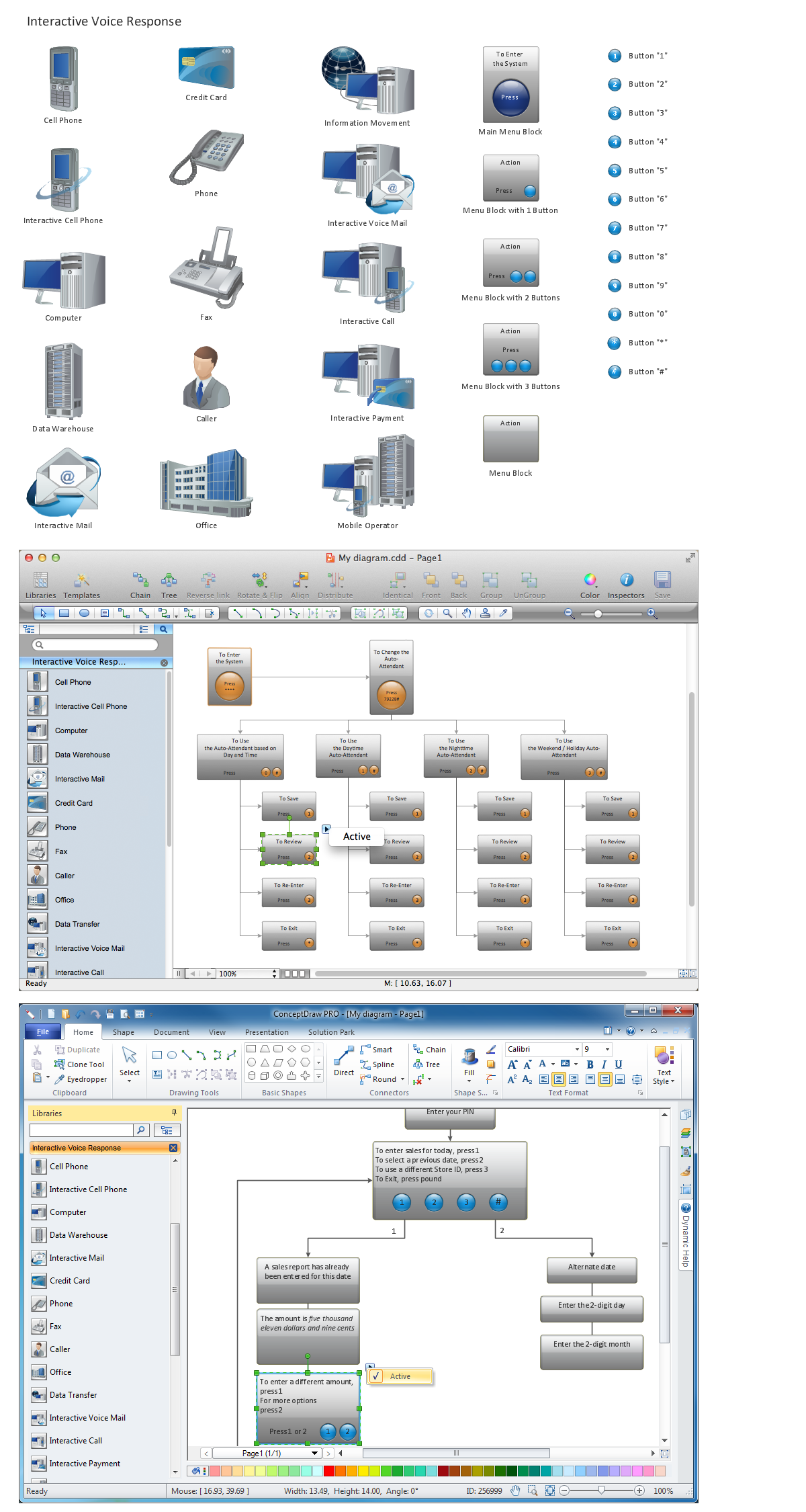
Picture: Network Diagramming Software for Design IVR Network Diagrams
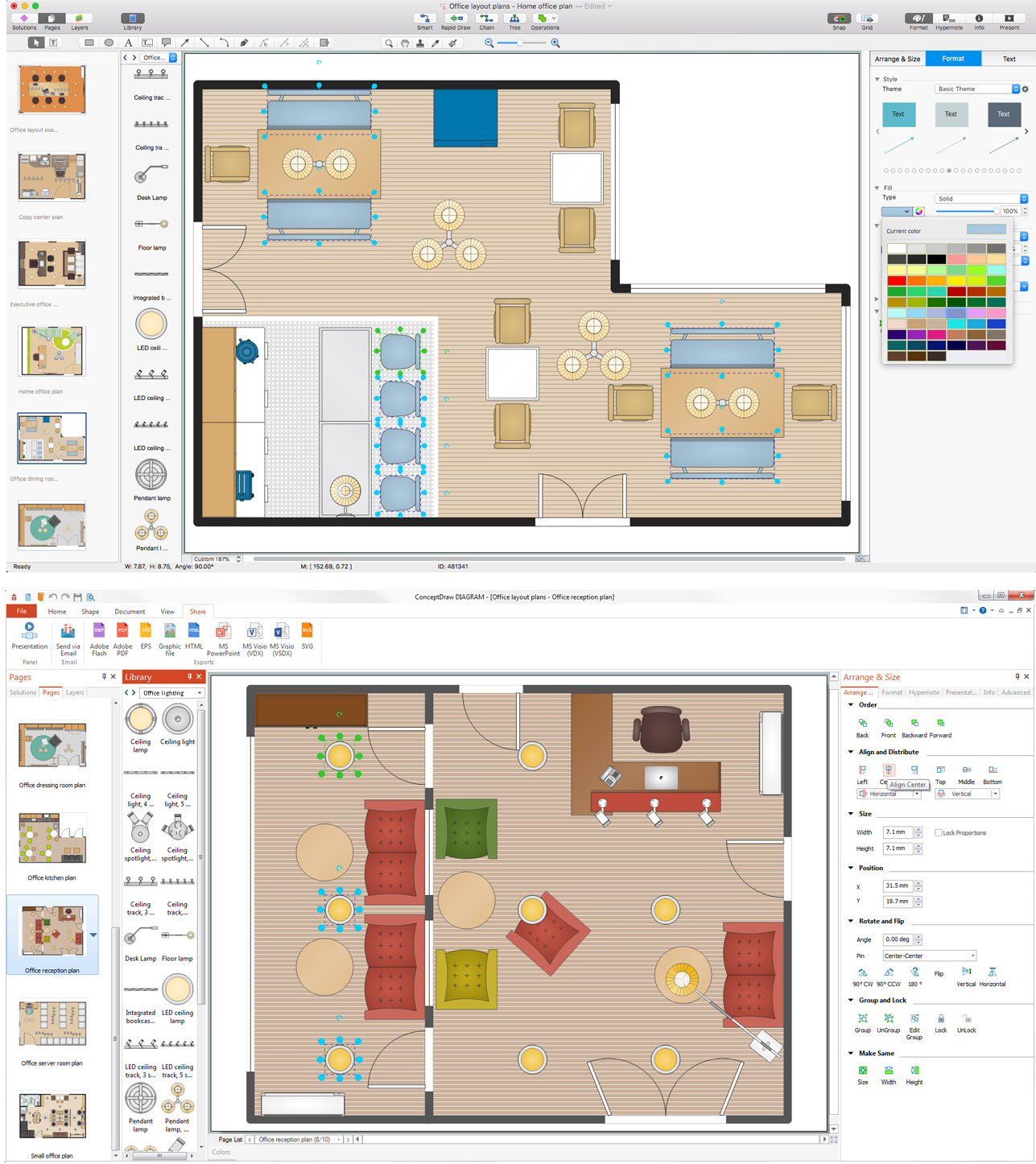
Cabinet is a necessary room in the house. It is very important that the cabinet was comfortable and convenient with elaborated design that dispose to the maximize productive work. The cabinet design is a reflection of the personality, habits and character traits of its owner.
