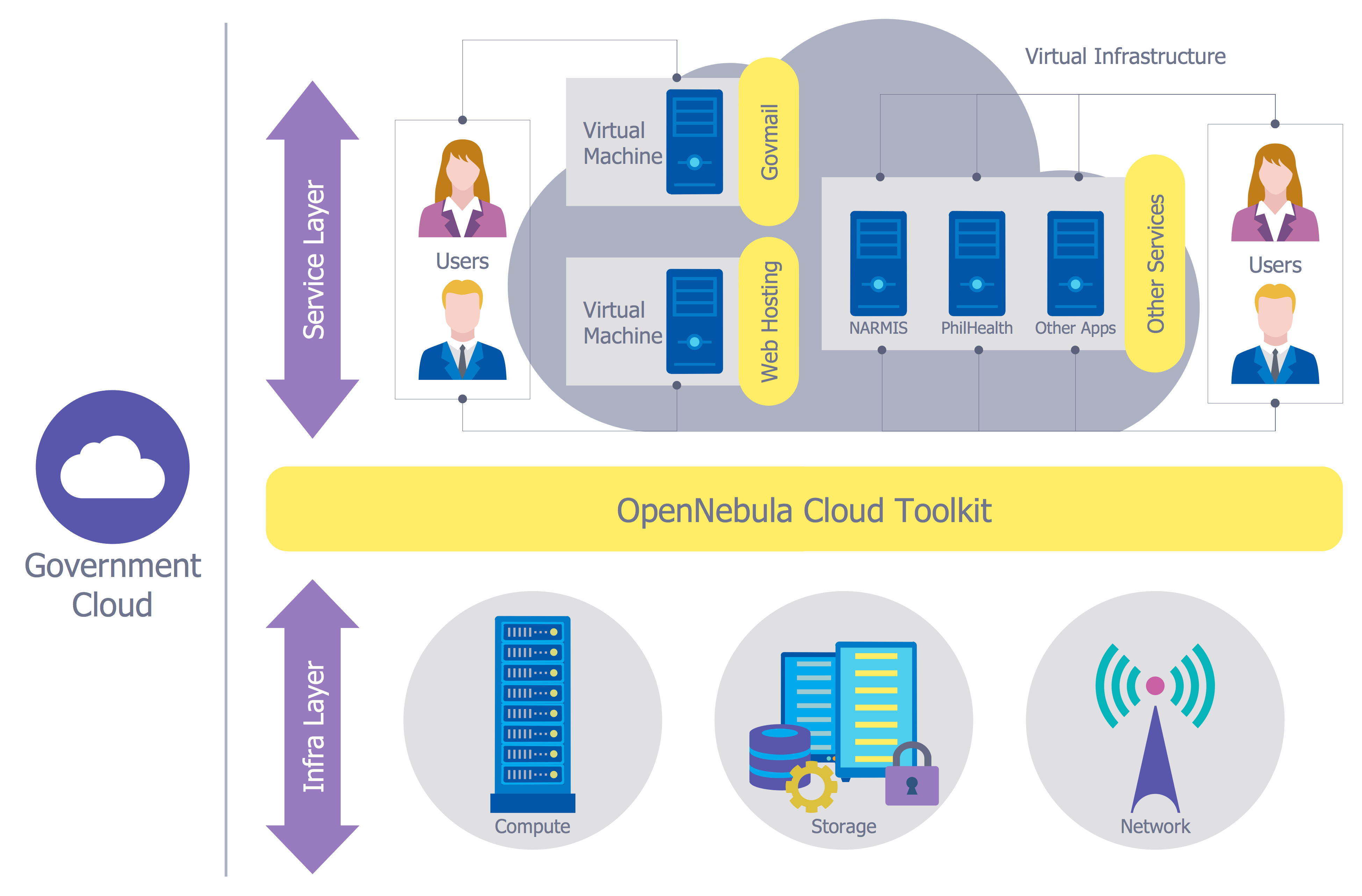
Network Security Model
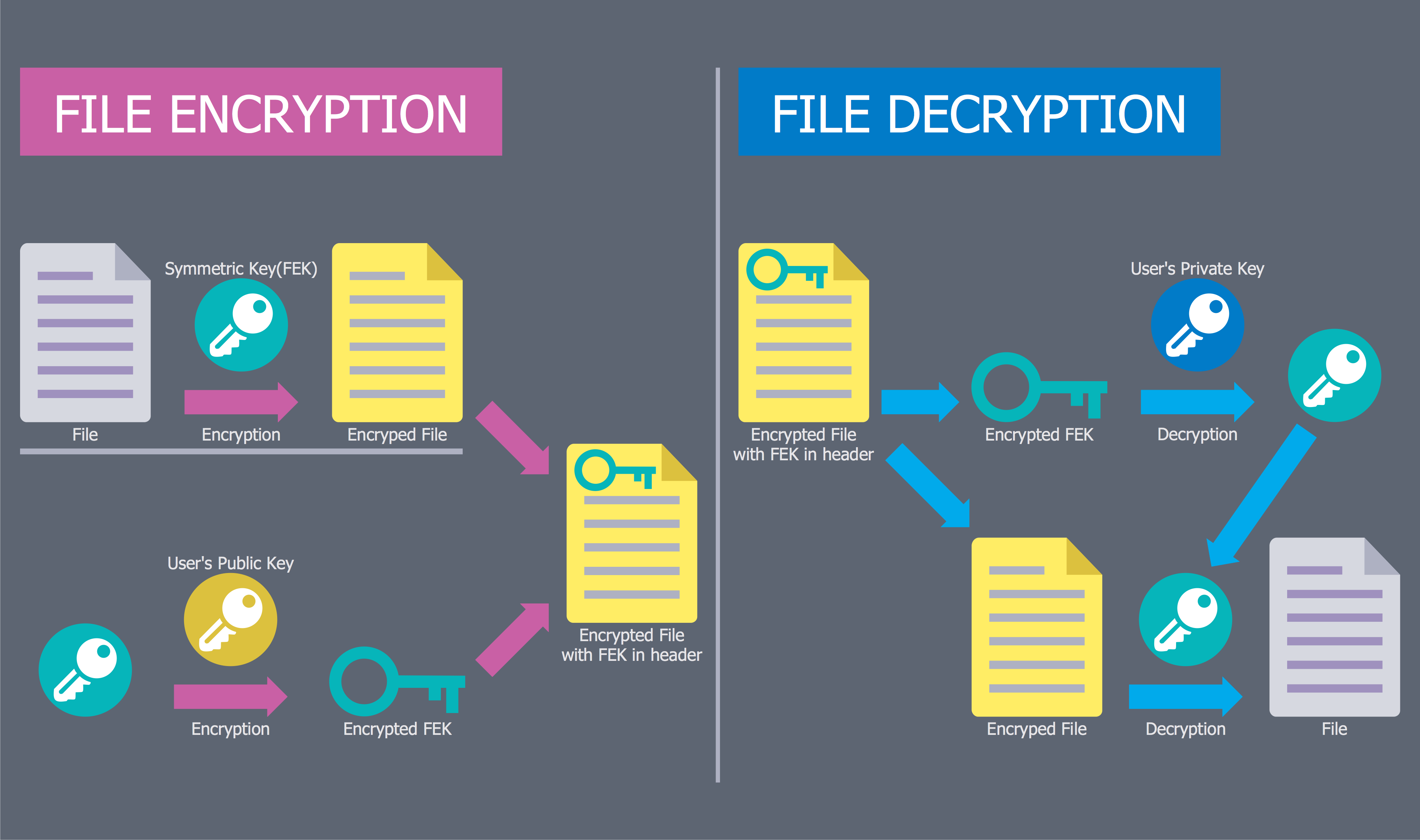
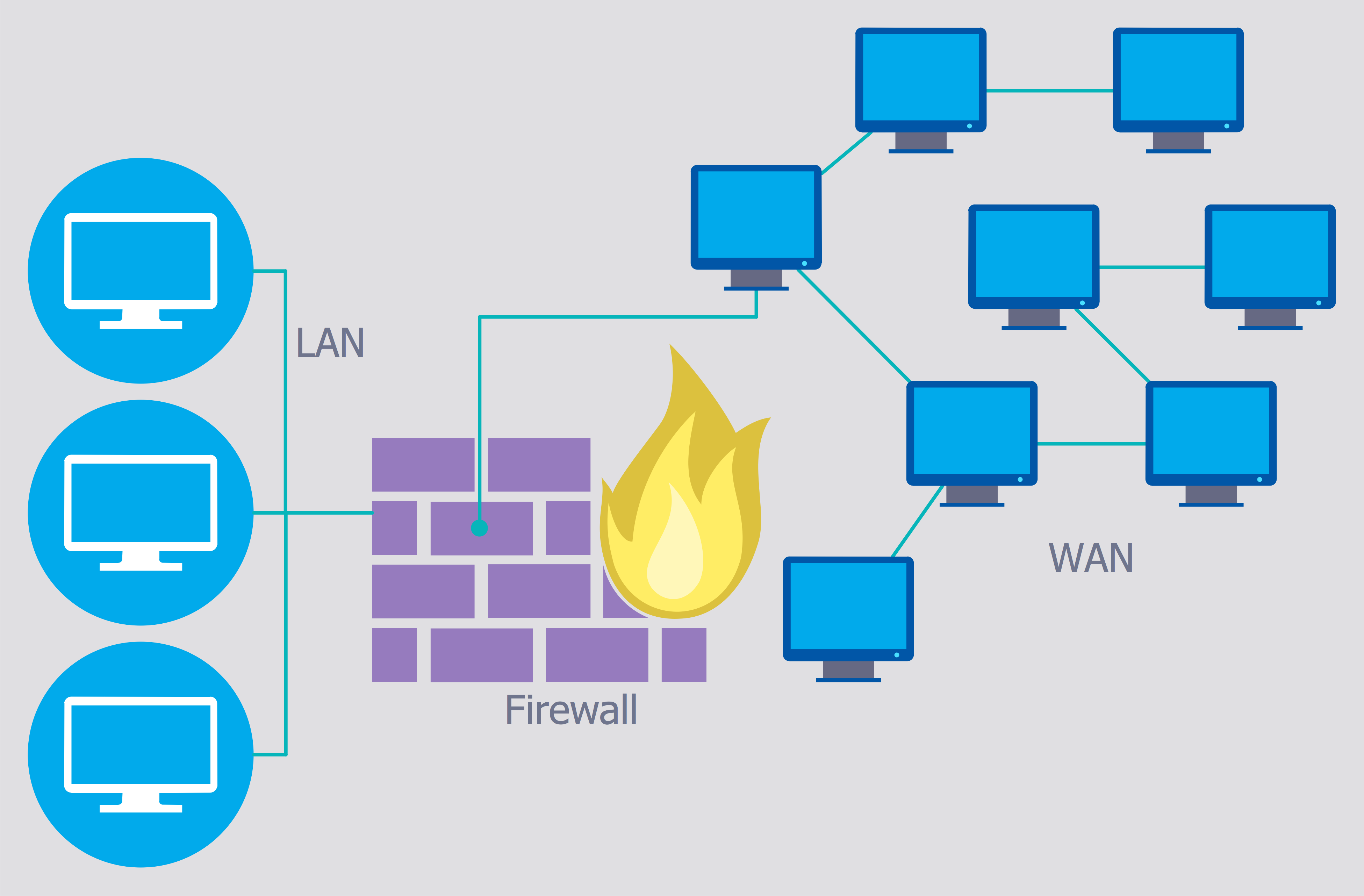
Creation of well thought-out network security model will effectively help you in realization your network's security. ConceptDraw PRO diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.Network Security Diagram
ConceptDraw PRO diagramming and vector drawing software enhanced with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is the best for effective design professional, colorful and attractive Network Security Diagram of any complexity and degree of detailing.Secure Wireless Network
Use the ConceptDraw PRO diagramming and vector drawing software enhanced with powerful tools of Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park to effectively visualize the importance of network security and wireless network security, and ways to ensure them, to easily design Network Security Diagrams and Maps, Network Security Model, Secure Wireless Network and Network Security Architecture diagrams.Cyber Security Degrees
