Event-driven Process Chain Diagrams
Event-driven Process Chain Diagrams
Event-Driven Process Chain Diagrams solution extends ConceptDraw DIAGRAM functionality with event driven process chain templates, samples of EPC engineering and modeling the business processes, and a vector shape library for drawing the EPC diagrams and EPC flowcharts of any complexity. It is one of EPC IT solutions that assist the marketing experts, business specialists, engineers, educators and researchers in resources planning and improving the business processes using the EPC flowchart or EPC diagram. Use the EPC solutions tools to construct the chain of events and functions, to illustrate the structure of a business process control flow, to describe people and tasks for execution the business processes, to identify the inefficient businesses processes and measures required to make them efficient.
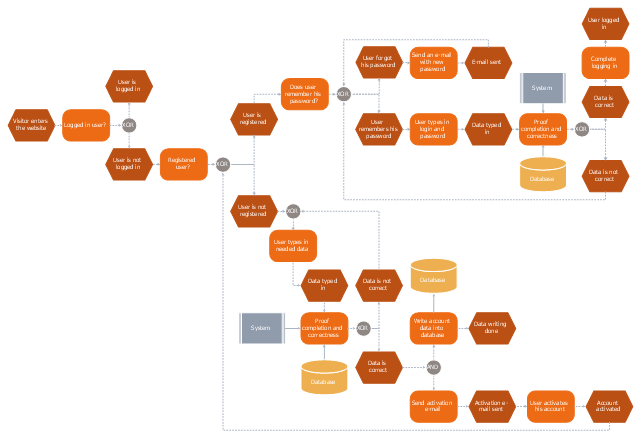
This computer security EPC diagram sample depicts the login and registration processing flow.
"In computer security, a login or logon refers to the credentials required to obtain access to a computer system or other restricted area. Logging in or on and signing in or on is the process by which individual access to a computer system is controlled by identifying and authenticating the user through the credentials presented by the user.
Once a user has logged in, they can then log out or log off when access is no longer needed. To log out is to close off one's access to a computer system after having previously logged in." [Login. Wikipedia]
The event-driven process chain (EPC) flowchart example "Login and registration processing" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Event-driven Process Chain Diagrams solution from the Business Processes area of ConceptDraw Solution Park.
"In computer security, a login or logon refers to the credentials required to obtain access to a computer system or other restricted area. Logging in or on and signing in or on is the process by which individual access to a computer system is controlled by identifying and authenticating the user through the credentials presented by the user.
Once a user has logged in, they can then log out or log off when access is no longer needed. To log out is to close off one's access to a computer system after having previously logged in." [Login. Wikipedia]
The event-driven process chain (EPC) flowchart example "Login and registration processing" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Event-driven Process Chain Diagrams solution from the Business Processes area of ConceptDraw Solution Park.
 Entity-Relationship Diagram (ERD)
Entity-Relationship Diagram (ERD)
Entity-Relationship Diagram (ERD) solution extends ConceptDraw DIAGRAM software with templates, samples and libraries of vector stencils from drawing the ER-diagrams by Chen's and crow’s foot notations.
 Basic EPC Diagrams
Basic EPC Diagrams
The Event-driven Process Chain Diagrams solution extends ConceptDraw DIAGRAM software with EPC templates, samples, and vector shape library for the drawing of EPC diagrams.