Floor Plans Solution provides templates, samples and wide collection of pre-designed vector stencils that allow you to create the cabinet design plans of any complexity quick, easy and effective.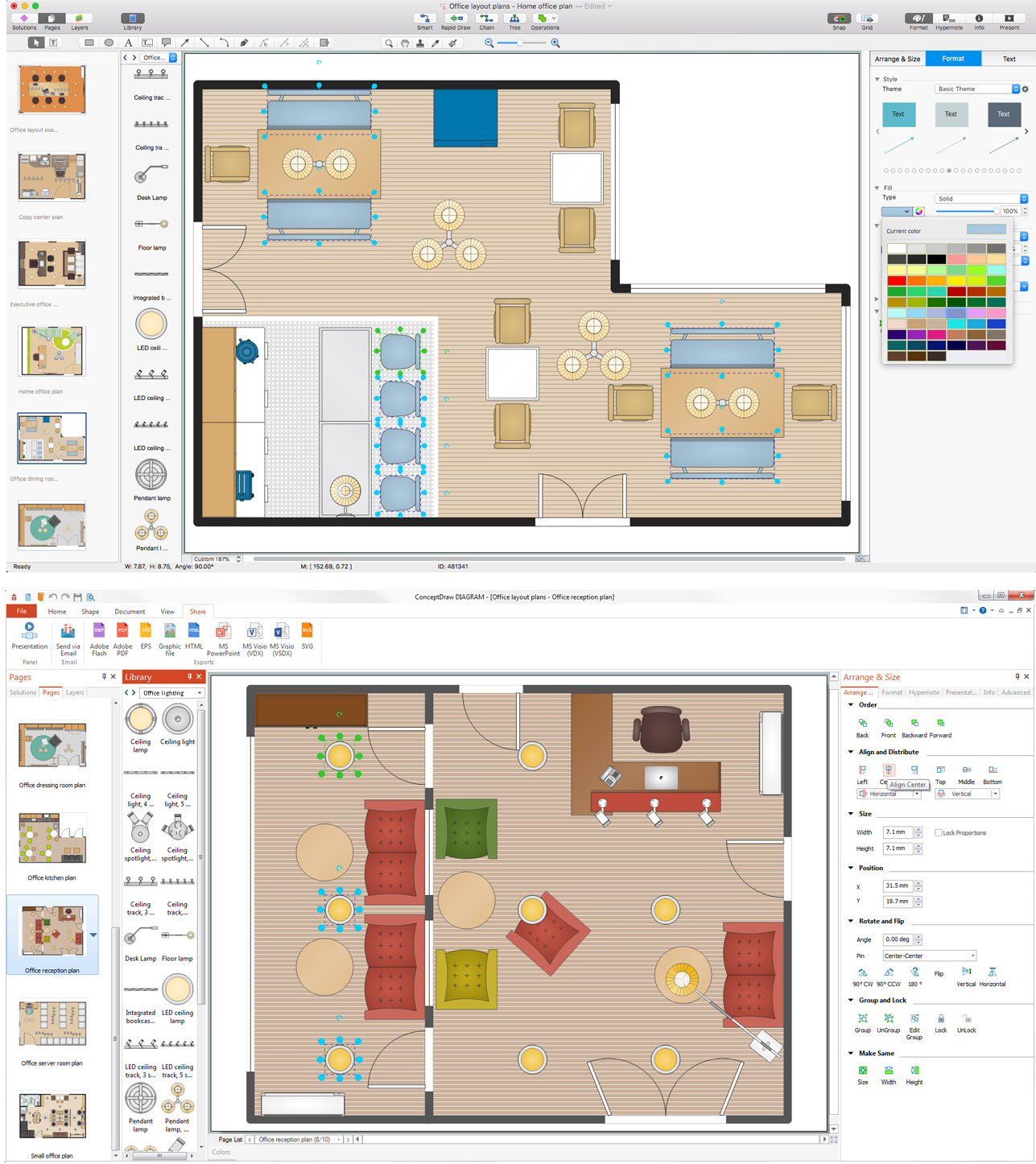
Picture: Cabinet Design Software
Related Solution:
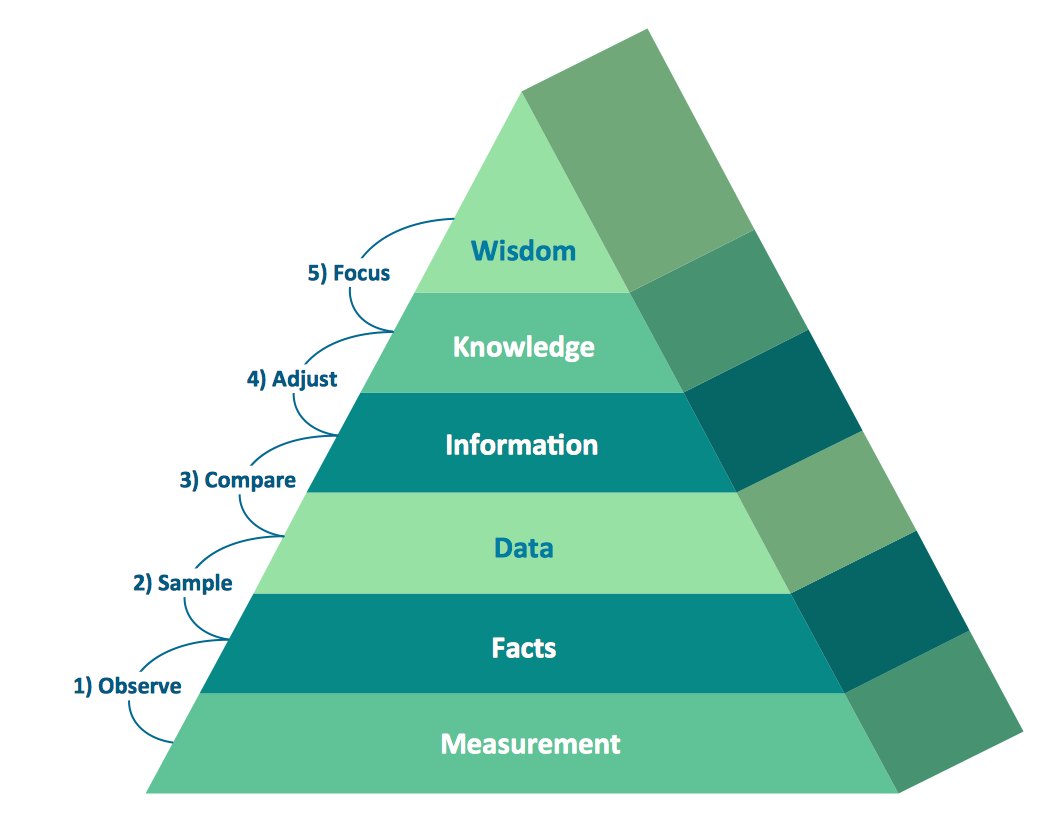
Pyramid diagrams help you visualize information as a triangle divided into horizontal slices. Labelled slices