For protection various cyber environments are developed and applied large variety of cyber security standards, techniques, security concepts and approaches with different cyber security degrees. The ConceptDraw PRO diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park offers the number of useful tools which will help network security engineers, cyber security specialists, network and computer analysts easily and visually depict the knowledge and skills for research and prevention of intrusions, about protection critical information and analysis of cyber incidents, and for how to assess threats and vulnerabilities.- Network Security Model | Secure Wireless Network | Network ...
- Network Security Model | Network Security Diagram | Secure ...
- Network Security Diagrams | How to Create a Network Security ...
- How to Create a Network Security Diagram Using ConceptDraw PRO
- Network Security Model | Network Security Diagrams | Download ...
- Network Security Diagrams | | Network Security Model | Computer ...
- Cyber Security Degrees | Network Security Diagrams | Network ...
- Network Security Diagram
- Network Security Diagram | Network Security | How to Create a ...
- Network Security Diagrams | Network Security Model | Cisco security ...
- Cyber Security Degrees | Network Security Diagrams | IT Security ...
- Network Security Devices | Cisco Network Design. Cisco icons ...
- Network Security Model | Cyber Security Degrees | Network Security ...
- ConceptDraw PRO Network Diagram Tool | Network Security ...
- Network Security | Network Security Model | ConceptDraw PRO ...
- Network Security Diagrams | Cisco Network Diagrams | Network ...
- ConceptDraw PRO Network Diagram Tool | Network Security ...
- Secure Wireless Network | Network Security Model | Network ...
- Network Security Diagrams | IT Security Solutions | Network Security ...
- Network Security Diagrams | Network Security | How to Create a ...