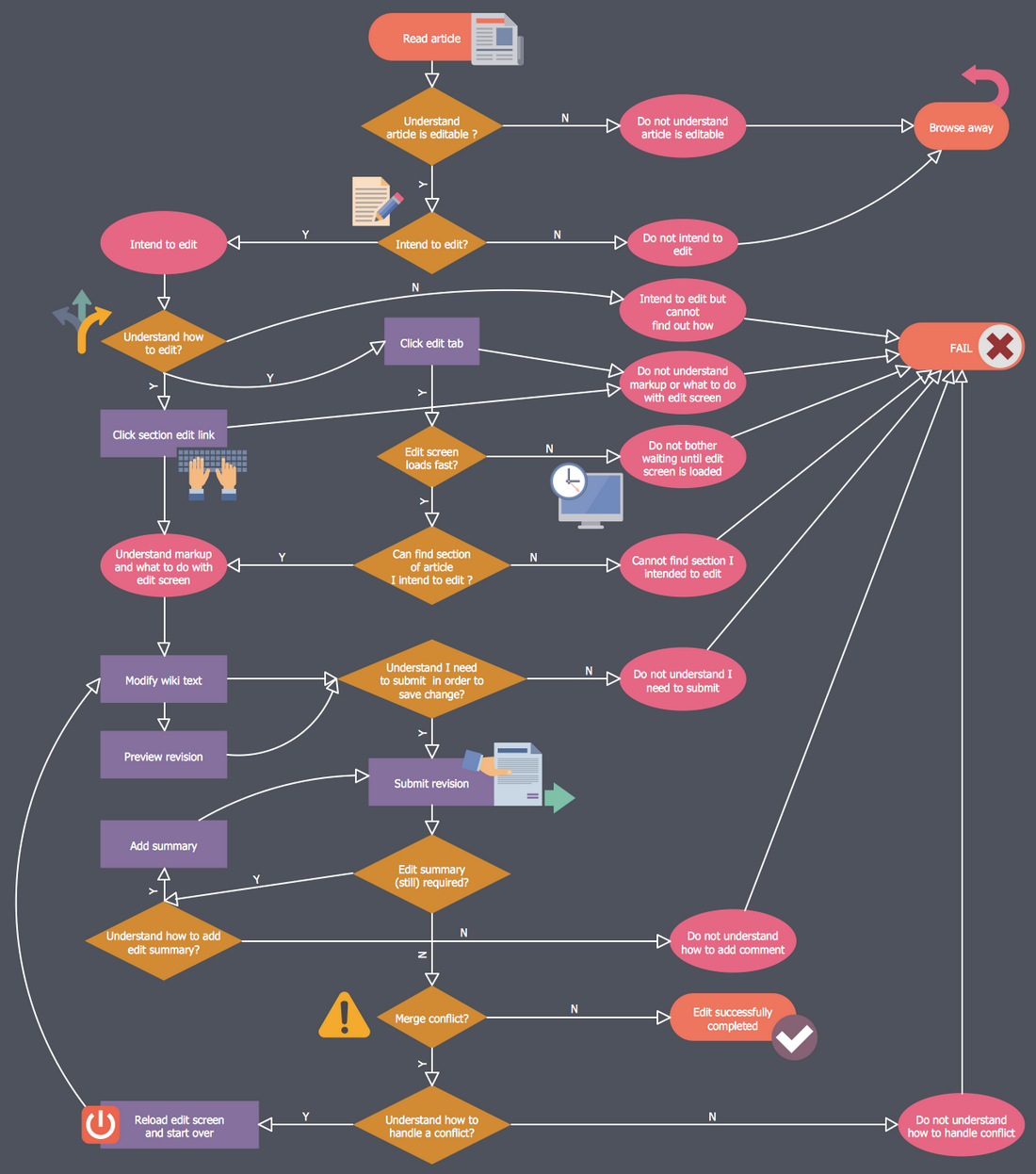
Contoh Flowchart
The Flowcharts are graphical representations of algorithms, processes or step-by-step solutions problems. There are many different types of Flowcharts, among them Process Flowchart, Cross Functional Flowchart, Data Flow Diagram, IDEF Flowchart, Workflow Diagram, Contoh Flowchart and many others. They have especial value when you need represent a complex process, depict in details the process of solution problems, efficiently plan and set the tasks priorities. The Flowcharts must to be constructed brief, clear and logical, simplifying the process or procedure, and making easier the comprehension and perception of information. The ConceptDraw DIAGRAM software makes the process of creating the flowcharts of any types well organized and clear for developers and customers also, including the Contoh Flowchart. It is possible due to the Flowcharts solution from ConceptDraw Solution Park, its predesigned vector objects, templates, and a lot of professional-looking practical samples and examples which can be quick and easy modified, printed, or published on web.