represent a hierarchy. Pyramids are used in marketing presentations to show and analyze hierarchy levels.
3D triangular diagram of DIKW pyramid has 6 levels: measurement, facts, data, information, knowledge, wisdom.
The data component include different scattered signs or symbols which are merely useless until these random objective facts are somehow processed. Data is a resource which has to be manipulated or rearranged to get useful. Information can be extracted from a pile of data, it also can be mined from different data storages.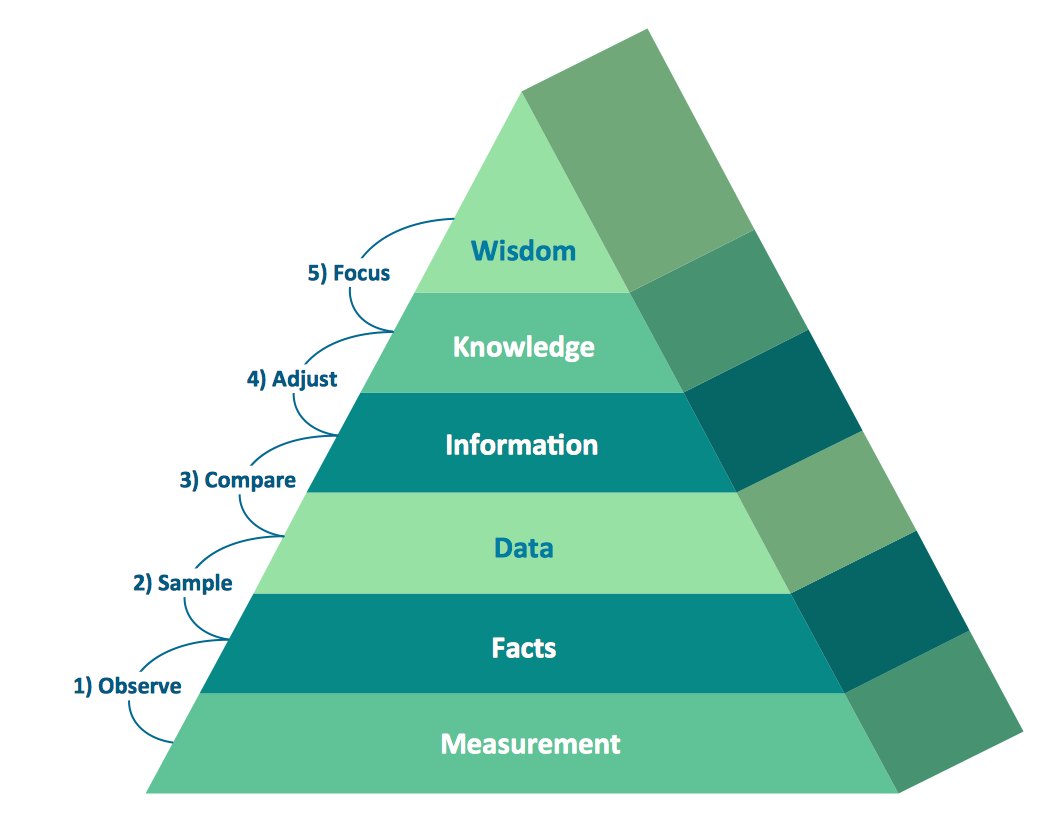
Picture: Pyramid Diagram
Related Solutions:
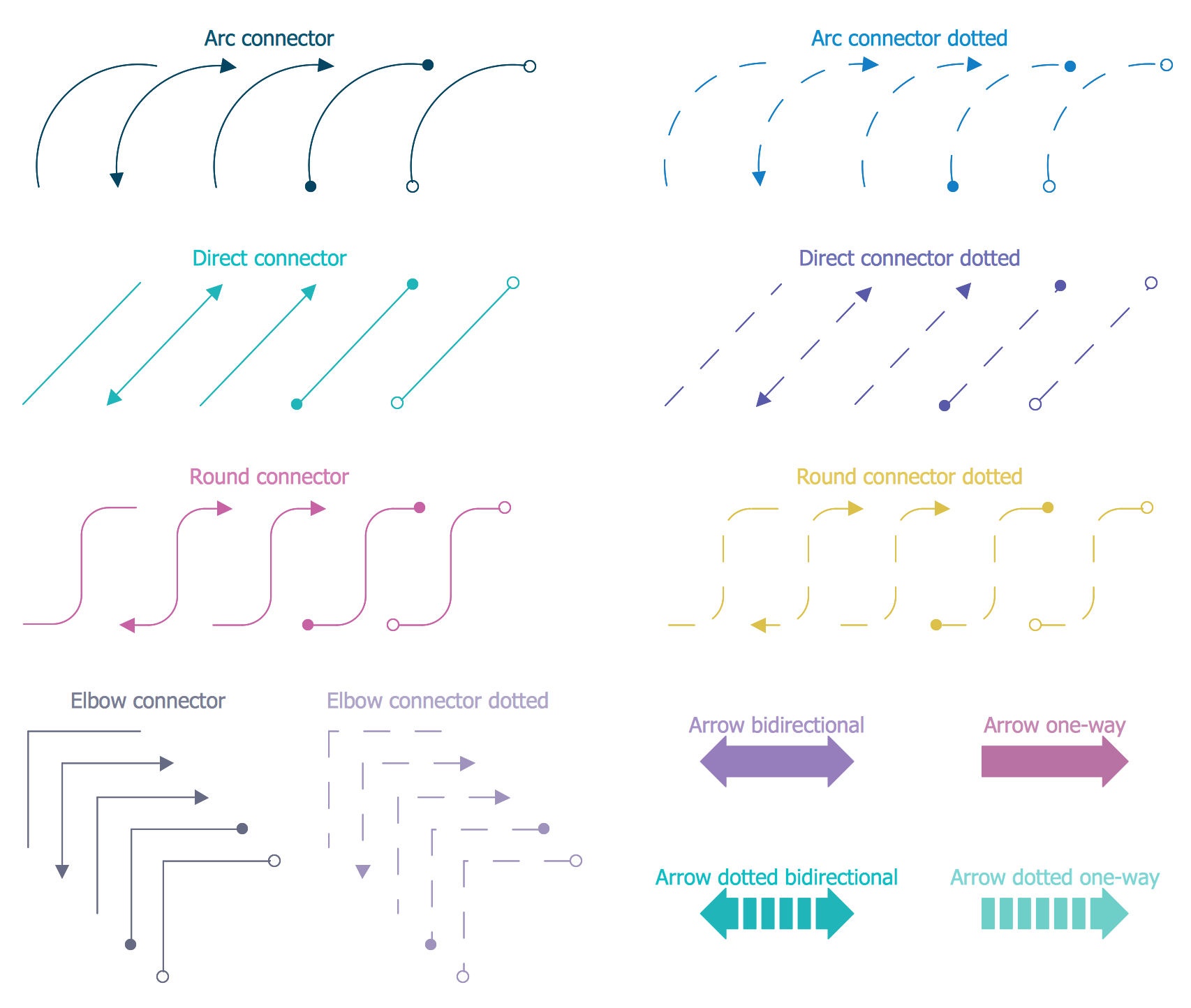
New Smart connectors in ConceptDraw DIAGRAM now have an auto-routing feature. This means that connectors always find the optimal route between objects and automatically recalculate that path when moving these objects.
