Cyber Security Degrees
Cyber security is the defense of information and computer systems from various attacks and threats, from the damage the hardware and software, from the theft of the information stored on them, and from the disruption and misdirection of services which they provide. The reliance on various computer and networked systems increases day by day, but all them are sufficiently vulnerable and so the need for cyber security acquires more and more importance, it includes protection from the damages due to the network access, the control of physical access to the hardware, the control of intentional and accidental malpractice by operators.
Increase of variety and quantity of cyber threats is lead to the active development of cyber security field today. For protection various cyber environments are developed and applied large variety of cyber security standards, techniques, security concepts and approaches with different cyber security degrees. But the main common objective of all them is reduce the risks, increase privacy and security, provide a reliable protection of computers, programs, networks and data from damages and unauthorized access, and effectively prevent the cyber attacks and cyber threats.
The ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park offers the number of useful tools which will help network security engineers, cyber security specialists, network and computer analysts easily and visually depict the knowledge and skills for research and prevention of intrusions, about maintenance of security protocols on computer networks of various sizes, about protection critical information and analysis of cyber incidents, and for how to assess threats and vulnerabilities.

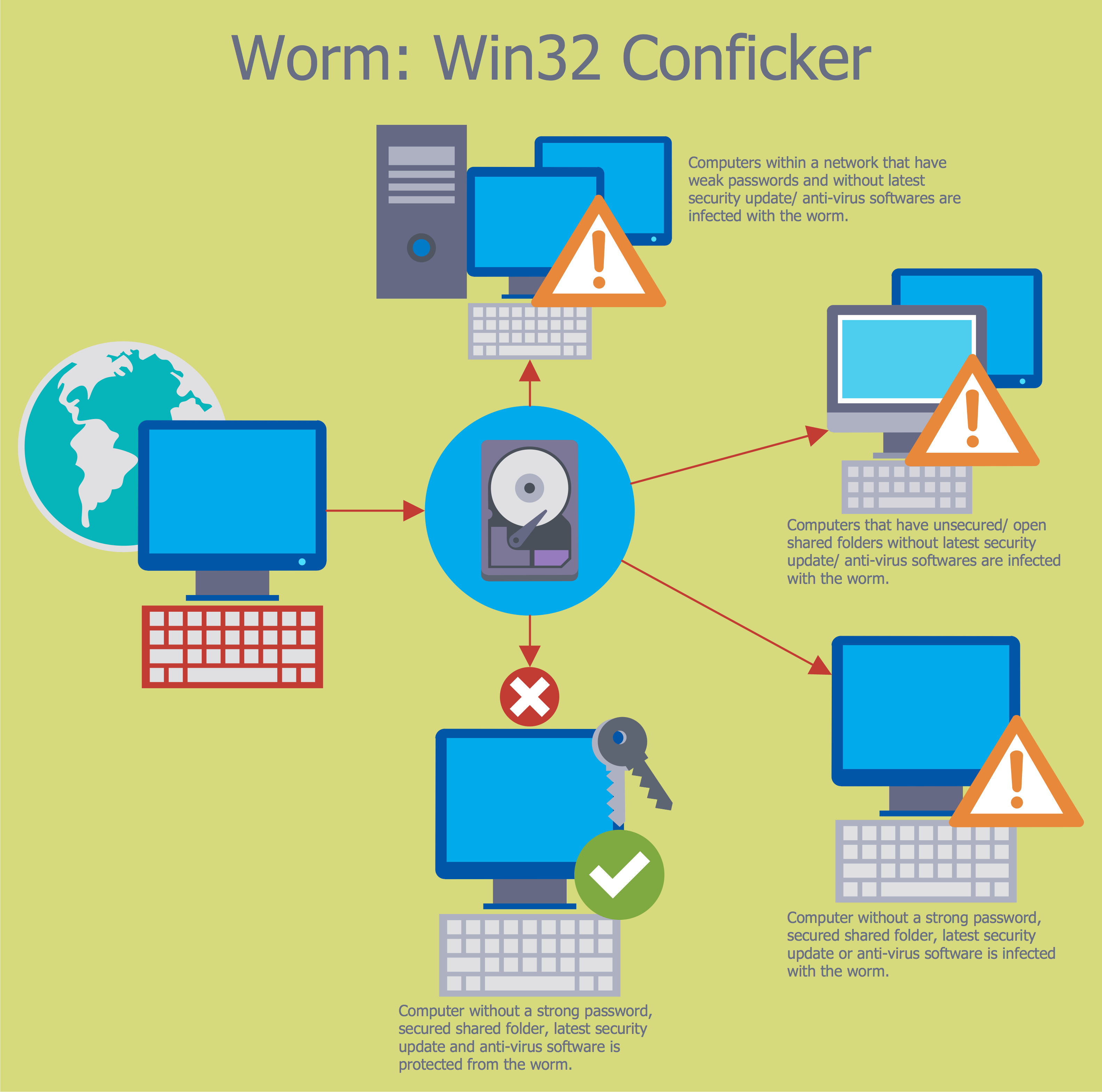
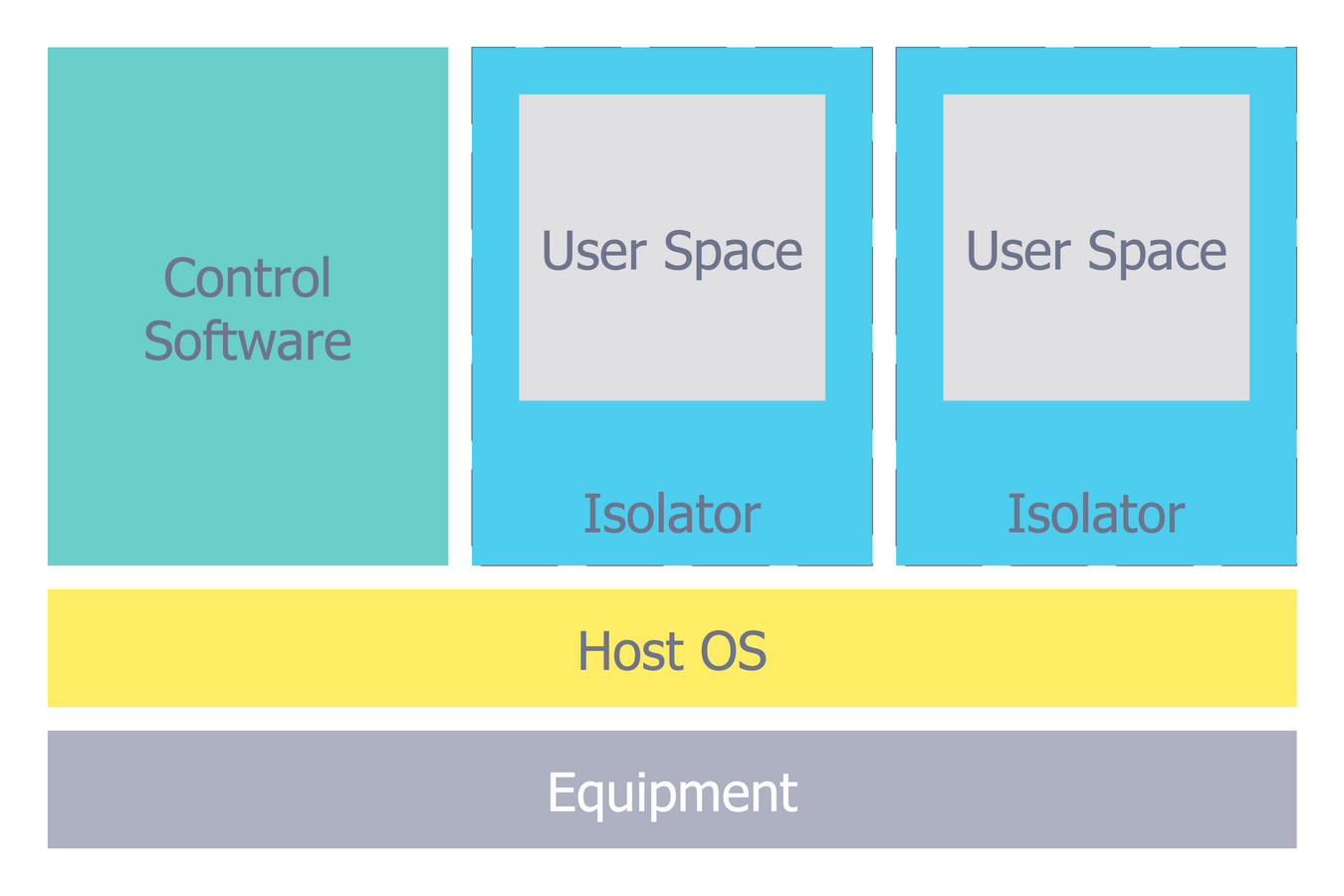
Example 1. Cyber Security Degrees