 Entity-Relationship Diagram (ERD)
Entity-Relationship Diagram (ERD)
An Entity-Relationship Diagram (ERD) is a visual presentation of entities and relationships. That type of diagrams is often used in the semi-structured or unstructured data in databases and information systems. At first glance ERD is similar to a flowch
 ConceptDraw Solution Park
ConceptDraw Solution Park
ConceptDraw Solution Park collects graphic extensions, examples and learning materials
 Business Process Workflow Diagrams
Business Process Workflow Diagrams
The Business Process Workflow Diagrams solution enhances the ConceptDraw DIAGRAM functionality with predesigned examples, samples and a numerous collection of predesigned vector objects of workflow chart elements, icons, arrows, connectors, and varied wor
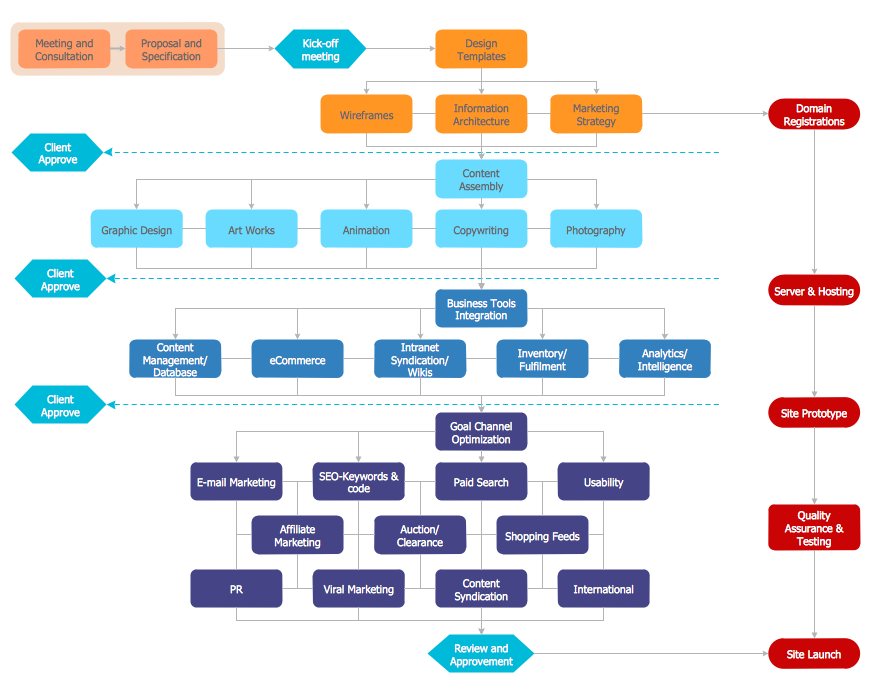
Business Process Workflow Diagram
Business Process Workflow Diagram is a professional visual tool that is widely applied for business development, business analysis, business process optimization and documenting business processes. Business Process Workflow Diagram lets depict in details the steps of business processes and flow of tasks between them, the execution of business processes, transfer of data and documents. The workflows on the Business Process Workflow Diagram are represented using the set of common symbols which let easy illustrate business processes and process flows, depict the start, all major steps and end of the process, what data are used by the process, how the data flow through the business areas within scope of our project, how the tasks are executed and by who, and how workers interact with each other.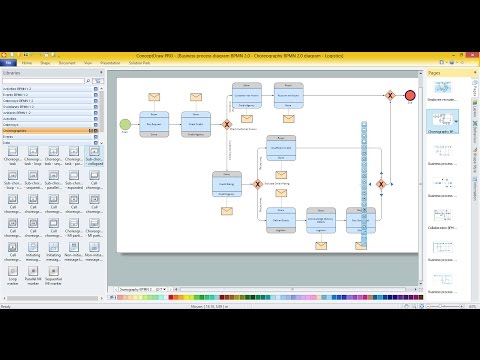
 ConceptDraw Dashboard for Facebook
ConceptDraw Dashboard for Facebook
ConceptDraw Dashboard for Facebook solution extends ConceptDraw DIAGRAM software with a dynamically updated visual dashboard, which shows lifetime total likes, daily friends of fans, and daily page views, information you can receive from Facebook Insights.
