Network Security Devices
How to describe the necessity of using network security devices and visually illustrate this information? Now, it's very easy thanks to the ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.Network Security
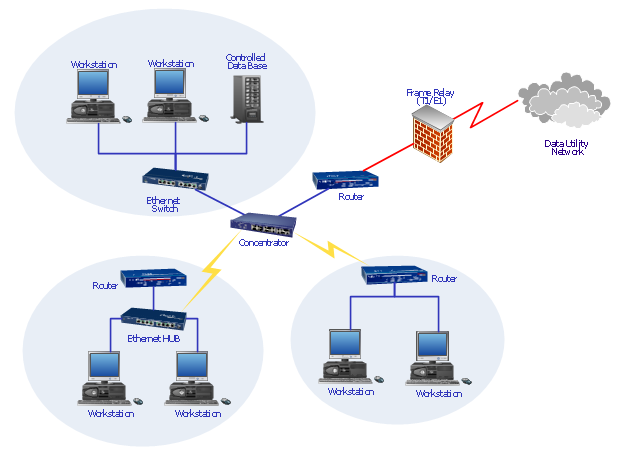
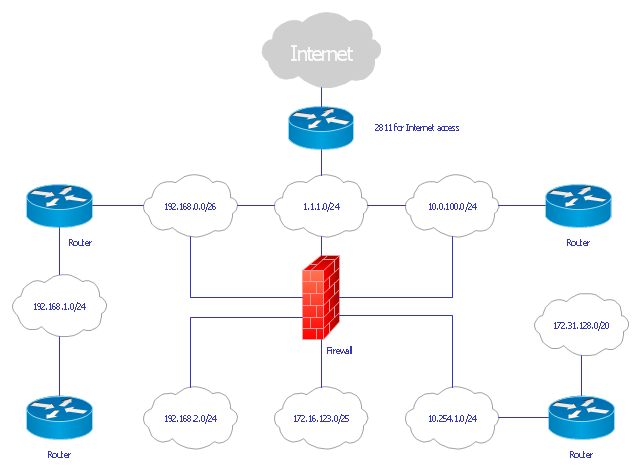
The Internet is a giant computer network which connects computers all over the world. It is integral part of human society and business. But the serious question for network engineers, designers, lawmakers and enforcers is the need for protect the Internet networks from the Internet crimes, hacking and attacks. There are quite a number of hardware, software and physical methods of protection against them. The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software. They show protection networks with Firewalls and other network security devices.Hotel Network Topology Diagram
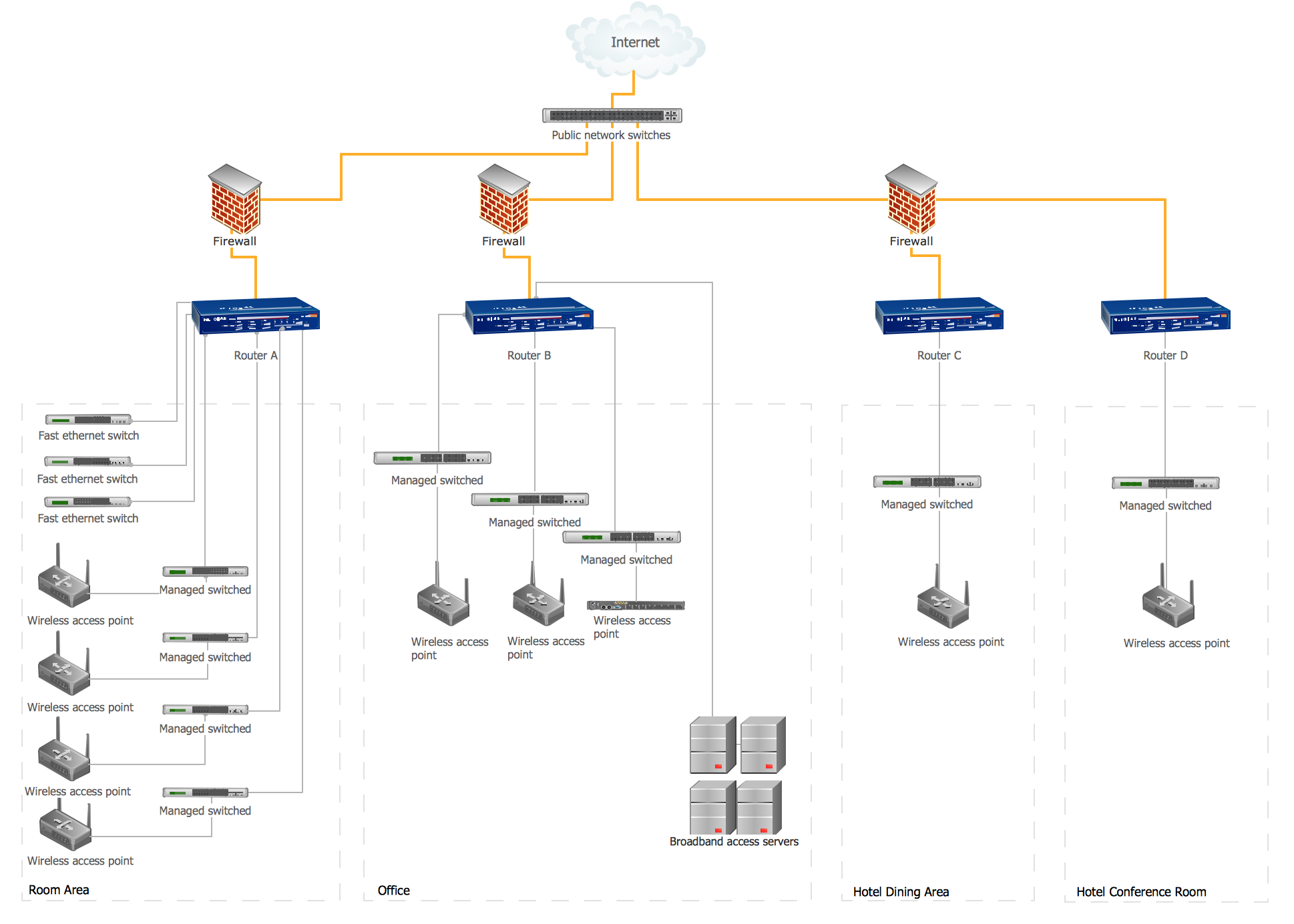
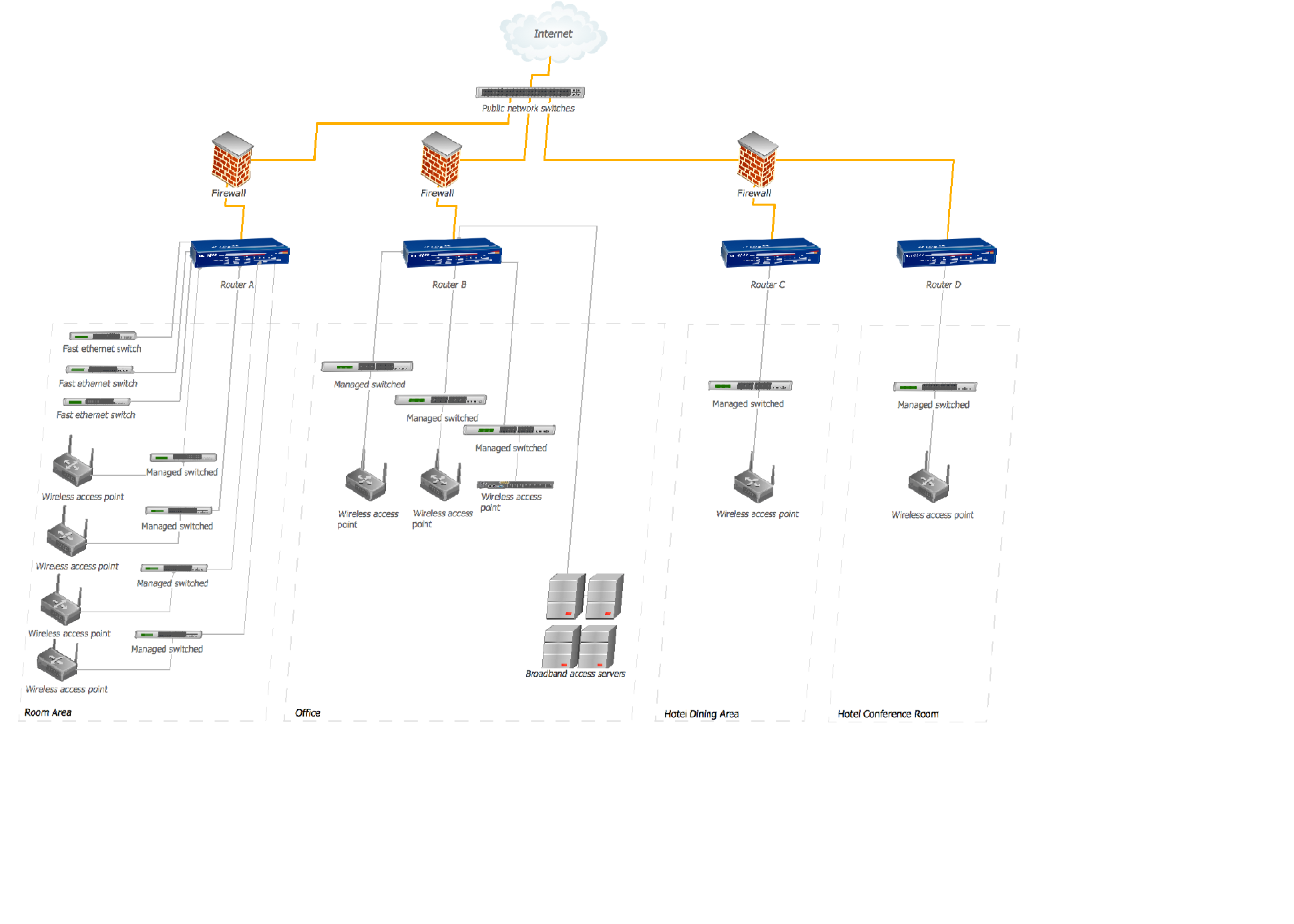
Network topology is a layout of various elements of computer network, such as nodes, links, routers, etc. It is a network topological structure which can be depicted logically or physically. Physical topology shows the physical location of network's components and cable connections between network nodes. Logical topology describes the data flows, the circulation of signals in physical topology. The physical and logical topologies for two networks can be identical, while their physical interconnections, the distances between nodes, transmission rates, and/or signal types may be differ. ConceptDraw DIAGRAM with Computer and Networks solution from Computer and Networks area of ConceptDraw Solution Park lets you design physical and logical network topology diagrams for wireless and wired computer communication networks located in various premises, including the hotels. You can easy design Hotel Network Topology Diagram, diagrams depicted LANs and WLANs, and also any of eight basic topologies (Point-to-point, Star, Bus, Mesh, Ring, Tree, Hybrid, Daisy chain).
Network Gateway Router
Special libraries of highly detailed, accurate shapes and computer graphics, servers, hubs, switches, printers, mainframes, face plates, routers etc.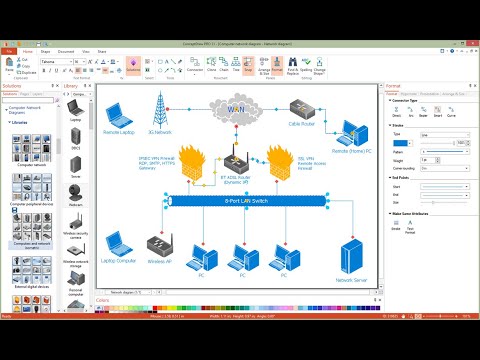
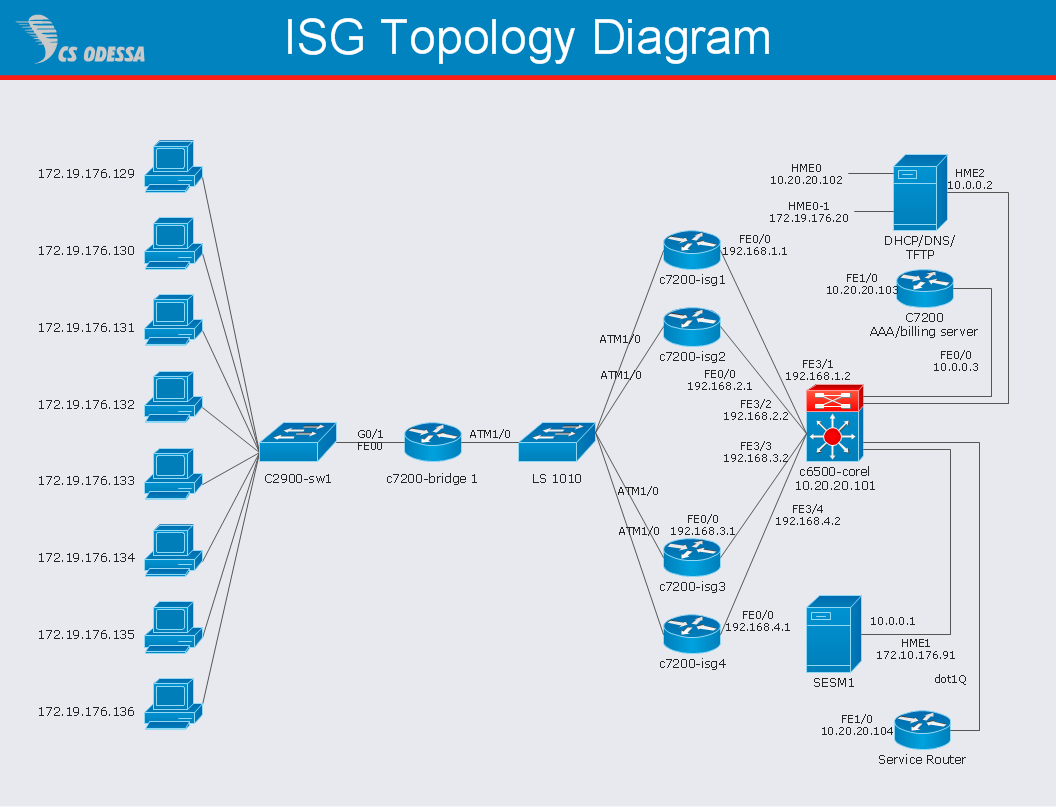
Network Diagram Software ISG Network Diagram
Drawing ISG Network Diagram using ConceptDraw DIAGRAM stencils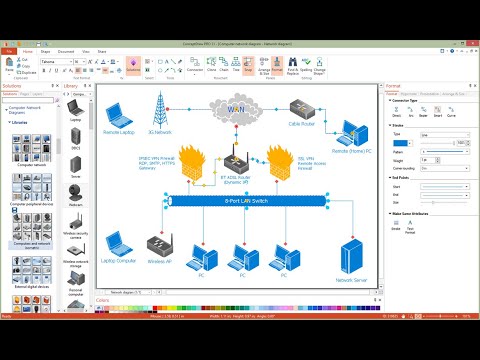
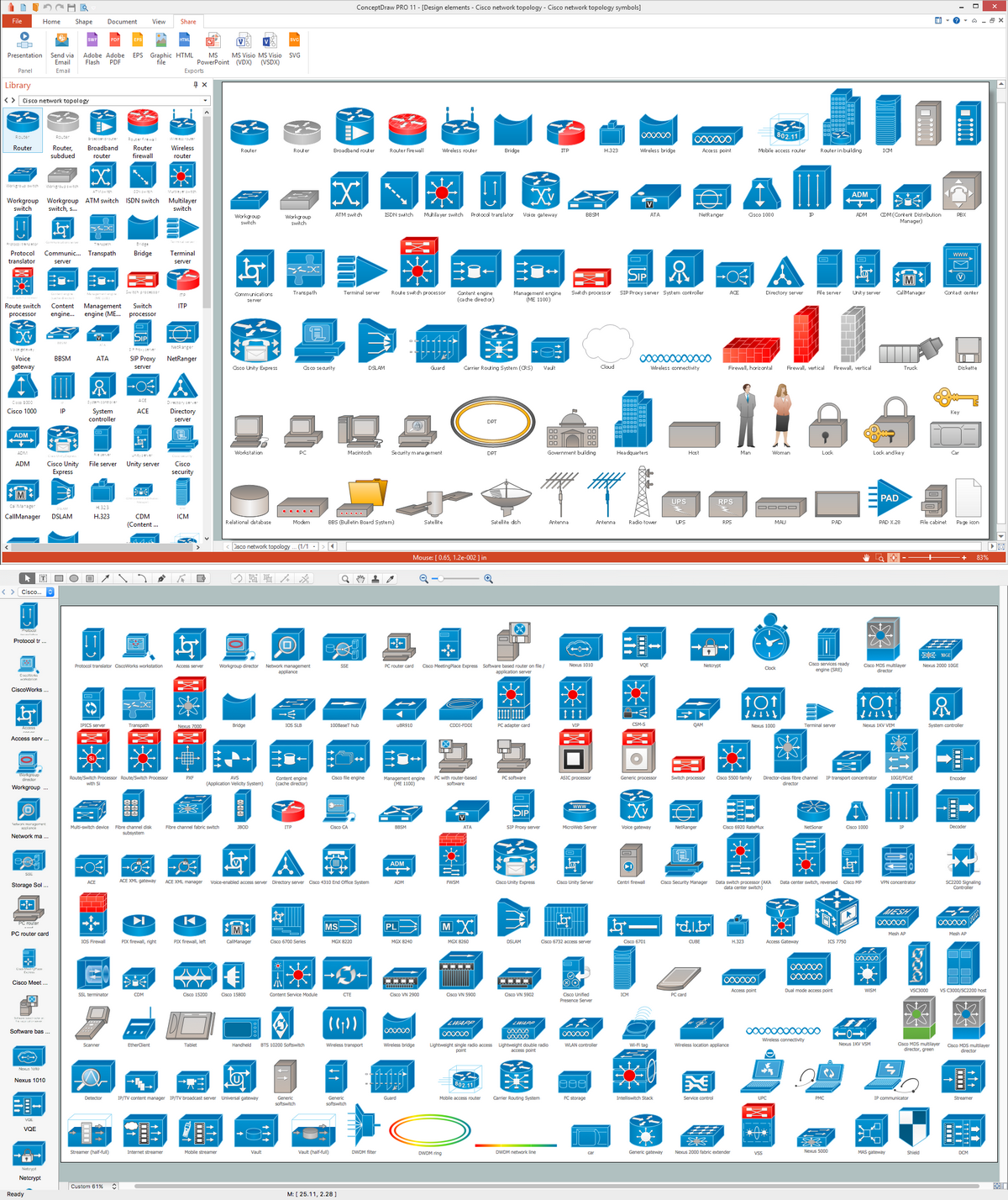
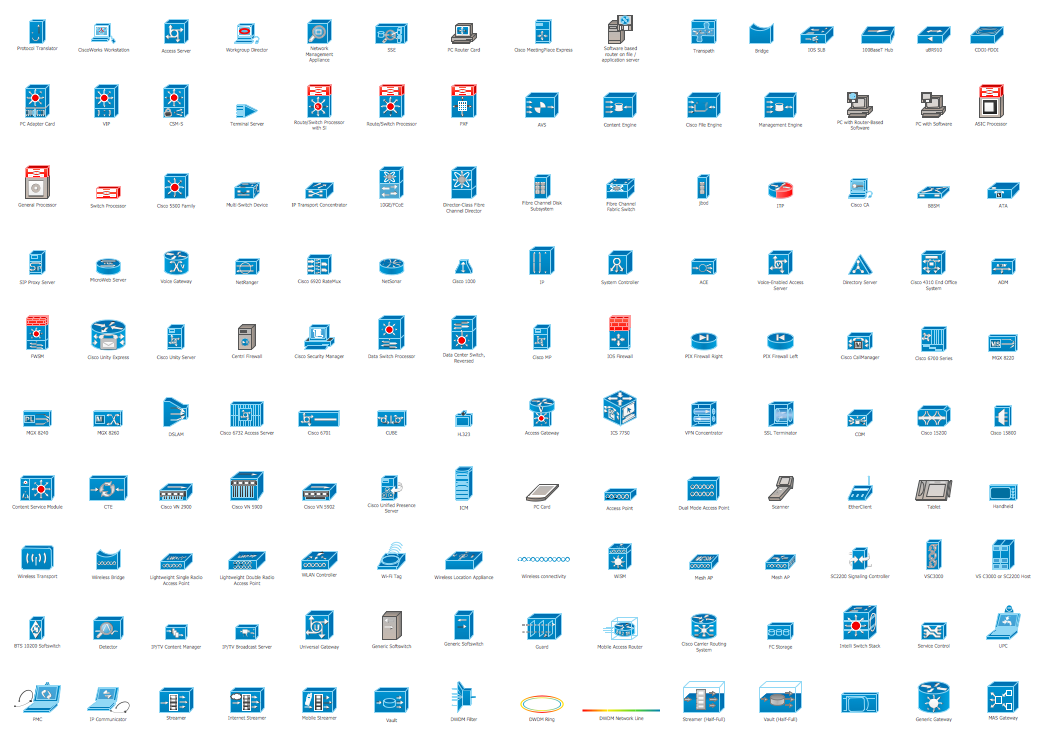
Cisco Network Topology. Cisco icons, shapes, stencils and symbols
Cisco Network Topology represents the arrangement of worldwide recognized and standardized Cisco network symbols, icons, shapes, and stencils which help visualize the schemes of computer networks. Any equipment used in Cisco networks is also named a node and network topology diagram represents the scheme of connection the used nodes. Cisco Network Diagram illustrates how the signals enter on the networked devices and how the data spread within a network from one device to another. These diagrams are useful for engineers while constructing computer networks and working with them. Cisco Network Diagrams solution included to Computer and Networks area of ConceptDraw Solution Park contains quick-start templates, professionally designed samples and examples, and numerous libraries with a lot of predesigned vector design elements, icons, and shapes of Cisco equipment, components, devices, links which provide for ConceptDraw DIAGRAM users a perfect possibility of simple and quick drawing Cisco Network Diagrams and Schematics, Network Designs and Maps of any complexity.Network Security Architecture Diagram
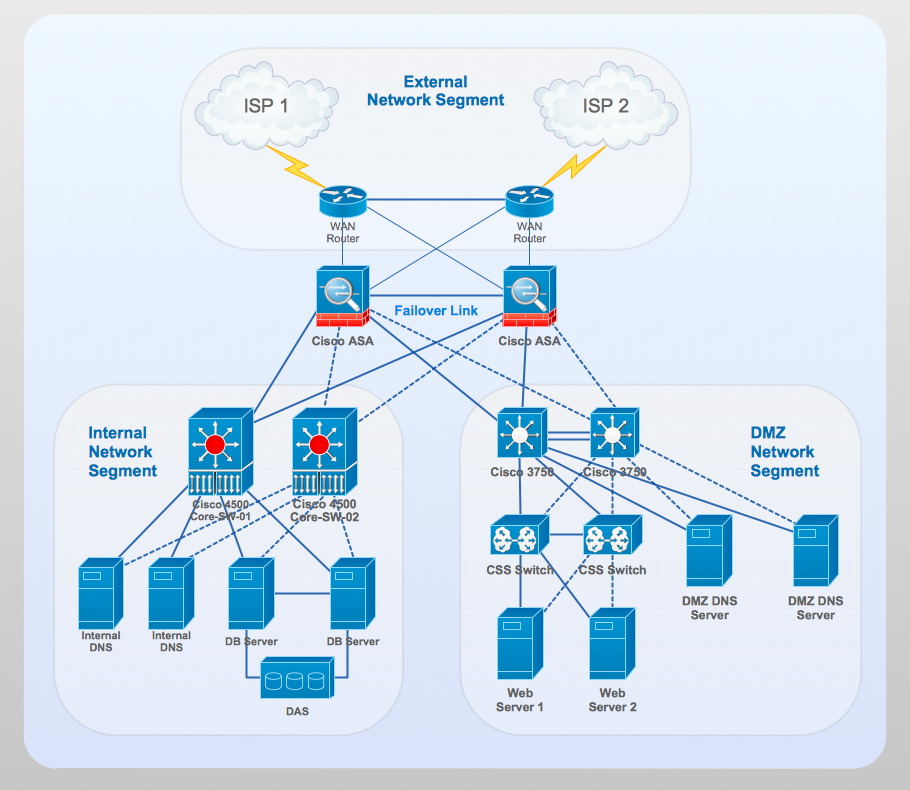
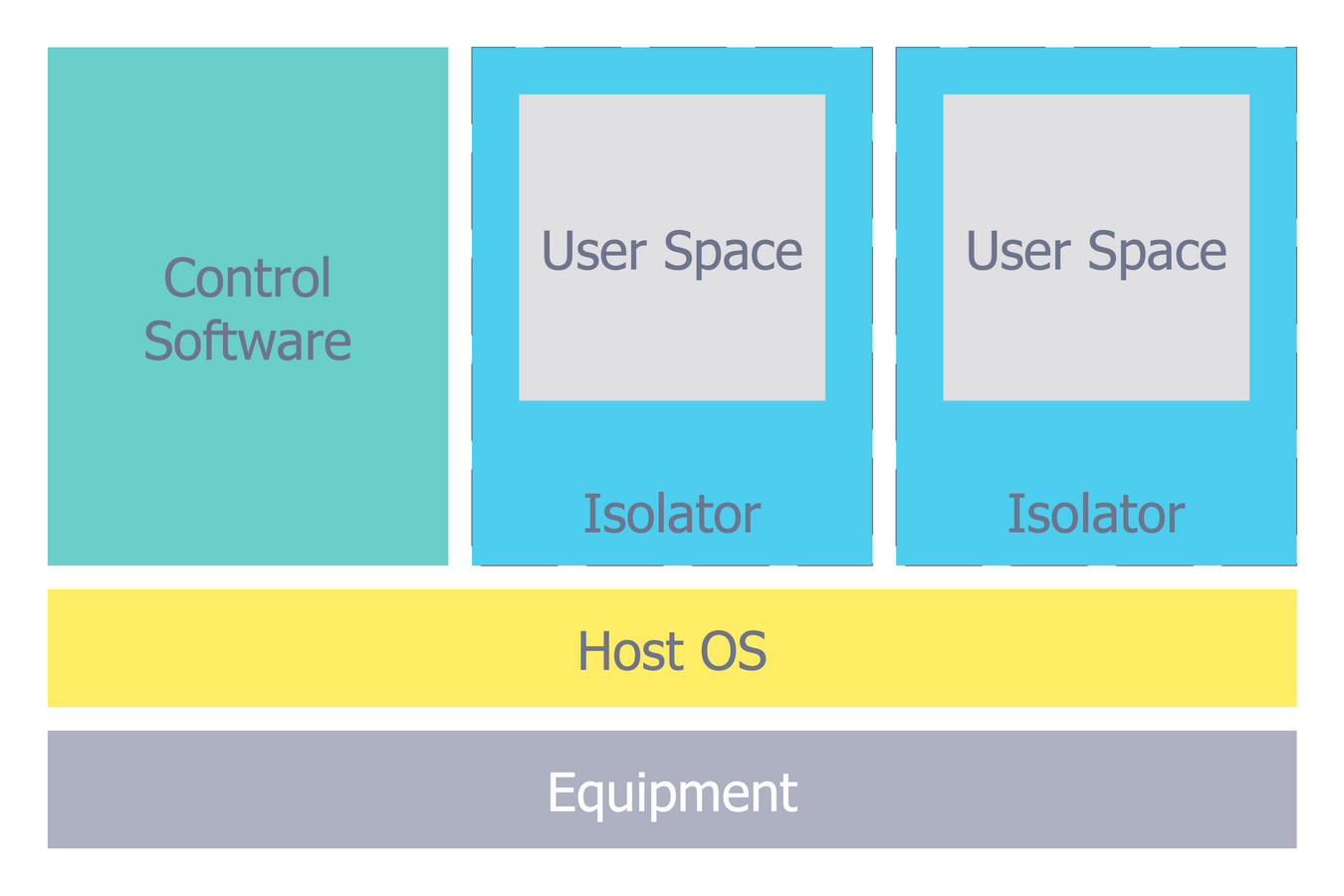
Network Security Architecture Diagram visually reflects the network's structure and construction, and all actions undertaken for ensuring the network security which can be executed with help of software resources and hardware devices. You dream to find powerful software for easy designing Network Security Architecture Diagram? We recommend to use ConceptDraw DIAGRAM extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.This computer security diagram example was designed on the base of the Wikimedia Commons file: Firewall.png.
[commons.wikimedia.org/ wiki/ File:Firewall.png]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"In computing, a firewall is a network security system that monitors and controls the incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted, secure internal network and another outside network, such as the Internet, that is assumed to not be secure or trusted. Firewalls are often categorized as either network firewalls or host-based firewalls. Network firewalls are a software appliance running on general purpose hardware or hardware-based firewall computer appliances that filter traffic between two or more networks. Host-based firewalls provide a layer of software on one host that controls network traffic in and out of that single machine. Firewall appliances may also offer other functionality to the internal network they protect such as acting as a DHCP or VPN server for that network." [Firewall (computing). Wikipedia]
The cybersecurity diagram example "Firewall between LAN and WAN" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
[commons.wikimedia.org/ wiki/ File:Firewall.png]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"In computing, a firewall is a network security system that monitors and controls the incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted, secure internal network and another outside network, such as the Internet, that is assumed to not be secure or trusted. Firewalls are often categorized as either network firewalls or host-based firewalls. Network firewalls are a software appliance running on general purpose hardware or hardware-based firewall computer appliances that filter traffic between two or more networks. Host-based firewalls provide a layer of software on one host that controls network traffic in and out of that single machine. Firewall appliances may also offer other functionality to the internal network they protect such as acting as a DHCP or VPN server for that network." [Firewall (computing). Wikipedia]
The cybersecurity diagram example "Firewall between LAN and WAN" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
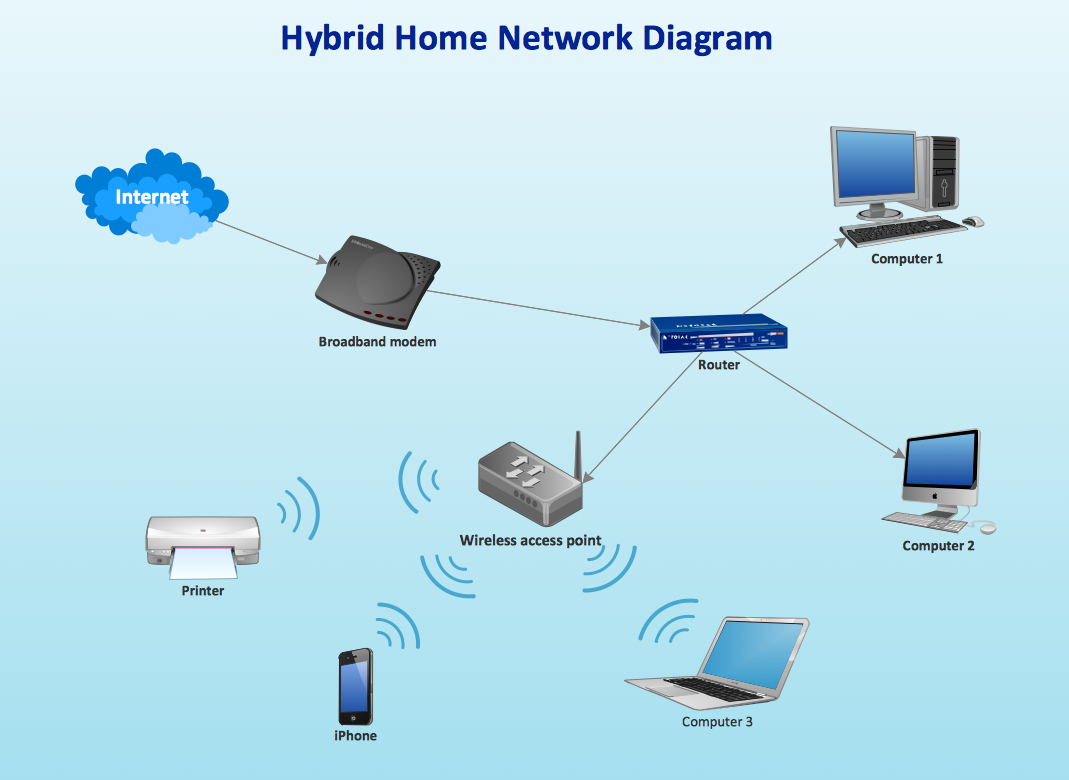
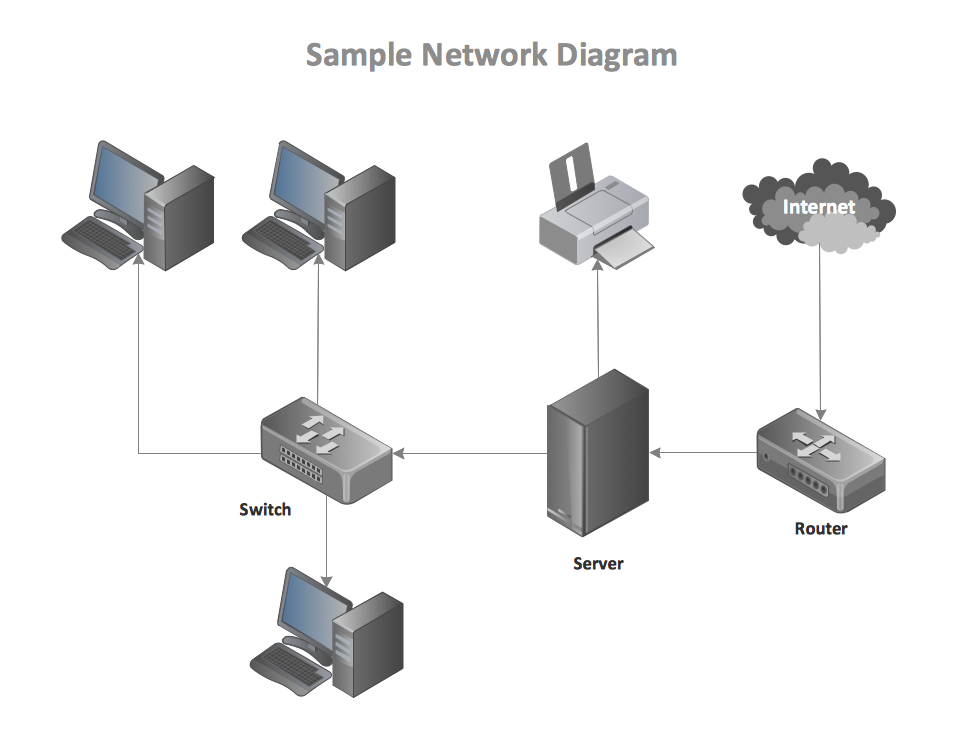
"A computer network or data network is a telecommunications network that allows computers to exchange data. In computer networks, networked computing devices (network nodes) pass data to each other along data connections. The connections (network links) between nodes are established using either cable media or wireless media. The best-known computer network is the Internet.
Network devices that originate, route and terminate the data are called network nodes. Nodes can include hosts such as servers and personal computers, as well as networking hardware. Two devices are said to be networked when a device is able to exchange information with another device." [Computer network. Wikipedia]
This computer communication network diagram example was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Computer and Networks solution from the Computer and Networks area of ConceptDraw Solution Park.
Network devices that originate, route and terminate the data are called network nodes. Nodes can include hosts such as servers and personal computers, as well as networking hardware. Two devices are said to be networked when a device is able to exchange information with another device." [Computer network. Wikipedia]
This computer communication network diagram example was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Computer and Networks solution from the Computer and Networks area of ConceptDraw Solution Park.
Hotel Network Topology Diagram. Hotel Guesthouse WiFi Network
Would you like to design and construct the local area network (LAN) or wireless LAN (WLAN) at your hotel, guesthouse or inn? In this case first that you need to do is to develop the detailed plan and to represent on it all required equipment, as well as scheme of its arrangement and connection. The ConceptDraw Solution Park offers a powerful Computer Network Diagrams solution from the Computer and Networks area specially developed to help you draw fast and easily the physical and logical network topology diagrams for wireless and wired computer communication networks. The Computer Network Diagrams solution provides numerous set of predesigned samples and templates, and large variety of vector stencils libraries with ready-to-use network icons and symbols of LAN and WLAN equipment, containing the routers, firewalls, switches, wireless access points, broadband access servers, and many other vector symbols. Use them as a real help when designing the Hotel Network Topology Diagrams, Hotel Wireless Computer Network Plans, Guesthouse Wi-Fi Network Diagrams.How to Create Network Diagrams
ConceptDraw Wireless Network solution includes 81 of professional-looking stencils and several samples that you can modify and make your own diagram."... logical topology shows how data flows within a network, regardless of its physical design. ...
... mapping the data flow between the components determines the logical topology of the network." [Network topology. Wikipedia]
"In a shared media topology, all the systems have the ability to access the physical layout whenever they need it. The main advantage in a shared media topology is that the systems have unrestricted access to the physical media. Of course, the main disadvantage to this topology is collisions. If two systems send information out on the wire at the same time, the packets collide and kill both packets. Ethernet is an example of a shared media topology. ...
The token-based topology works by using a token to provide access to the physical media. In a token-based network, there is a token that travels around the network. When a system needs to send out packets, it grabs the token off of the wire, attaches it to the packets that are sent, and sends it back out on the wire. As the token travels around the network, each system examines the token. When the packets arrive at the destination systems, those systems copy the information off of the wire and the token continues its journey until it gets back to the sender. When the sender receives the token back, it pulls the token off of the wire and sends out a new empty token to be used by the next machine." [Logical topology. Wikipedia]
This Cisco logical computer network diagram example was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Cisco Network Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
... mapping the data flow between the components determines the logical topology of the network." [Network topology. Wikipedia]
"In a shared media topology, all the systems have the ability to access the physical layout whenever they need it. The main advantage in a shared media topology is that the systems have unrestricted access to the physical media. Of course, the main disadvantage to this topology is collisions. If two systems send information out on the wire at the same time, the packets collide and kill both packets. Ethernet is an example of a shared media topology. ...
The token-based topology works by using a token to provide access to the physical media. In a token-based network, there is a token that travels around the network. When a system needs to send out packets, it grabs the token off of the wire, attaches it to the packets that are sent, and sends it back out on the wire. As the token travels around the network, each system examines the token. When the packets arrive at the destination systems, those systems copy the information off of the wire and the token continues its journey until it gets back to the sender. When the sender receives the token back, it pulls the token off of the wire and sends out a new empty token to be used by the next machine." [Logical topology. Wikipedia]
This Cisco logical computer network diagram example was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Cisco Network Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
Basic Network Diagram
The Basic Network Diagram is an easy and effective way to design and document a simple network, it lets to represent visually and logically how the different network devices and computer equipment can be installed to meet the main business needs. ConceptDraw DIAGRAM software supplied with Computer Network Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park is a perfect tool for drawing the Basic Computer Network diagrams, designs, schematics, and maps, network architectures, topologies, and layouts. Numerous vector libraries of network symbols, icons and components are incredibly helpful for IT and telecom engineers, stakeholders and end-users when designing Basic Network Diagrams, Common Network Diagrams, Common Network Topologies, 10Base-T Star Network Topologies, Bus Topology Diagrams, Communication Network Diagrams, System Designs, Regional Cable Head-End Diagrams, etc. Collection of predesigned samples and templates included to Computer Network Diagrams solution also greatly extends the capabilities of ConceptDraw DIAGRAM users.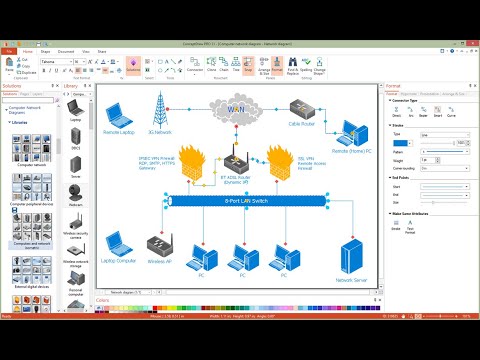
 Network Security Diagrams
Network Security Diagrams
The Network Security Diagrams solution presents a large collection of predesigned cybersecurity vector stencils, cliparts, shapes, icons and connectors to help you succeed in designing professional and accurate Network Security Diagrams, Network Security Infographics to share knowledge about effective ways of networks protection with help of software and network security devices of different cyber security degrees, Network Plans for secure wireless network, Computer Security Diagrams to visually tell about amazing possibilities of IT security solutions. The samples and examples reflect the power of ConceptDraw DIAGRAM software in drawing Network Security Diagrams, give the representation about variety of existing types of attacks and threats, help to realize their seriousness and the methods to deal with them.
Cisco Products Additional. Cisco icons, shapes, stencils and symbols
The ConceptDraw vector stencils library Cisco Products Additional contains equipment symbols for drawing the computer network diagrams.- Basic Network Diagram With Firewall
- Firewall between LAN and WAN | Network Security Diagrams ...
- Network Diagram Software ISG Network Diagram | Network Security ...
- Firewall between LAN and WAN | Network Security | Basic Network ...
- Firewall between LAN and WAN | Network Diagram Examples ...
- Firewall On Network Diagram
- Firewall between LAN and WAN | Cubetto Flowchart | Cisco Network ...
- Firewall between LAN and WAN | Network Security Diagrams | Hotel ...
- Firewall between LAN and WAN | Network Security | Network ...
- Network Security Devices | Firewall between LAN and WAN ...
- Firewall Network Diagram In Lan
- Star Network Topology | Hotel Network Topology Diagram | Fully ...
- Internet symbols - Vector stencils library | Network Security Devices ...
- Firewall between LAN and WAN | How to Draw a Computer Network ...
- Communication network diagram | Network Glossary Definition ...
- Use Of A Hardware Firewall With A Diagram
- Network Diagram Cloud Firewall Workstation Switch Server
- Create Ethernet Basic Network Diagram Using Firewall
- Diagrams Of Hardware Firewall In Network
- Firewall Diagram In Network Security