You don't have to think about your connectors, they think for you.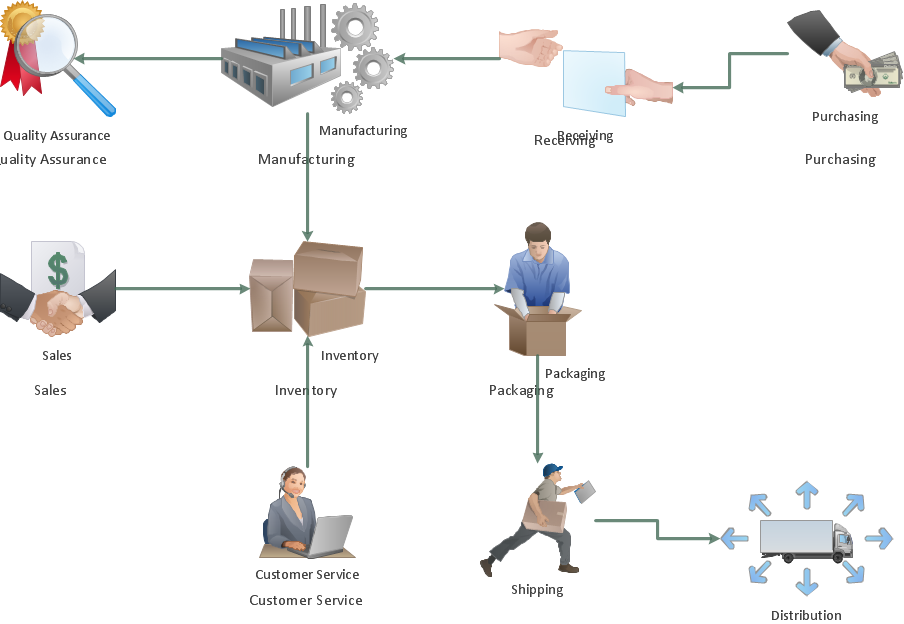
Picture: ConceptDraw Arrows10 Technology
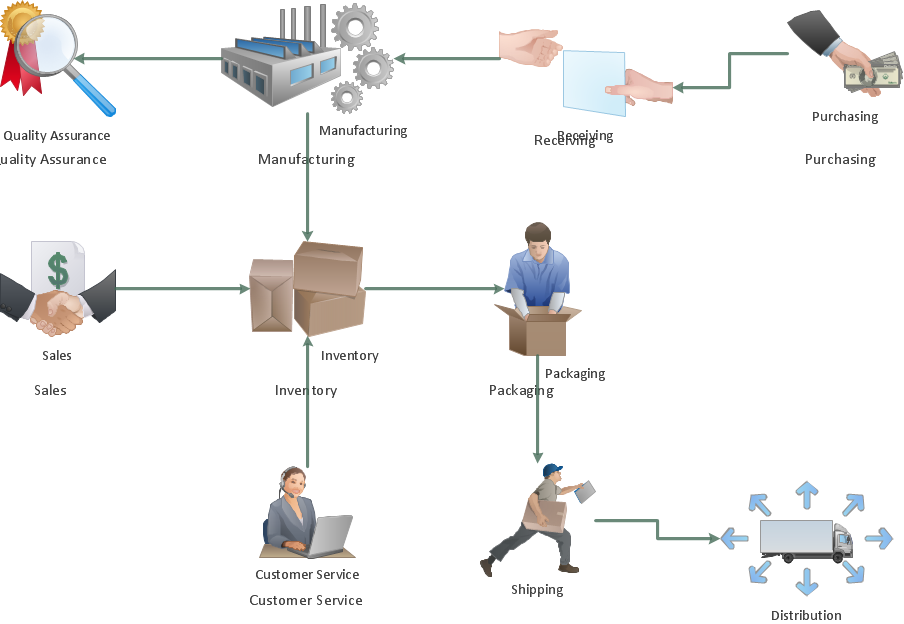
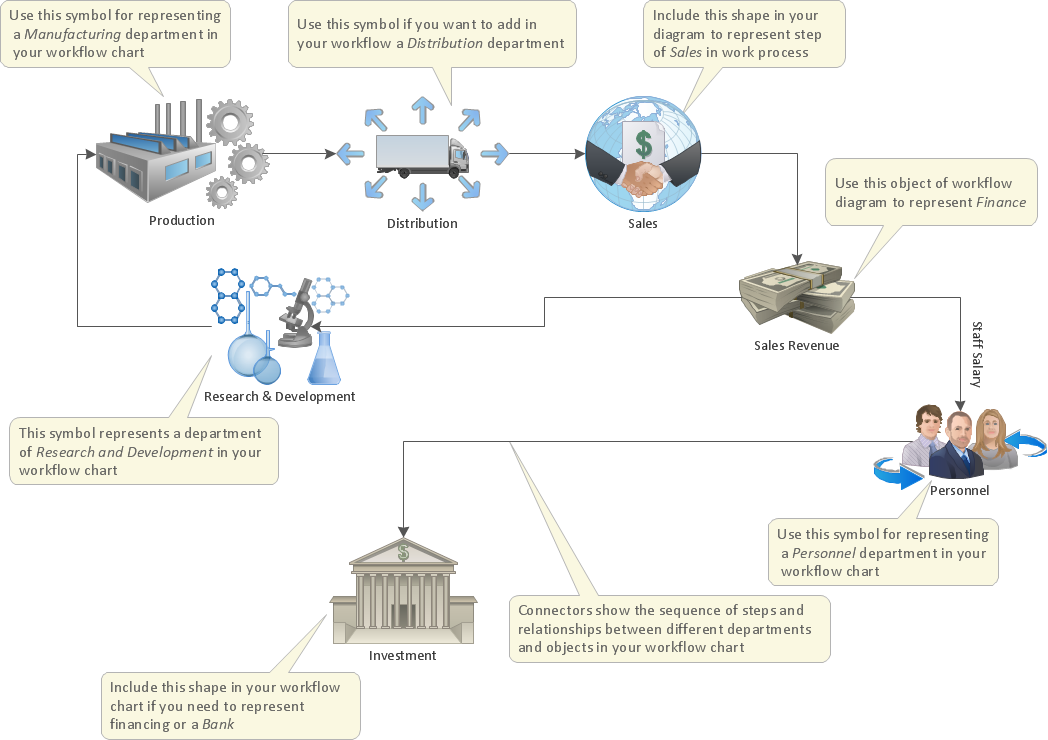
The first step to optimize a workflow is to get its visual depiction. Then you can analyse and optimize the workflow making changes to your workflow diagram. We recommend to use ConceptDraw DIAGRAM software extended with the Workflow Diagram solution to visualize and optimize your workflow. It allows you produce easy-to-change scalable vector graphic workflow and then present it to your team or partners.