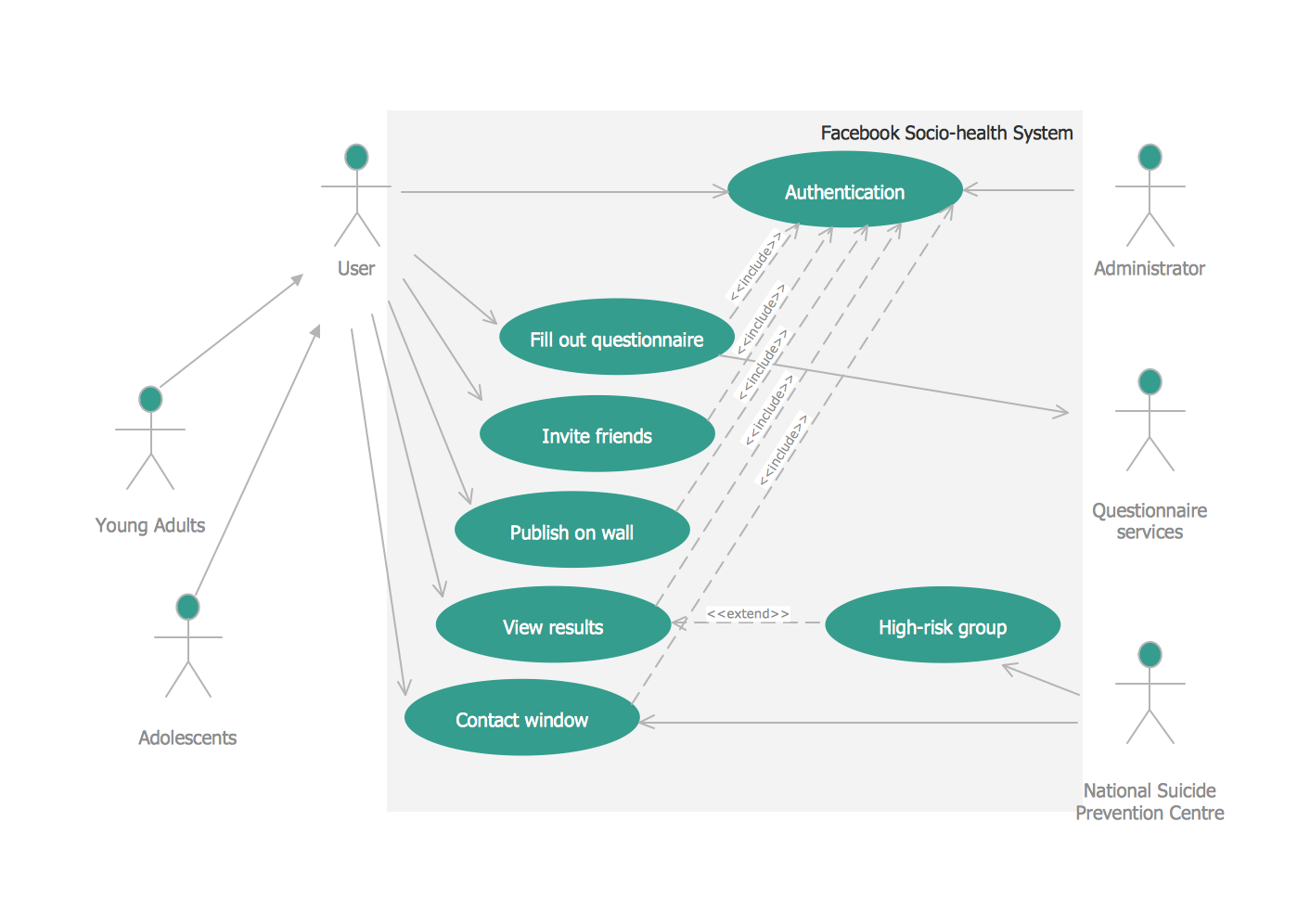
UML Use Case Diagram Example. Social Networking Sites Project
UML Diagrams Social Networking Sites Project. This sample was created in ConceptDraw DIAGRAM diagramming and vector drawing software using the UML Use Case Diagram library of the Rapid UML Solution from the Software Development area of ConceptDraw Solution Park. This sample shows the Facebook Socio-health system and is used at the projection and creating of the social networking sites.The vector clipart library Access and security contains 17 images of access control and security system equipment.
