Network Security Model
The network security involves all tools, devices, strategies and activities which enterprises and organizations undertake to protect their networks, data and operations. An effective network security strategy must include the most effective set of tools for identification and reflection various threats and attacks. Creation of well thought-out network security model will effectively help you in realization your network's security. The network security model (NSM) is a scheme that reflects the general plan and the policy of ensuring the network security, and usually includes all or some of the following seven layers in different modifications according to the specific company's needs:
- Physical layer — involves organization of physical security against the access to the data on computer devices, this can be access control devices, cameras, alarm.
- VLAN layer — involves creation of Virtual Local Area Networks (VLANs) which join together common hosts for security purposes.
- ACL layer — supposes creation and maintenance of Access Control Lists (ACLs) which allow or deny the access between hosts on different networks. Software layer — helps to protect the user layer and ensures the software's actuality.
- User layer — involves the user’s training of security on the network.
- Administrative layer — supposes the training of administrative users.
- IT department layer — this layer is the most important for network security, it contains all network security professionals and support specialists, network technicians and architects, which organize and maintain the work of the network and hosts.
Pay please your attention for the powerful ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park which lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.
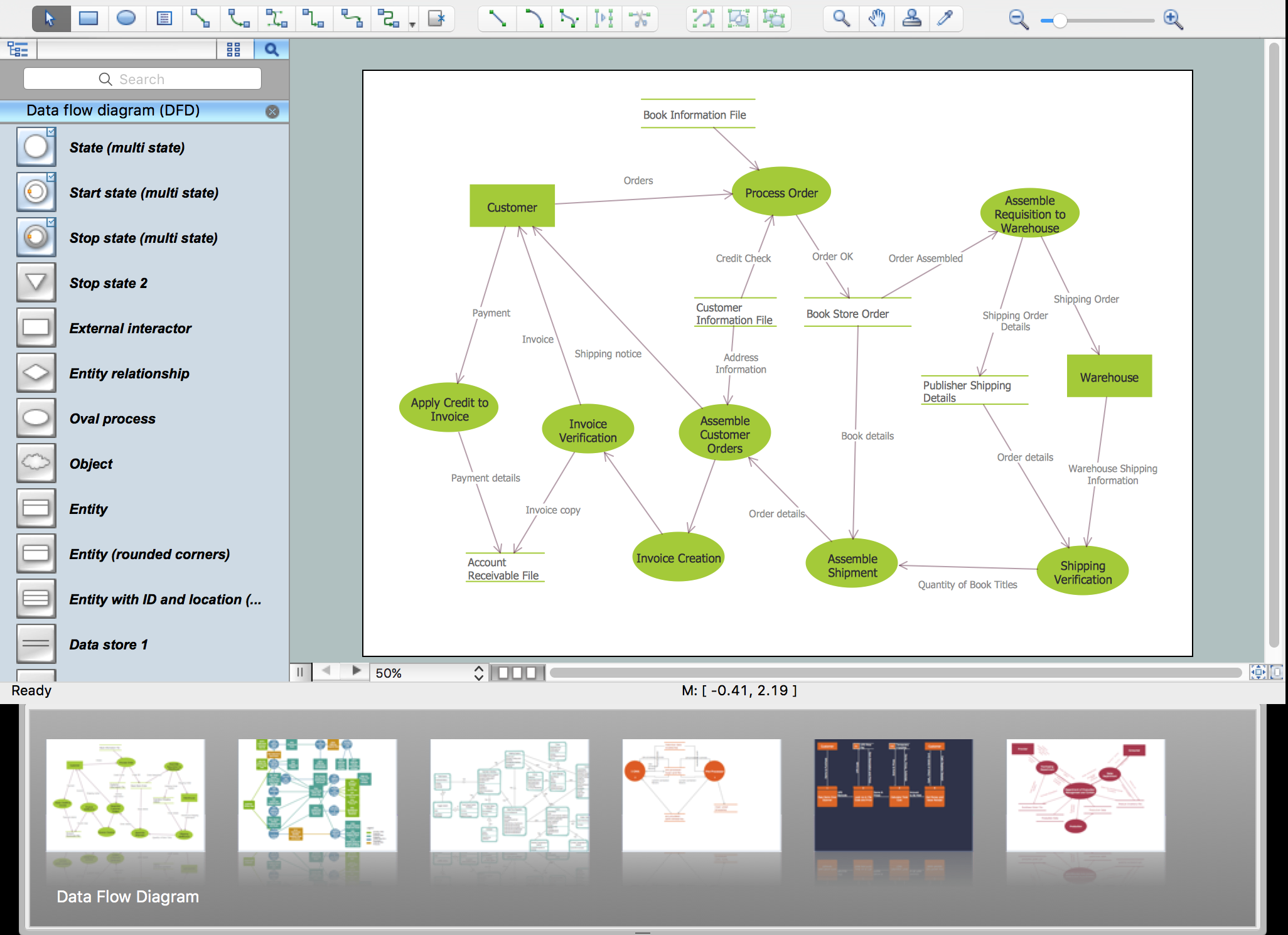
Example 1. Network Security Model
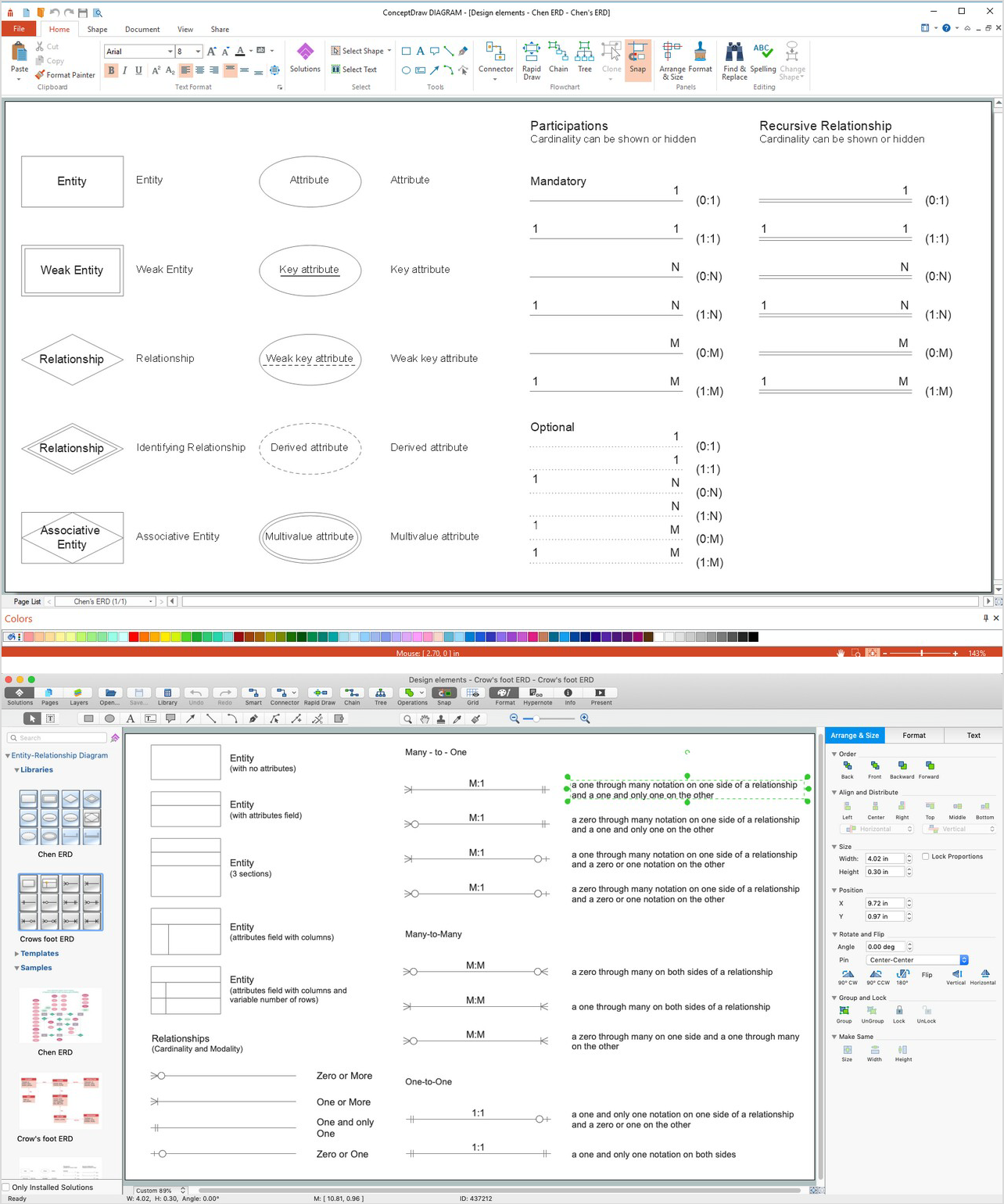
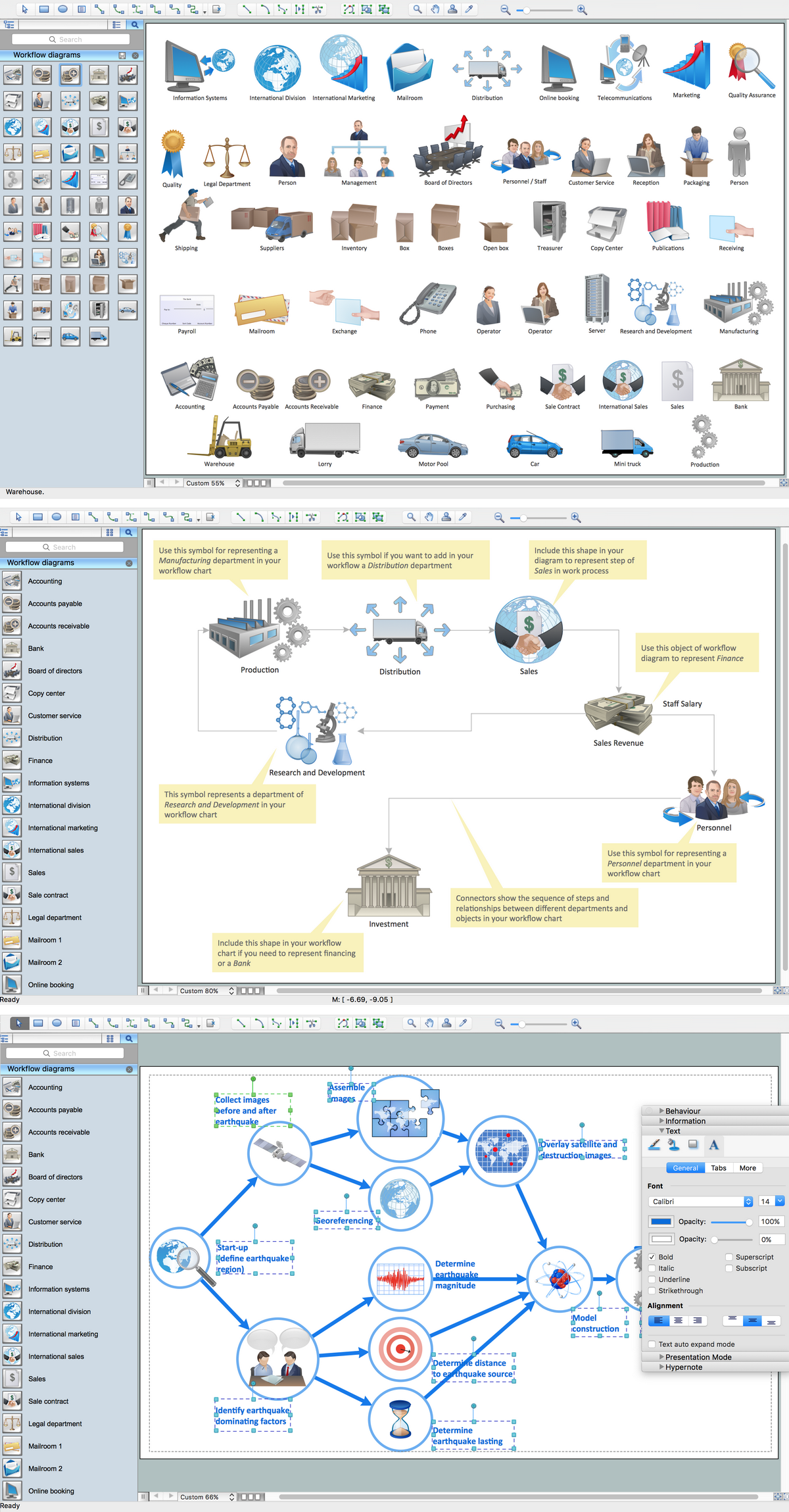
To design the Network Security Model, we recommend to use already ready-to-use 460 predesigned colorful vector objects offered by 4 libraries of the Network Security Diagrams Solution:
- Cybersecurity Clipart
- Cybersecurity Shapes
- Cybersecurity Connectors
- Cybersecurity Round Icons
Simply drag desired objects from the libraries to your document, arrange them, depict relationships between devices with help of connectors from the Cybersecurity Connectors library, type the text and make your diagram more attractive with help of bright colors applied for objects, connectors and background.
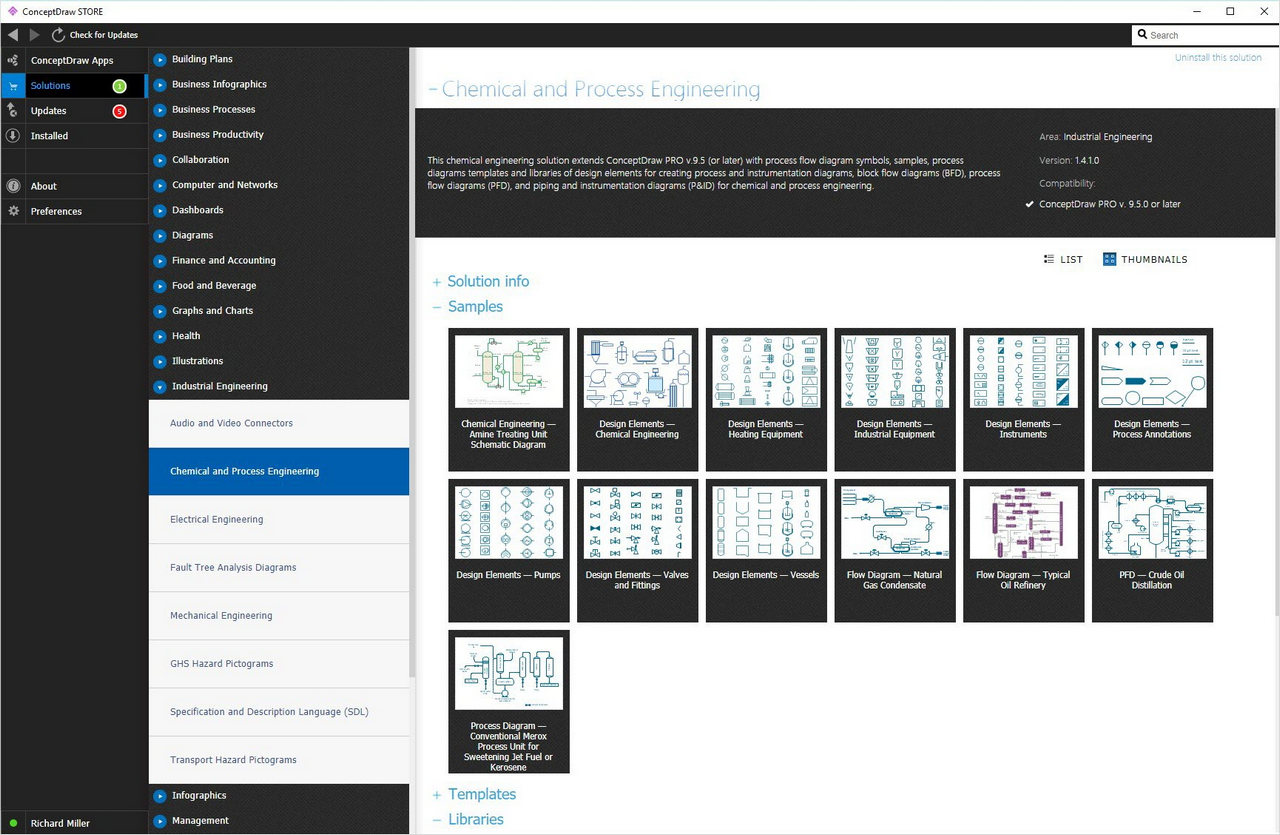
Example 2. Network Security Diagrams Solution in ConceptDraw STORE
One more useful way for inspiration and excellent start for drawing Network Security Diagrams and Network Security Model is collection of predesigned network security samples and examples offered by Network Security Diagrams Solution in ConceptDraw STORE.
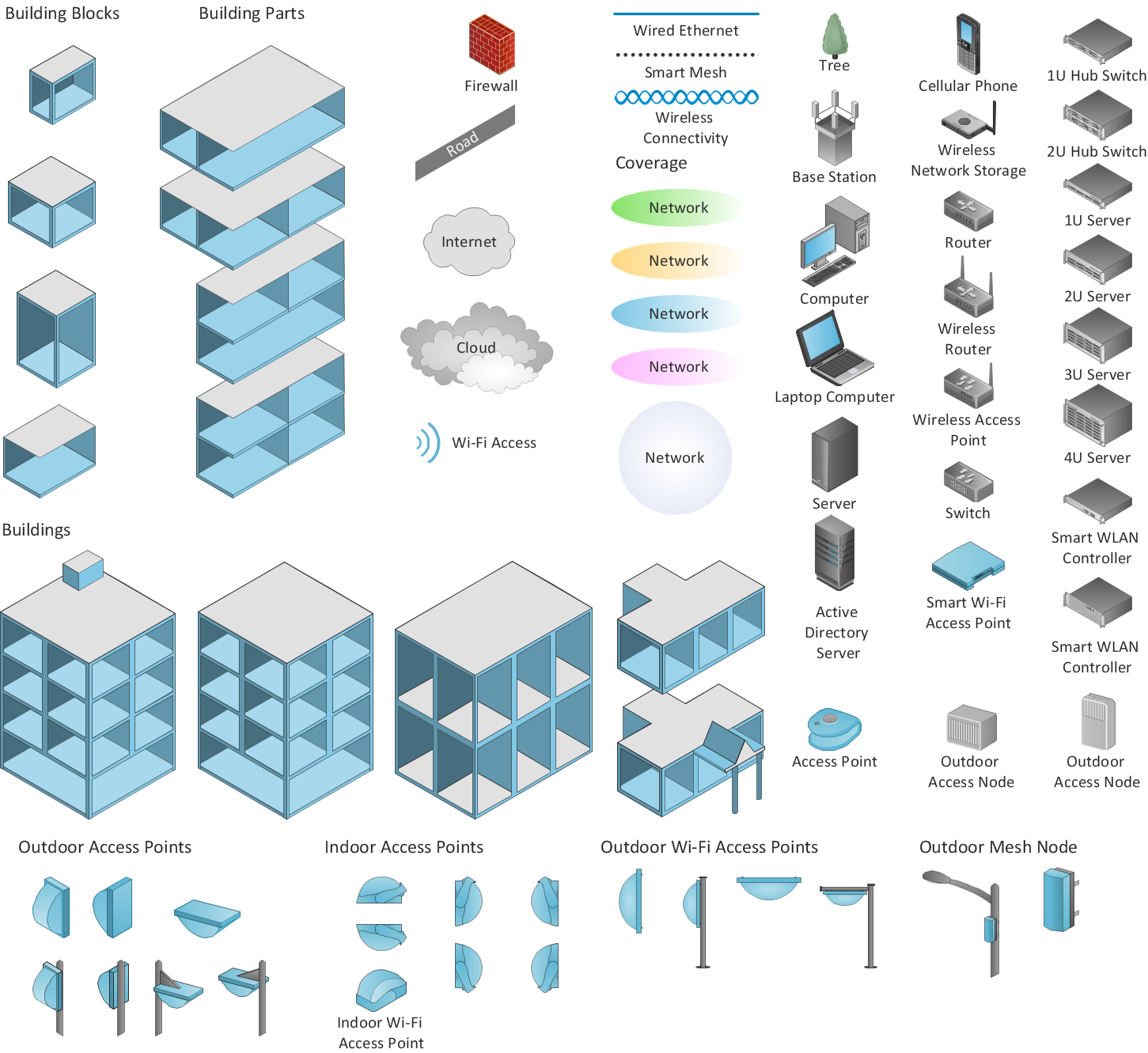
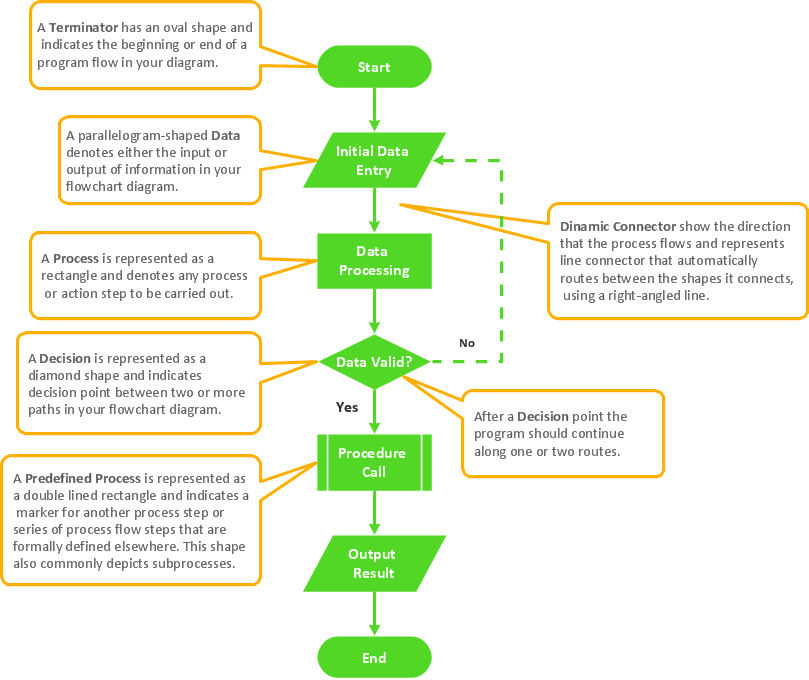
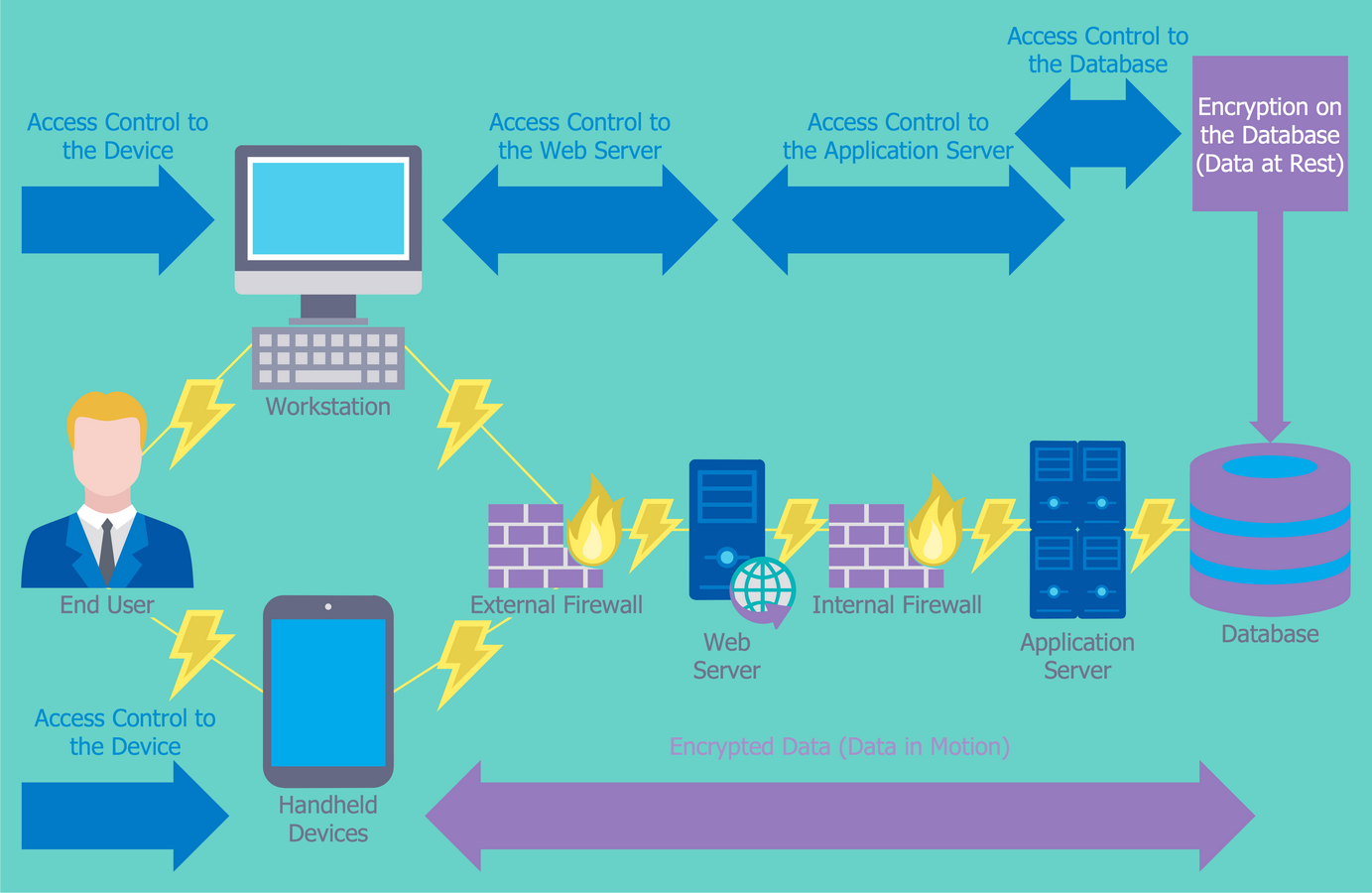
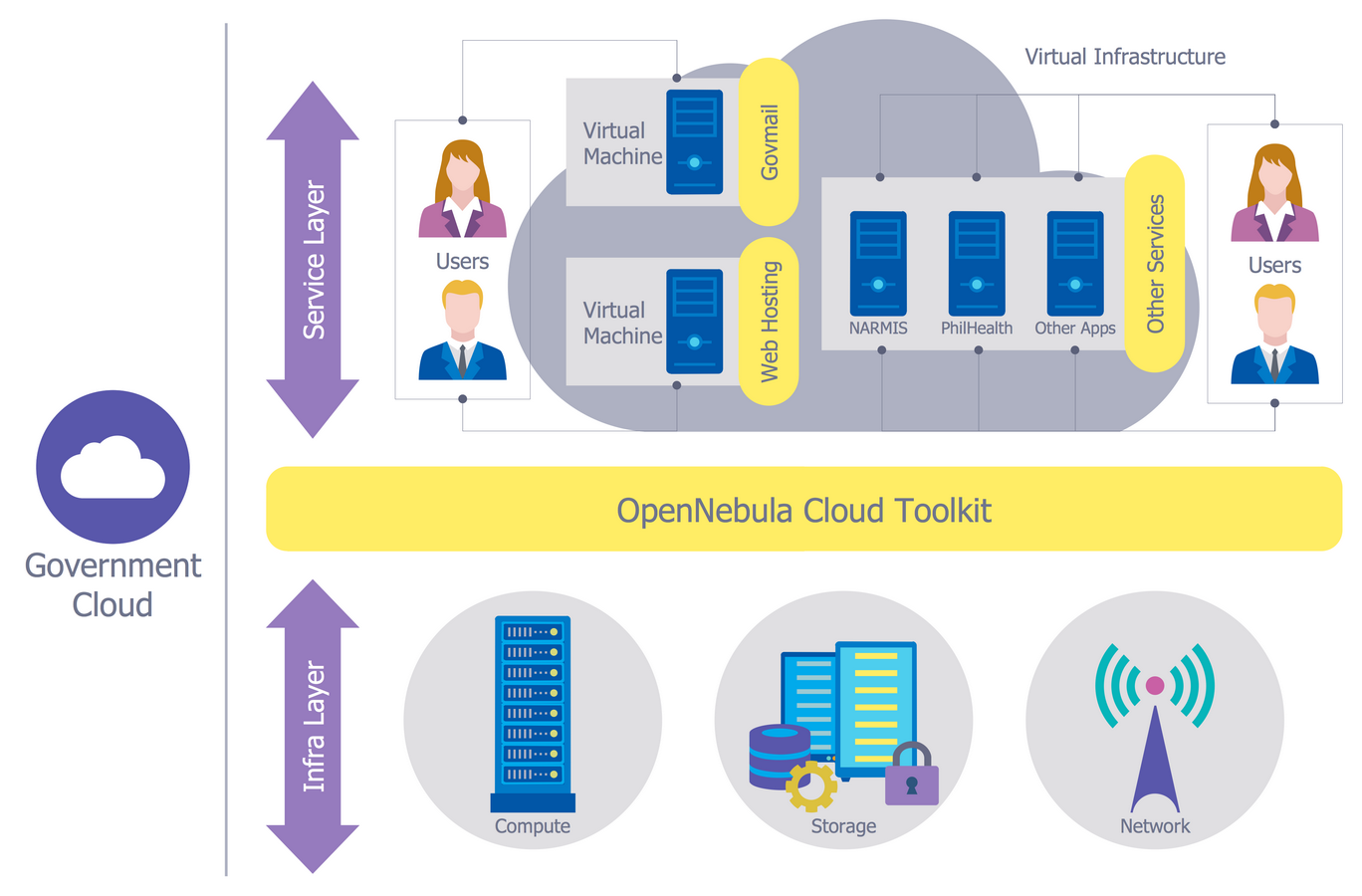
Example 3. Network Security Diagram — Access Control and Encryption
The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software. An experienced user spent 10 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Model and Network Security Diagrams quick, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.