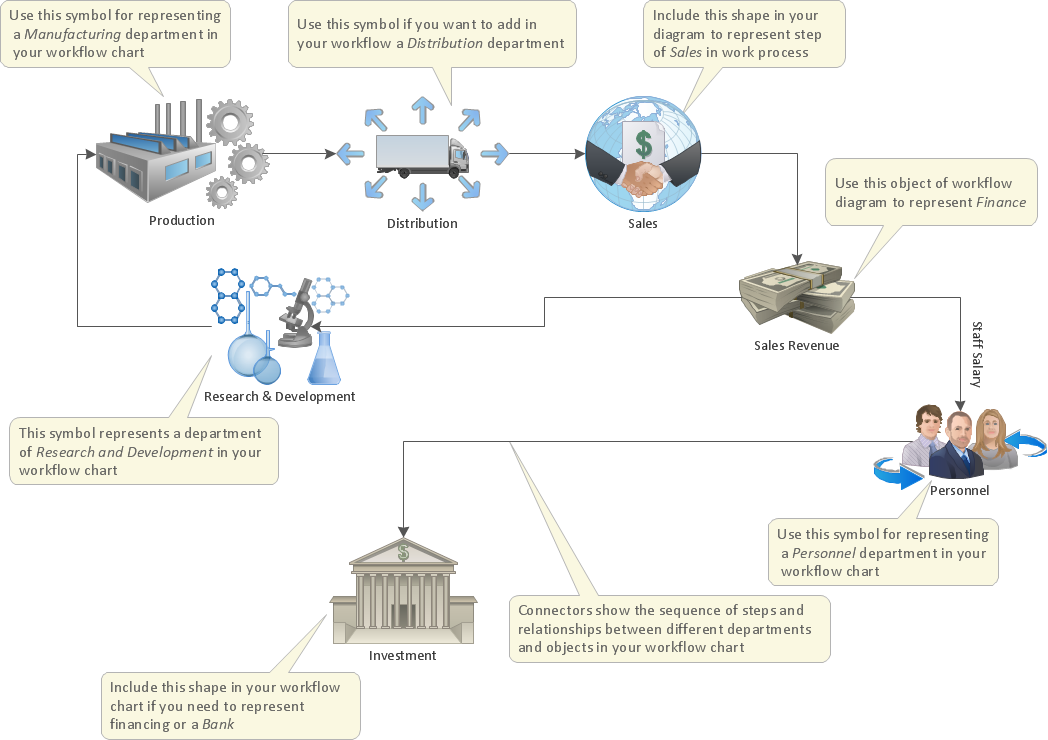
Picture: Optimize a Workflow
Related Solution:
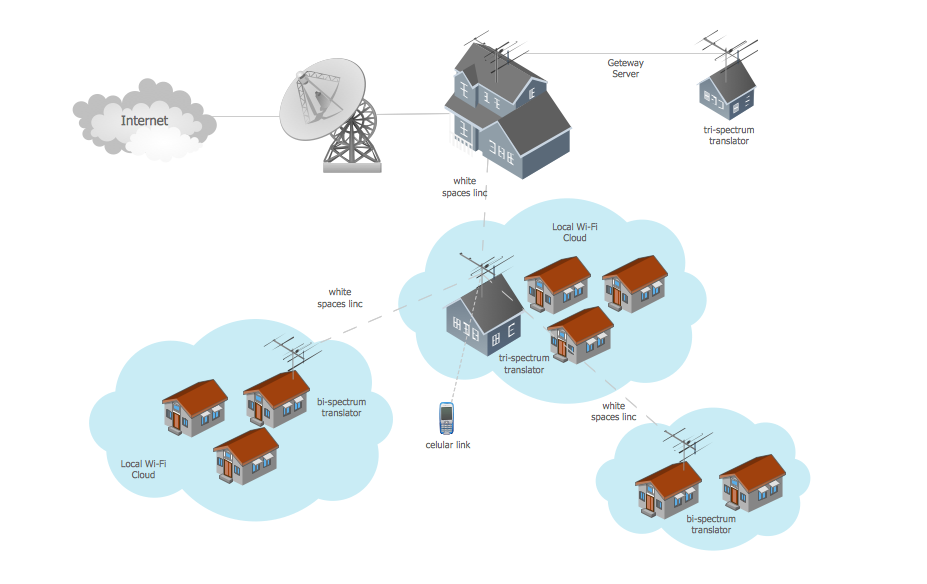
Studying informatics demands knowledge in the area of computer networks as well. The most famous world network, Internet, is an example of wide area network (WAN) topology that connects devices spread on any distance. Unlike other smaller networks that are limited to a building or to a campus, WAN is almost limitless.