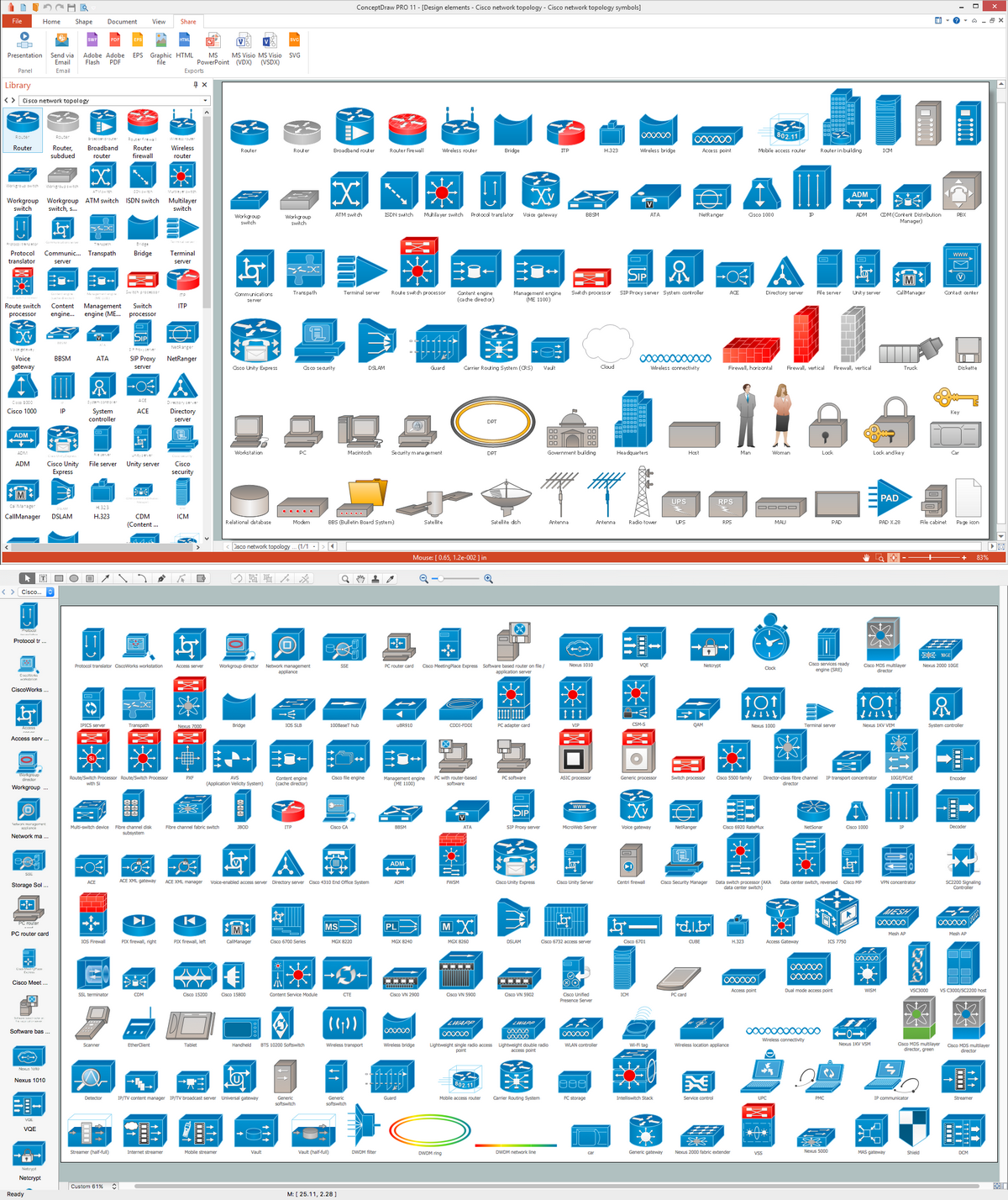
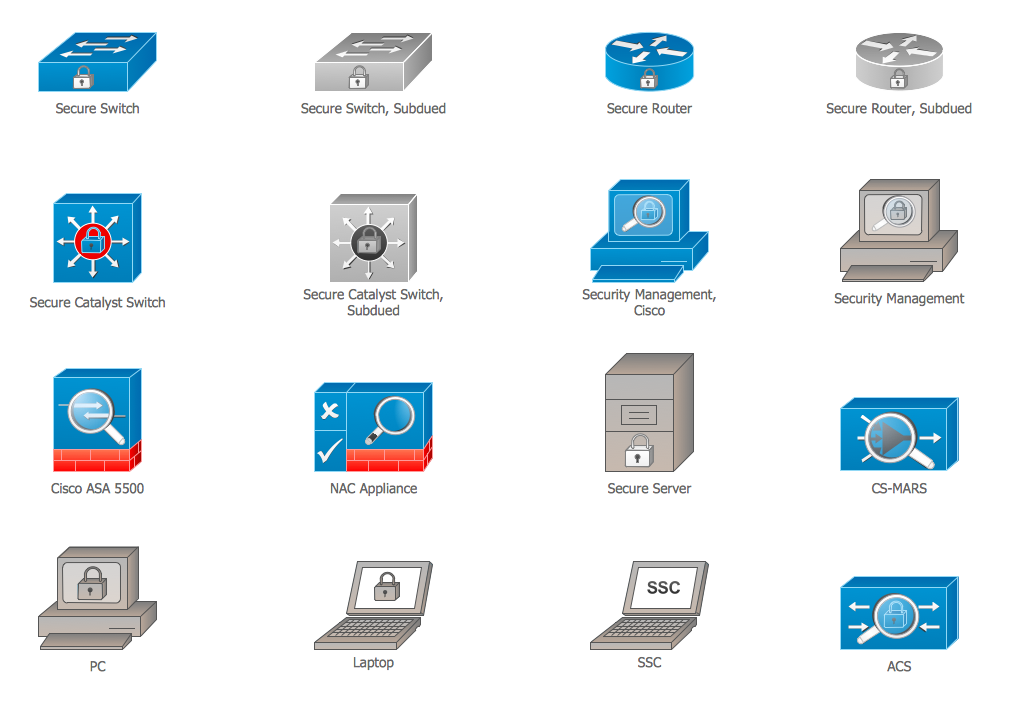
Network Security Diagrams Solution for ConceptDraw DIAGRAM is incredibly useful for effective network security schemes design with different cyber security degrees thanks primarily to 4 libraries with numerous quantity of predesigned vector objects:
- Cybersecurity Clipart
- Cybersecurity Round Icons
- Cybersecurity Shapes
- Cybersecurity Connectors
Start create your diagram by dragging the objects from these libraries to your ConceptDraw document and evaluate the usability of using fully ready-to-use objects.
