"Targeted advertising is a type of advertising whereby advertisements are placed so as to reach consumers based on various traits such as demographics, psychographics, behavioral variables (such as product purchase history), and firmographic variables ... or other second-order activities which serve as a proxy for these traits.
Most targeted new media advertising currently uses second-order proxies for targeting, such as tracking online or mobile web activities of consumers, associating historical webpage consumer demographics with new consumer web page access, using a search word as the basis for implied interest, or contextual advertising.
Addressable advertising systems serve ads directly based on demographic, psychographic, or behavioral attributes associated with the consumer(s) exposed to the ad. These systems are always digital and must be addressable in that the end point which serves the ad (set-top box, website, or digital sign) must be capable of rendering an ad independently of any other end points based on consumer attributes specific to that end point at the time the ad is served. Addressable advertising systems therefore must use consumer traits associated with the end points as the basis for selecting and serving ads." [Targeted advertising. Wikipedia]
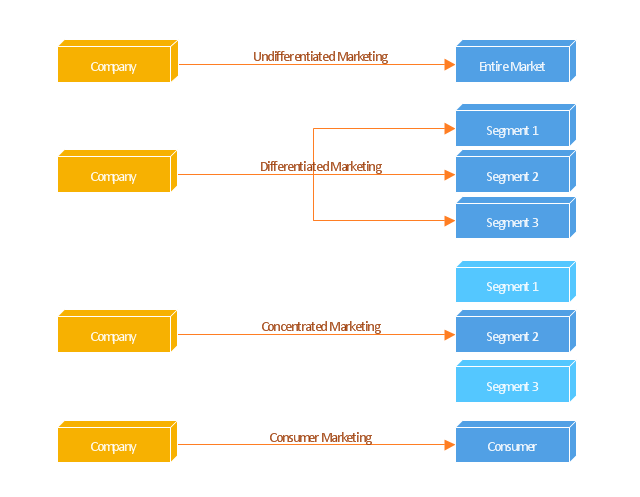
The block diagram example "Marketing targeting" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Block Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
Most targeted new media advertising currently uses second-order proxies for targeting, such as tracking online or mobile web activities of consumers, associating historical webpage consumer demographics with new consumer web page access, using a search word as the basis for implied interest, or contextual advertising.
Addressable advertising systems serve ads directly based on demographic, psychographic, or behavioral attributes associated with the consumer(s) exposed to the ad. These systems are always digital and must be addressable in that the end point which serves the ad (set-top box, website, or digital sign) must be capable of rendering an ad independently of any other end points based on consumer attributes specific to that end point at the time the ad is served. Addressable advertising systems therefore must use consumer traits associated with the end points as the basis for selecting and serving ads." [Targeted advertising. Wikipedia]
The block diagram example "Marketing targeting" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Block Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
"Targeted advertising is a type of advertising whereby advertisements are placed so as to reach consumers based on various traits such as demographics, psychographics, behavioral variables (such as product purchase history), and firmographic variables ... or other second-order activities which serve as a proxy for these traits.
Most targeted new media advertising currently uses second-order proxies for targeting, such as tracking online or mobile web activities of consumers, associating historical webpage consumer demographics with new consumer web page access, using a search word as the basis for implied interest, or contextual advertising.
Addressable advertising systems serve ads directly based on demographic, psychographic, or behavioral attributes associated with the consumer(s) exposed to the ad. These systems are always digital and must be addressable in that the end point which serves the ad (set-top box, website, or digital sign) must be capable of rendering an ad independently of any other end points based on consumer attributes specific to that end point at the time the ad is served. Addressable advertising systems therefore must use consumer traits associated with the end points as the basis for selecting and serving ads." [Targeted advertising. Wikipedia]
The block diagram example "Marketing targeting" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Block Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
Most targeted new media advertising currently uses second-order proxies for targeting, such as tracking online or mobile web activities of consumers, associating historical webpage consumer demographics with new consumer web page access, using a search word as the basis for implied interest, or contextual advertising.