"In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.
Locks and login credentials are two analogous mechanisms of access control. ...
The term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons. Physical access control can be achieved by a human (a guard, bouncer, or receptionist), through mechanical means such as locks and keys, or through technological means such as access control systems like the mantrap. Within these environments, physical key management may also be employed as a means of further managing and monitoring access to mechanically keyed areas or access to certain small assets." [Access control. Wikipedia]
Use the vector stencils library Access and security to draw illustrations and diagrams of safety and security system equipment using the ConceptDraw PRO diagramming and vector drawing software.
The clipart example "Design elements - Access and security" is included in the Safety and Security solution from the Illustration area of ConceptDraw Solution Park.
"In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.
Locks and login credentials are two analogous mechanisms of access control. ...
The term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons. Physical access control can be achieved by a human (a guard, bouncer, or receptionist), through mechanical means such as locks and keys, or through technological means such as access control systems like the mantrap. Within these environments, physical key management may also be employed as a means of further managing and monitoring access to mechanically keyed areas or access to certain small assets." [Access control. Wikipedia]
Use the vector stencils library Access and security to draw illustrations and diagrams of safety and security system equipment using the ConceptDraw PRO diagramming and vector drawing software.
The clipart example "Design elements - Access and security" is included in the Safety and Security solution from the Illustration area of ConceptDraw Solution Park.
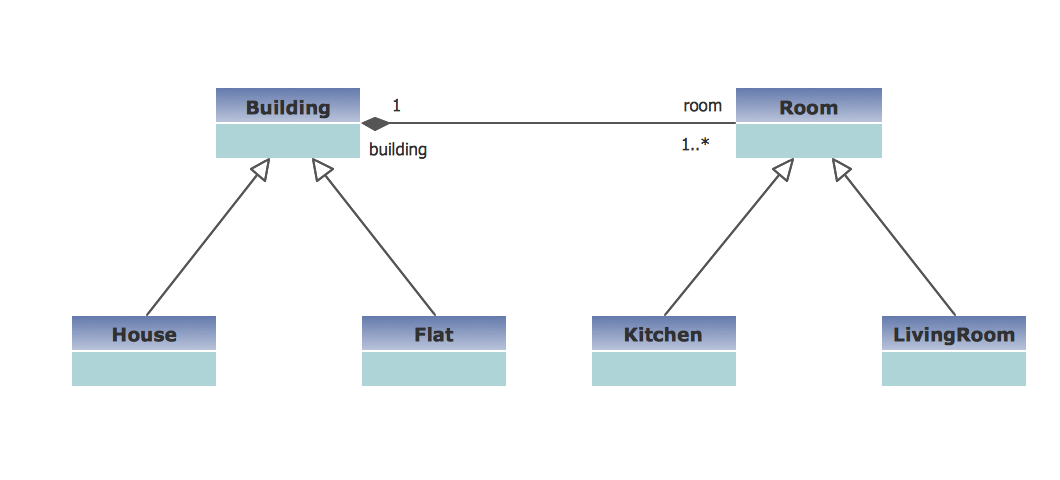
UML Class Diagram Example - Buildings and Rooms
This sample was created in ConceptDraw DIAGRAM diagramming and vector drawing software using the UML Class Diagram library of the Rapid UML Solution from the Software Development area of ConceptDraw Solution Park. This sample shows the structure of the building and can be used by building companies, real estate agencies, at the buying / selling of the realty.This vector stencils library contains 184 round icons.