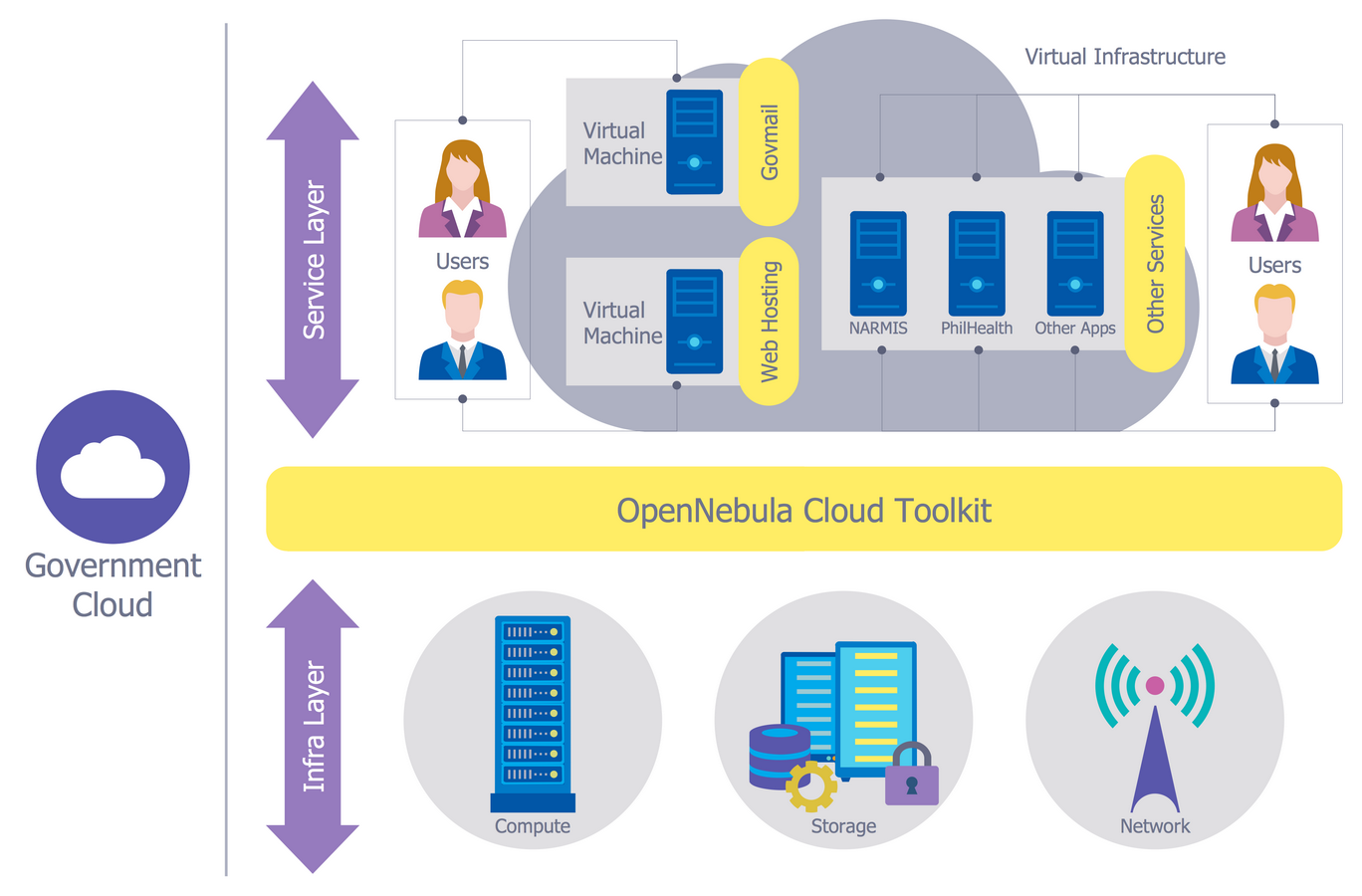
Example 2. Network Security Diagrams Solution in ConceptDraw STORE
Network Security Diagrams solution provides also wide collection of predesigned network security samples which are available from ConceptDraw STORE. Each of offered samples is carefully thought-out by experts and can be used as easy start for your own diagrams. Pay attention for them and get excellent result in a few minutes!