Addressable advertising systems serve ads directly based on demographic, psychographic, or behavioral attributes associated with the consumer(s) exposed to the ad. These systems are always digital and must be addressable in that the end point which serves the ad (set-top box, website, or digital sign) must be capable of rendering an ad independently of any other end points based on consumer attributes specific to that end point at the time the ad is served. Addressable advertising systems therefore must use consumer traits associated with the end points as the basis for selecting and serving ads." [Targeted advertising. Wikipedia]
The block diagram example "Marketing targeting" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Block Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
 Block Diagrams
Block Diagrams
Block diagrams solution extends ConceptDraw PRO software with templates, samples and libraries of vector stencils for drawing the block diagrams.
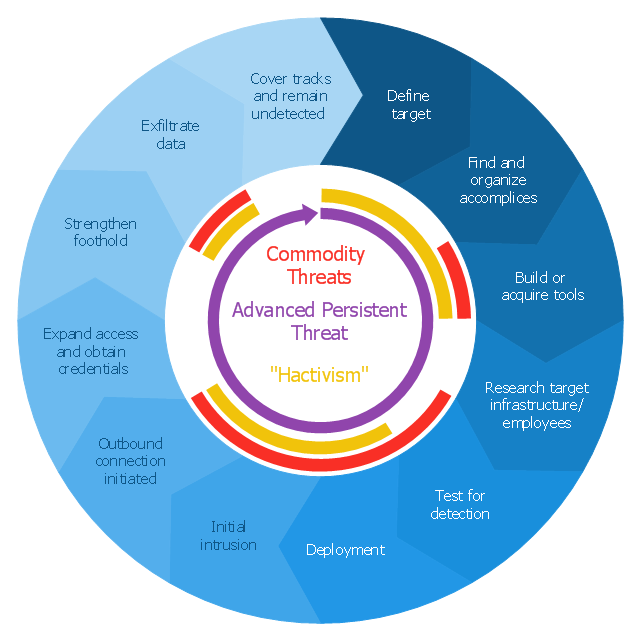
This circular arrows diagram sample shows advanced persistent threat lifecycle.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
- Marketing Diagrams | Marketing Analysis Diagram | Block diagram ...
- Marketing Diagrams | Target and Circular Diagrams | Block diagram ...
- Diagram Of Targeted Marketing
- Target Diagram | Target and Circular Diagrams | Block diagram ...
- Block diagram - Marketing targeting | Venn diagram - Internet ...
- Block diagram - Marketing targeting
- Pyramid Diagram | Block diagram - Marketing targeting | Time ...
- Marketing Diagrams | Marketing mix - Wheel diagram | Block ...
- Block diagram - Marketing targeting | Targeted Advertising
- Pyramid Diagram | Block diagram - Marketing targeting | Time ...
- Block diagram - Marketing targeting | Block diagram - Six markets ...
- Block diagram - Marketing targeting | Competing consumers pattern ...
- Advertising creation process - Conversation BPMN 2.0 diagram ...
- ConceptDraw Solution Park | Flow Chart Online | Block diagram ...
- ConceptDraw Solution Park | Block diagram - Marketing targeting ...
- Marketing Diagrams | Target and Circular Diagrams | Marketing ...
- Block diagram - Marketing targeting | Design elements ...
- Marketing mix - Wheel diagram | Marketing mix diagram | Target ...
- Circle-spoke diagram - Target market | Target market - Onion ...
- Marketing Diagrams | Marketing | Target and Circular Diagrams ...
- ERD | Entity Relationship Diagrams, ERD Software for Mac and Win
- Flowchart | Basic Flowchart Symbols and Meaning
- Flowchart | Flowchart Design - Symbols, Shapes, Stencils and Icons
- Flowchart | Flow Chart Symbols
- Electrical | Electrical Drawing - Wiring and Circuits Schematics
- Flowchart | Common Flowchart Symbols
- Flowchart | Common Flowchart Symbols