Use it to design cloud computing infographics and diagrams with ConceptDraw PRO software.
"Though service-oriented architecture advocates "everything as a service" (with the acronyms EaaS or XaaS or simply aas), cloud-computing providers offer their "services" according to different models, which happen to form a stack: infrastructure-, platform- and software-as-a-service.
Infrastructure as a service (IaaS)
In the most basic cloud-service model ... providers of IaaS offer computers — physical or (more often) virtual machines — and other resources. IaaS refers to online services that abstract the user from the details of infrastructure like physical computing resources, location, data partitioning, scaling, security, backup etc.
Platform as a service (PaaS)
PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a computing platform, typically including operating system, programming-language execution environment, database, and web server. Application developers can develop and run their software solutions on a cloud platform without the cost and complexity of buying and managing the underlying hardware and software layers.
Software as a service (SaaS)
In the software as a service (SaaS) model, users gain access to application software and databases. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee.
In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability — which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand." [Cloud computing. Wikipedia]
The vector stencils library "Cloud round icons" is included in the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
Use it to design cloud computing infographics and diagrams with ConceptDraw PRO software.
"Though service-oriented architecture advocates "everything as a service" (with the acronyms EaaS or XaaS or simply aas), cloud-computing providers offer their "services" according to different models, which happen to form a stack: infrastructure-, platform- and software-as-a-service.
Infrastructure as a service (IaaS)
In the most basic cloud-service model ... providers of IaaS offer computers — physical or (more often) virtual machines — and other resources. IaaS refers to online services that abstract the user from the details of infrastructure like physical computing resources, location, data partitioning, scaling, security, backup etc.
Platform as a service (PaaS)
PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a computing platform, typically including operating system, programming-language execution environment, database, and web server. Application developers can develop and run their software solutions on a cloud platform without the cost and complexity of buying and managing the underlying hardware and software layers.
Software as a service (SaaS)
In the software as a service (SaaS) model, users gain access to application software and databases. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee.
In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability — which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand." [Cloud computing. Wikipedia]
The vector stencils library "Cloud round icons" is included in the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
The vector stencils library "Cybersecurity" contains 24 cybersecurity icons.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
- Login and registration processing - EPC diagram | Flowchart ...
- Flowchart | Business process Flow Chart - Event-Driven Process ...
- How to Create a Network Security Diagram Using ConceptDraw ...
- Login and registration processing - EPC diagram | Basic Flowchart ...
- Login and registration processing - EPC diagram | Restricted Area ...
- Login and registration processing - EPC diagram | Flowchart ...
- Flowchart | Login and registration processing - EPC diagram ...
- EPC diagram - Login and registration processing | Logon Process ...
- Flowchart | Login and registration processing - EPC diagram ...
- Network Security | How to Create a Network Security Diagram Using ...
- Simple Diagrams Free
- UML activity diagram - User registration | Account Flowchart ...
- Network Security Diagrams | Network Security Tips | How to Create ...
- Network Security Devices | Cybersecurity - Vector stencils library ...
- Network diagrams with ConceptDraw PRO | AWS Architecture ...
- User Registration Login Process Diagram
- Intranet Simple Diagrams
- ConceptDraw Solution Park | Design elements - Access and security ...
- Network Security Devices | Cyber Security Degrees | Network ...
- UML Use Case Diagram Example Registration System | UML activity ...