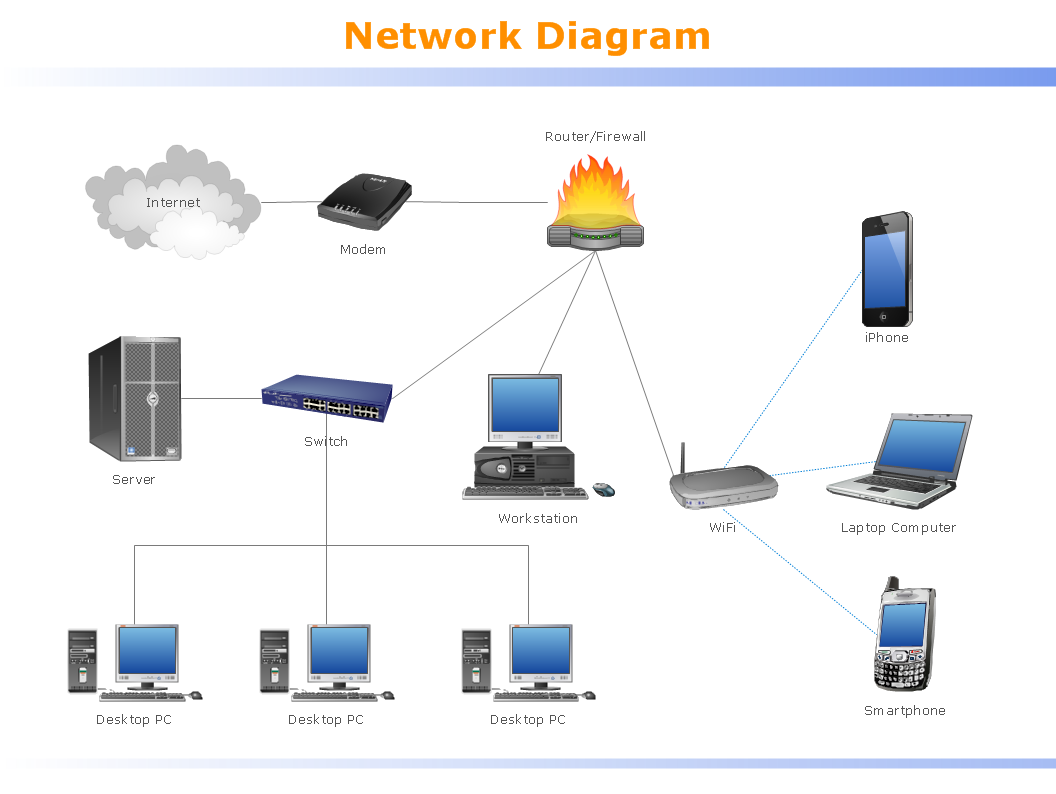
Example 3. Network Security Diagram - Recommended Network Architecture
The samples you see on this page were created in ConceptDraw DIAGRAM using the predesigned vector objects from the libraries of Network Security Diagrams Solution. An experienced user spent 10-15 minutes creating each of these samples.
Use the Network Security Diagrams Solution for ConceptDraw DIAGRAM to create your own Network Security Diagrams of any cyber security degrees fast, easy and effective.
All source documents are vector graphic documents. They are available for reviewing, modifying, or converting to a variety of formats (PDF file, MS PowerPoint, MS Visio, and many other graphic formats) from the ConceptDraw STORE. The Network Security Diagrams Solution is available for all ConceptDraw DIAGRAM users.