This WAN (wide area network) diagram was created in ConceptDraw DIAGRAM. It shows a telecommunication network that covers a large geographical area connecting several settlements. This type of networks is commonly used by business and government institutions. Using the WANs enables them quickly communicate information between remote geographical points. To reproduce this network diagram, you will need the means, provided by ConceptDraw Computer and Network Diagrams solution.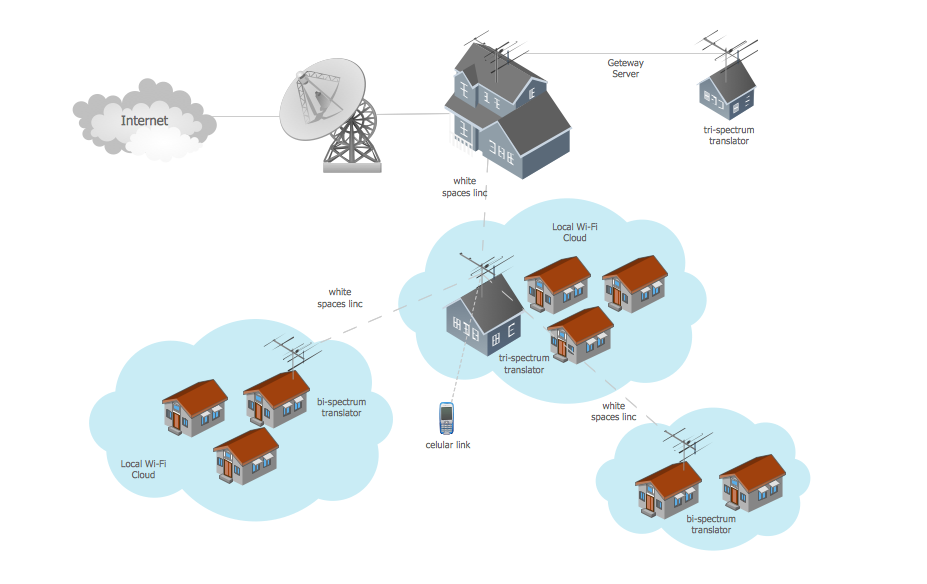
Picture: Wide area network (WAN) topology. Computer and Network Examples
Related Solution: