Cyber Security Degrees
For protection various cyber environments are developed and applied large variety of cyber security standards, techniques, security concepts and approaches with different cyber security degrees. The ConceptDraw PRO diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park offers the number of useful tools which will help network security engineers, cyber security specialists, network and computer analysts easily and visually depict the knowledge and skills for research and prevention of intrusions, about protection critical information and analysis of cyber incidents, and for how to assess threats and vulnerabilities.This example was designed on the base of the cybersecurity infographic from the website gov.uk. (Open Government Licence v3.0. nationalarchives.gov.uk/ doc/ open-government-licence/ version/ 3/ )
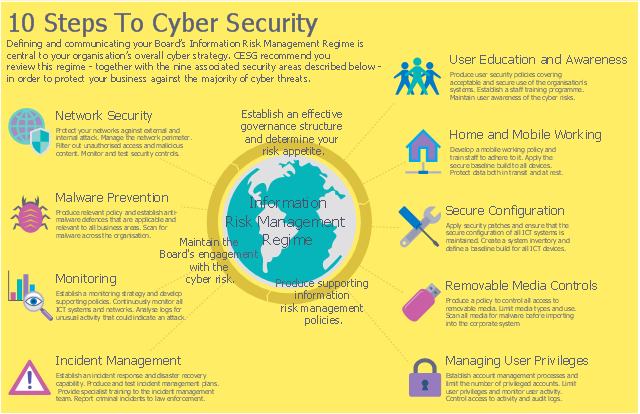
"10 Steps To Cyber Security...
Defining and communicating your Board’s Information Risk Management Regime (shown at the centre of the following diagram) is central to your organisation’s overall cyber strategy.
... the 9 steps that surround it are ...
- Secure configuration
- Network security
- Managing user privileges
- User education and awareness
- Incident management
- Malware prevention
- Monitoring
- Removable media controls
- Home and mobile working" [gov.uk/ government/ publications/ cyber-risk-management-a-board-level-responsibility/ 10-steps-summary]
The infographic example "10 Steps to Cyber Security" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
"10 Steps To Cyber Security...
Defining and communicating your Board’s Information Risk Management Regime (shown at the centre of the following diagram) is central to your organisation’s overall cyber strategy.
... the 9 steps that surround it are ...
- Secure configuration
- Network security
- Managing user privileges
- User education and awareness
- Incident management
- Malware prevention
- Monitoring
- Removable media controls
- Home and mobile working" [gov.uk/ government/ publications/ cyber-risk-management-a-board-level-responsibility/ 10-steps-summary]
The infographic example "10 Steps to Cyber Security" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
Used Solutions
 Network Security Diagrams
Network Security Diagrams
The Network Security Diagrams solution enhances the ConceptDraw PRO v10 functionality with large collection of predesigned vector stencils of cybersecurity clipart, shapes, icons and connectors to help you succeed in designing professional and accurate Ne
IT Security Solutions
Dynamic of development computer and network technologies increases the need in modern cyber security strategies and IT security solutions to support security of your data, to ensure data privacy, and to protect your operations from the cyber threats. Thanks to the Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park, the ConceptDraw PRO diagramming and vector drawing software is one of the unique IT security solutions for professional designing Network Security Diagrams.Network Security Tips
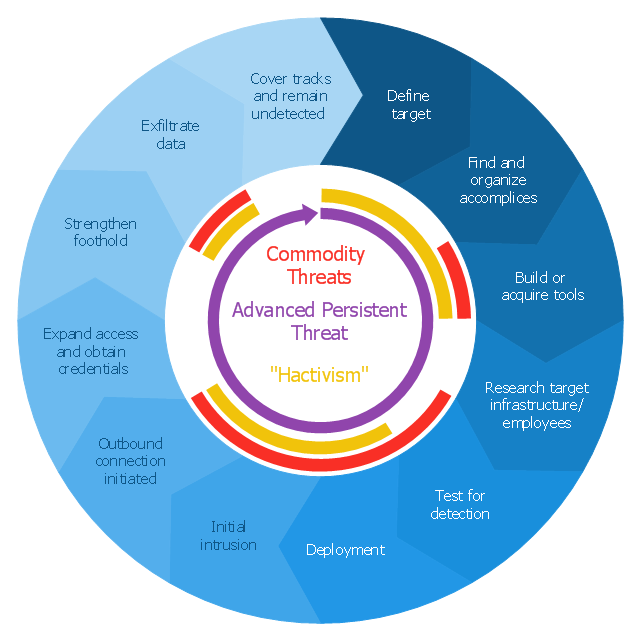
The Internet is a huge world with unlimited possibilities. But with all its numerous advantages, the Internet also conceals many dangers and security threats, that's why we advise you to follow simple network security tips. ConceptDraw PRO diagramming and vector drawing software supplied with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is an ideal software for easy designing Network Security Diagrams and attractive illustrations with effective network security tips."Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
This circular arrows diagram example was redesigned from the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
The example "Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
This circular arrows diagram example was redesigned from the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
The example "Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
Network Security Diagram
ConceptDraw PRO diagramming and vector drawing software enhanced with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is the best for effective design professional, colorful and attractive Network Security Diagram of any complexity and degree of detailing.HelpDesk
How to Convert a Mind Map into MS Word Document
Mind maps are often used for structuring ideas, planning and organizing of various documents. ConceptDraw MINDMAP allows you transfer a mind map to MS Word format using its export facilities. You can convert a mind map to a MS Word outline using the set of standard templates, or even your custom template. Thus, your mind map will be transformed into the proper document format. Using a custom MS Word template allows you apply your individual style to each document, being exported from ConceptDraw MINDMAP. You can use a mind mapping to capture ideas and structure information. Then making a quick conversion to MS Word and you finally obtain a clean and stylish document.
 ConceptDraw Solution Park
ConceptDraw Solution Park
ConceptDraw Solution Park collects graphic extensions, examples and learning materials
 Computer and Networks Area
Computer and Networks Area
The solutions from Computer and Networks Area of ConceptDraw Solution Park collect samples, templates and vector stencils libraries for drawing computer and network diagrams, schemes and technical drawings.
- Cyber Security Degrees | 10 Steps to Cyber Security | Network ...
- 10 Steps to Cyber Security | Network Security Diagrams | Network ...
- Cyber Security Degrees | Network Security Diagrams | Computer ...
- Design elements - Cybersecurity round icons | Cyber Security ...
- Design elements - Cybersecurity shapes | Cyber Security Degrees ...
- Design elements - Cybersecurity clipart | Cyber Security Degrees ...
- How to Create a Network Security Diagram Using ConceptDraw PRO
- Design elements - Cybersecurity connectors | Cyber Security ...
- A Business Plan On Wbs About Cyber Cafe
- 10 Steps to Cyber Security
- How to Create a Network Security Diagram Using ConceptDraw ...
- Erd Dfd Examples For Cyber Cafe
- Network Security Diagrams | IT Security Solutions | Network Security ...
- Typical Plan Of A Cyber Cafe
- Er Diagram Of A Cyber Cafe Database
- Secure Wireless Network | Network Security Diagrams ...
- How To Draw A Floor Plan Of Cyber Cafe
- Show A Stech Of The Layout Of Cyber Cafe
- ConceptDraw PRO Network Diagram Tool | Network Security ...
- Recommended network architecture for BlackBerry SWS | Network ...